@SignOfficial I was at my desk just after 7 a.m. with coffee cooling beside a legal pad when I reread a line from Sign’s docs about inspection-ready evidence. That phrase stayed with me because I keep seeing digital systems promise speed before they earn confidence and I keep wondering what really holds when pressure arrives.
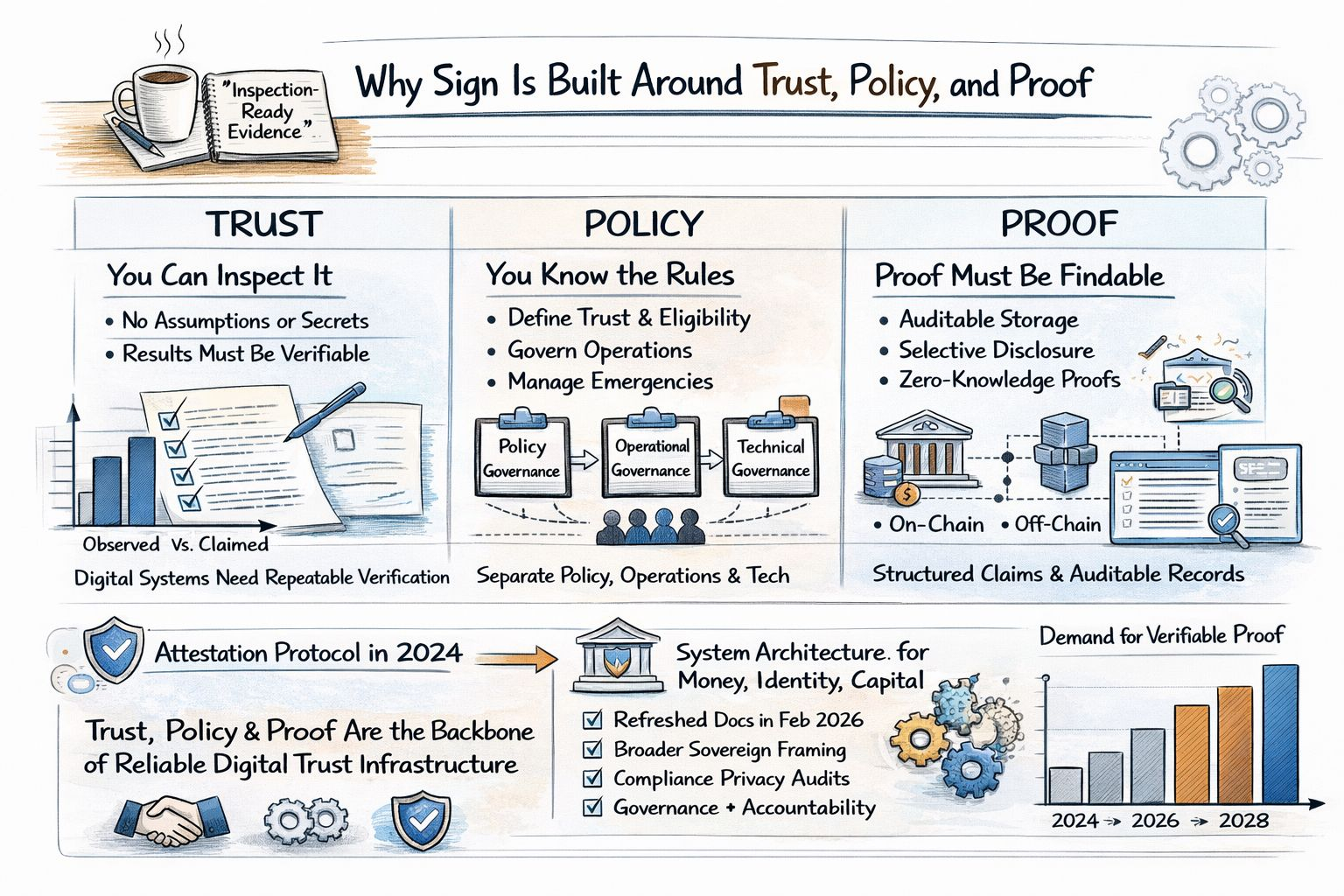
I think that question explains why Sign has started to attract more attention now. In 2025 the project moved from being discussed mainly as an attestation protocol toward a broader system architecture for money identity and capital. Its documentation was refreshed again in February 2026 around that sovereign framing. Around the same period policy pressure on stablecoins and digital asset infrastructure intensified across many jurisdictions which made any system that could show compliance privacy controls and auditable records feel more relevant than it did even a year earlier.
What I find most sensible in Sign’s design is that it does not treat trust as a mood but as something I should be able to inspect. The project’s own language is pretty plain about this because older systems often relied on relationships and institutional familiarity while digital systems that stretch across agencies vendors chains and storage layers need repeatable verification. That idea lands with me because the weak point in modern infrastructure is often not computation but interpretation since two parties can look at the same event while only one can prove what happened under whose authority and whether that fact is still valid.
That is where policy enters the picture and I think this is the part many technical projects gloss over. Sign’s current architecture separates policy governance operational governance and technical governance. I read that less as bureaucracy and more as realism because a money rail an identity system or a benefits program cannot run on code alone. Someone still has to define eligibility rules privacy levels incident handling upgrades emergency controls and who is actually authorized to act. Sign seems built on the assumption that these questions should not sit off to the side as messy human exceptions because they belong in the system design from the start.
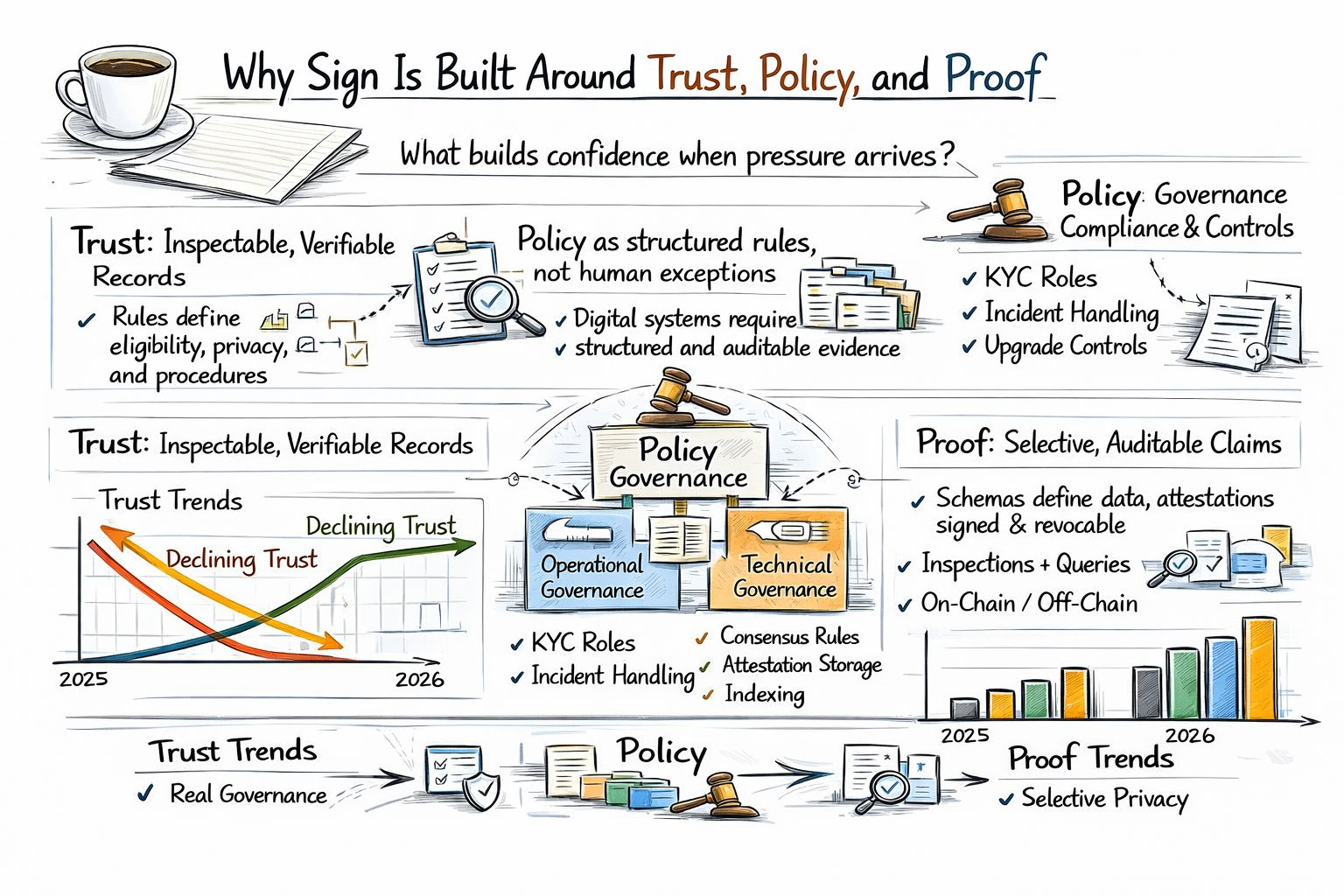
I also think the emphasis on proof is more practical than philosophical. In Sign’s model attestations are structured signed claims tied to schemas with evidence revocation and querying built into the workflow. That sounds technical but the plain meaning is simple because I can check a claim later without relying on memory screenshots or a vendor’s private dashboard. The protocol supports on-chain off-chain and hybrid storage along with indexing through SignScan which matters because proof is only useful if it is still findable when an auditor regulator partner or citizen needs it months later.
What makes this feel timely rather than theoretical is the way privacy and proof are being asked to coexist. Sign’s whitepaper describes selective disclosure unlinkability and zero-knowledge proofs as core features for identity and compliance workflows. I pay attention to that because the old tradeoff was always framed too crudely as if the only options were to reveal everything for compliance or reveal too little to be trusted. Systems like this are trying to narrow that gap so I can prove age eligibility or authorization without handing over my whole file every time which is a much more serious idea than the usual talk about putting identity on-chain.
I’m also persuaded by the quieter examples more than the grand ones. Sign points to a proof-of-audit use case where an audit summary is recorded as an attestation and to KYC-gated contract calls where eligibility and sanctions checks can be communicated in a verifiable way. These are not glamorous stories and that is exactly why I take them seriously because they show the project working where disputes actually happen in audits permissions claims and access. Real trust infrastructure usually looks a little boring up close and I think that is often a good sign.
When I step back I do not see Sign mainly as a crypto brand trying to sound institutional. I see an attempt to build administrative memory for digital systems that have become too important to run on informal trust. That is why the combination of trust policy and proof feels coherent to me because trust tells me what must be believable while policy tells me who sets the rules and proof tells me what survives scrutiny. I do not think that solves every governance problem but it does make evasions harder and in a period when digital money credentials and public-facing systems are all getting more regulated and more connected that order seems less like branding and more like basic discipline.