@MidnightNetwork If you’ve followed blockchain privacy for any length of time, you’ve probably heard the pitch: “Zero-knowledge proofs will change everything.” But most projects deliver either total opacity (great for cypherpunks, terrible for real-world utility) or leaky half-measures that still expose far too much. Midnight Network does neither. Its zk-SNARKs aren’t a bolted-on feature or a marketing checkbox—they’re the architectural spine of the entire system, engineered for what the team calls “rational privacy”: the ability to prove exactly what needs proving, hide everything else, and still compose, interoperate, and scale like a modern smart-contract platform.I spent weeks poring through the official documentation, the Kachina whitepaper origins, the 2025 proving-system upgrade notes, and developer discussions to understand how this actually works under the hood. What emerges isn’t magic. It’s meticulous cryptographic engineering layered on top of a dual-state ledger and a developer-friendly DSL. Here’s the deep dive.First, the zk-SNARK Primer (Because We Need It)A zero-knowledge succinct non-interactive argument of knowledge (zk-SNARK) lets a prover convince a verifier that they know a secret “witness” satisfying a set of mathematical constraints—without revealing the witness or requiring back-and-forth chatter.The flow is always the same:Setup — Generate public parameters (a structured reference string). Midnight uses a universal setup via BLS12-381, avoiding per-circuit ceremonies. 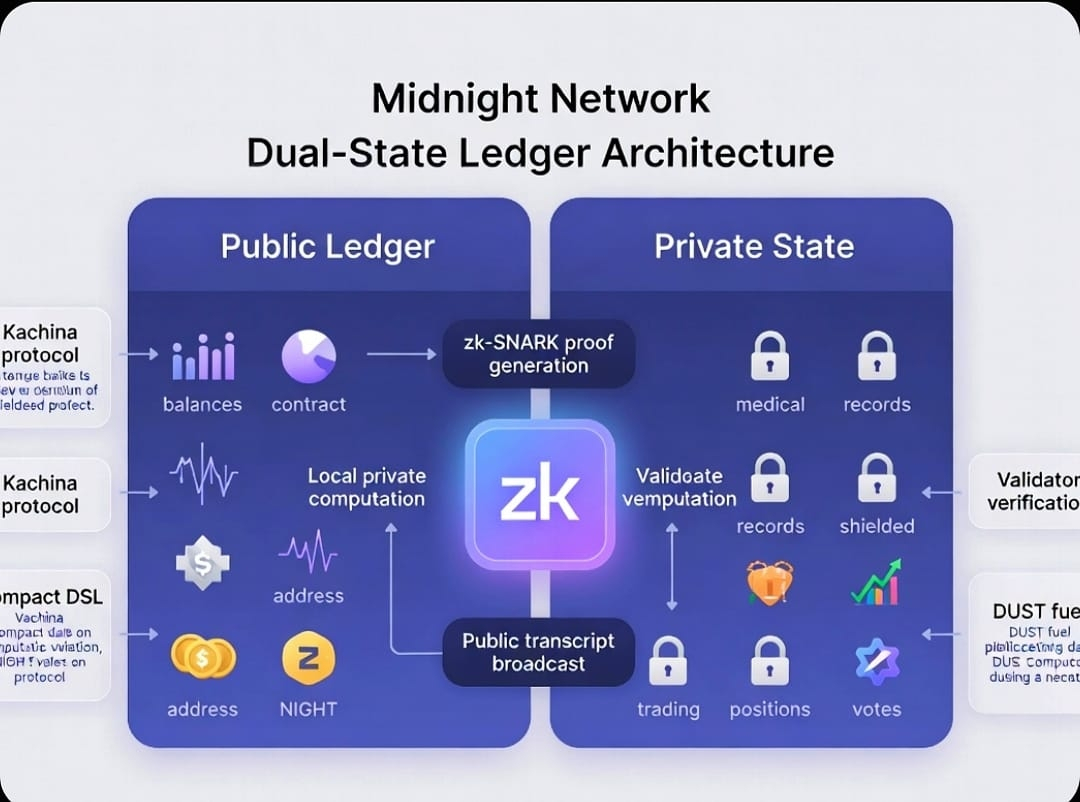
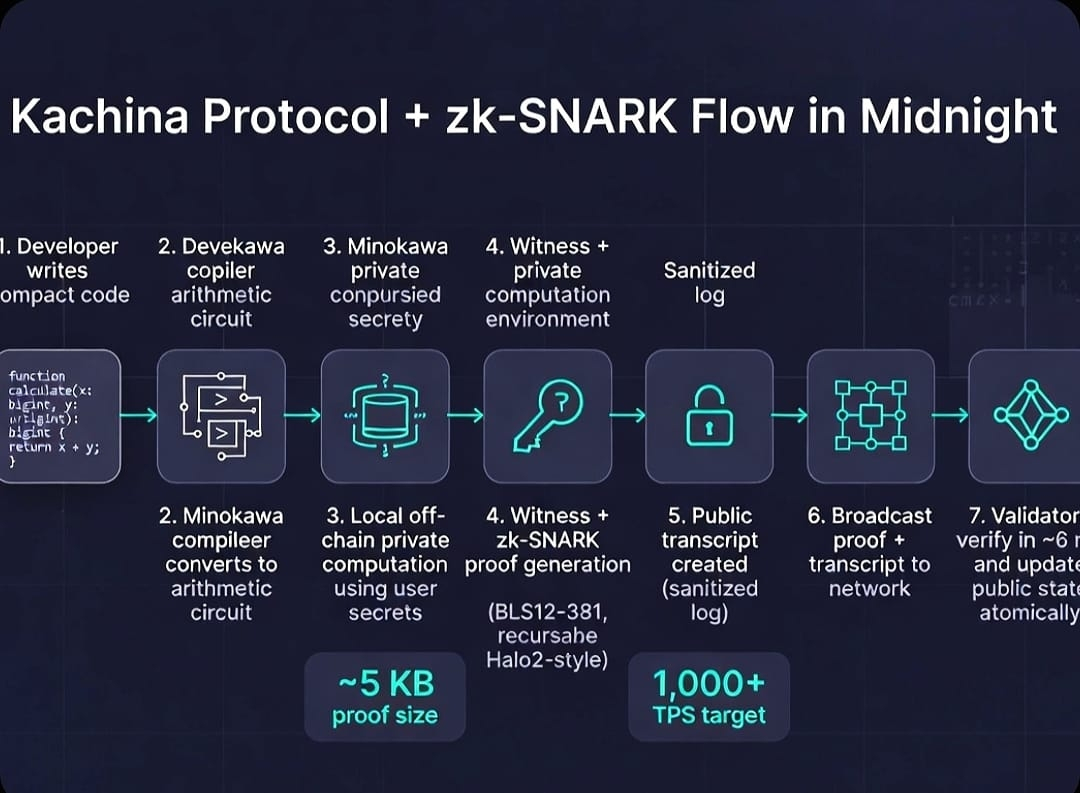
Circuit construction — Translate your program logic into an arithmetic circuit: gates that enforce addition, multiplication, equality checks, range proofs, etc.
Witness + Proof generation (off-chain) — Plug in the private inputs. The prover machine crunches polynomials and elliptic-curve pairings until it spits out a tiny proof.
Verification (on-chain) — The verifier plugs the public inputs and proof into a fast pairing check. If it passes, the statement is true.
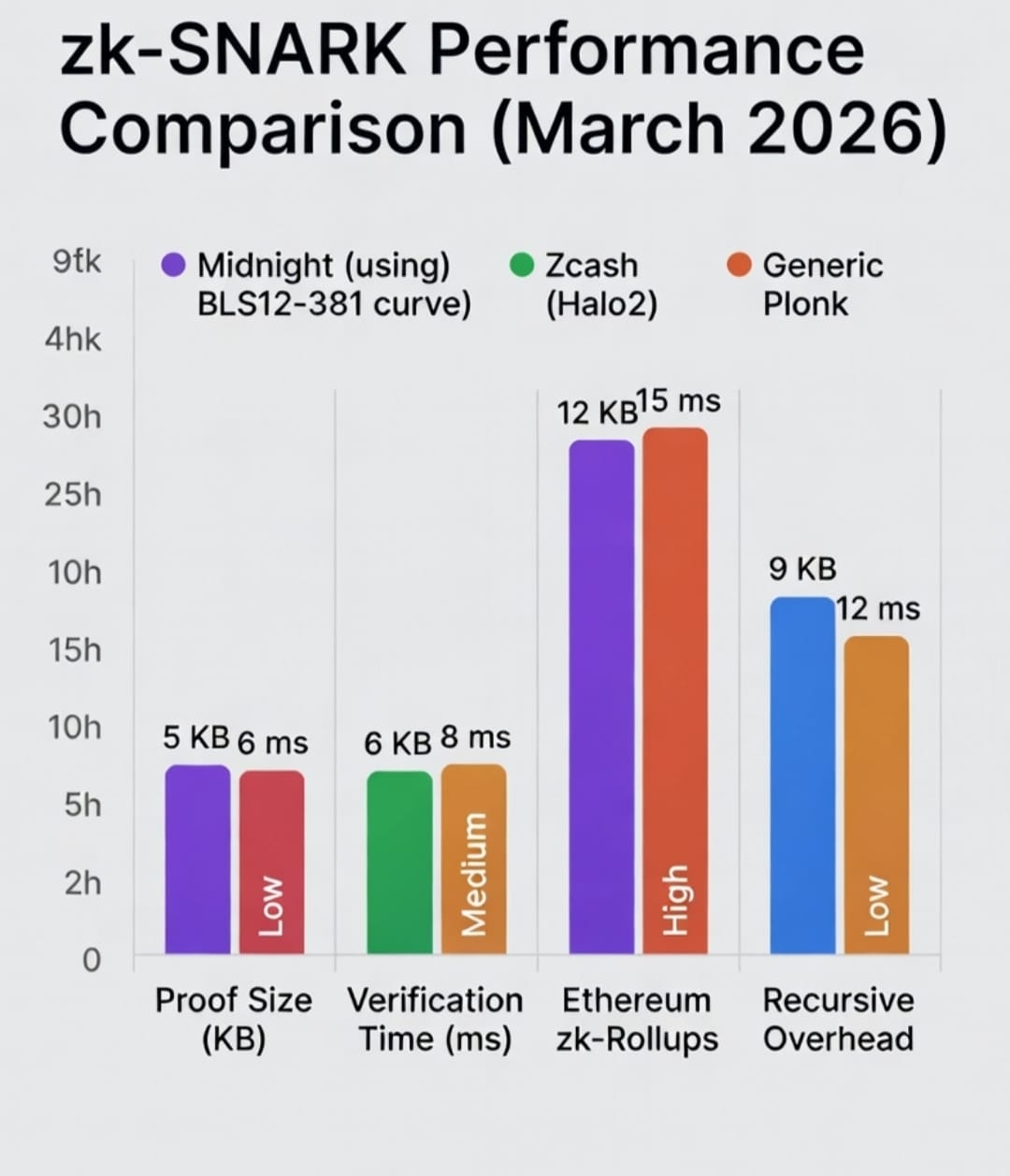
Succinctness is the killer feature: proof size stays sub-linear (often just a few kilobytes) no matter how big the statement gets. Non-interactivity means you generate once and broadcast. Midnight’s proofs are currently ~5 KB with ~6 ms verification time on modern hardware—fast enough for high-throughput chains.Midnight’s Specific Flavor: Halo2-Inspired, BLS12-381, Recursive by DesignMidnight didn’t invent zk-SNARKs, but it made deliberate choices that set it apart.Originally the network used a custom Pluto-Eris curve system. In April 2025, during the Testnet-02 upgrade, the team migrated everything to the industry-standard BLS12-381 elliptic curve. Why? Three reasons that matter deeply:No bespoke trusted setup ceremony—leverage the existing BLS12-381 SRS.
Standard cryptography means better interoperability and fewer “weird crypto” attack surfaces.
Recursion trade-offs flipped in Midnight’s favor: Pluto-Eris gave smaller circuits but punishing CPU costs during recursive composition. BLS12-381 accepts slightly larger circuits for dramatically lower CPU overhead when proofs nest inside other proofs.
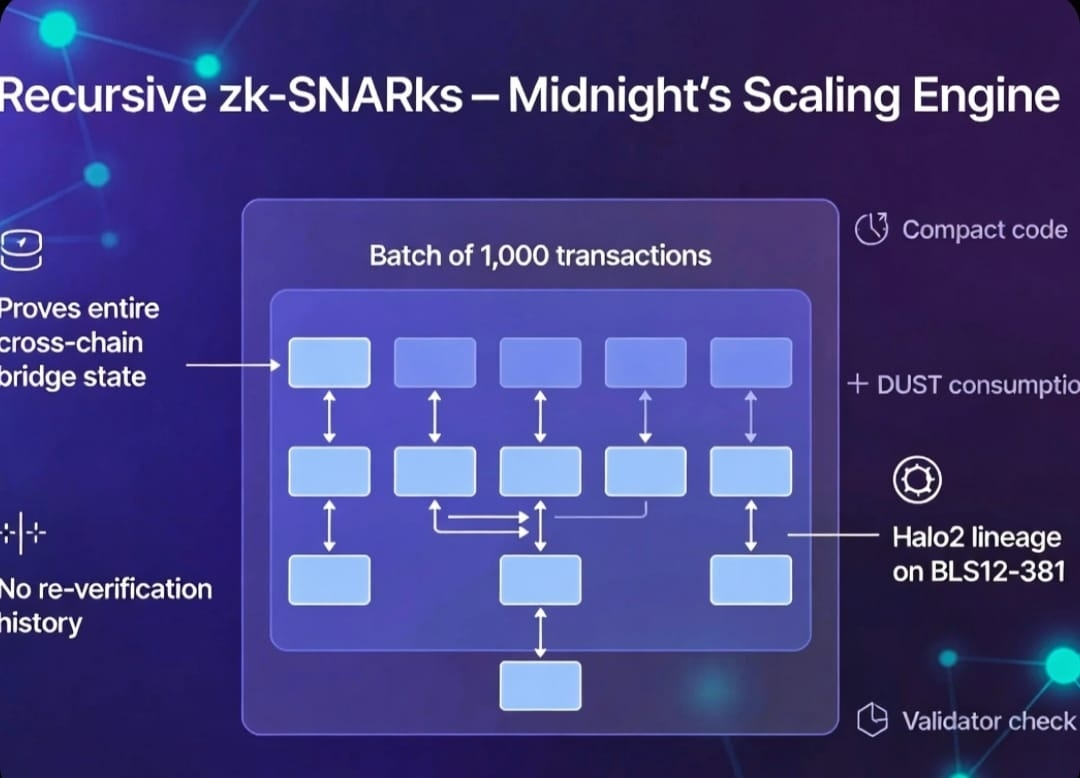
The numbers speak for themselves: verification dropped from ~12 ms to ~6 ms per proof; proof size shrank from 6 KB to 5 KB. That might sound incremental until you realize these proofs are being verified thousands of times per second across a network gunning for 1,000+ TPS with sub-second finality.The underlying proving system is Plonk-derived and explicitly supports recursion—the same Halo2 lineage popularized by Electric Coin Company and Zcash, but tuned for Midnight’s dual-ledger model. Recursion here isn’t a nice-to-have; it’s the scaling engine. You can prove “this private state transition is valid” and then wrap that proof inside a larger proof that attests “a batch of 1,000 such transitions are all valid.” Or prove a cross-chain bridge state without re-verifying the entire history. This is how Midnight keeps private computation composable rather than isolated.Kachina: The Protocol That Makes zk-SNARKs Actually UsefulThe cryptographic engine lives inside the Kachina protocol—the formal foundation for Midnight’s private smart contracts. Kachina (named after a Hopi spirit of life-bringing) is built on the Universally Composable security framework, which is academic-speak for “we proved this composes safely with other cryptographic primitives.”Here’s the genius move: instead of trying to hide the entire blockchain (Monero/Zcash style), Kachina splits the world into two synchronized but separate realities:Public ledger — A deterministic state machine everyone can see and agree on (balances of public tokens, contract addresses, etc.).
Private state — Lives entirely on your local machine. Your medical records, your trading positions, your voting history—never uploaded.
When you want to interact with a contract, you:Compute the new private state locally using your secret data.
Generate a zk-SNARK proof that this private transition obeys the contract rules and produces the correct public state change.
Broadcast only the proof + a public “transcript” (a sanitized log of the operations you performed).
Validators check the proof against the stored verifier key. If it passes, the public state updates atomically. Your secrets never leave your device.Transcripts add another layer of elegance. They record the sequence of reads, assertions, and writes in a way that lets the network reorder conflicting transactions for maximum concurrency without leaking information. Think of them as a public play-by-play that still protects the private script.Smart Contracts in Practice: Compact + Transcripts + Circuit SplittingDevelopers write in Compact—a TypeScript-flavored DSL that feels like normal programming but compiles straight to ZK circuits. Here’s a simplified guessing-game contract to show the magic:plaintext
def guess_number():
(a, b) = local.guess_factors(number) // private computation
assert(a != 1 and b != 1)
assert(a * b == number)
(a, b) = local.new_challenge()
number = a * b // public state update
Under the hood Compact splits this into three pieces:Local (off-chain): Runs your private functions.
Circuit (ZK): Encodes the constraints as arithmetic:
a1 × b1 = n2
a2 ≠ 1
b2 ≠ 1
n3 = a2 × b2
Public transcript (on-chain): Just the visible assertions and state writes.
You generate the proof off-chain, submit it with the transcript, and the chain only stores the verifier key for that circuit. No one ever sees your guessed factors. The result? Private logic with public verifiability and full composability.Selective Disclosure: The “Rational” PartThis is where Midnight stops being just another privacy coin and becomes infrastructure for the real economy.Because proofs are programmable, you can build viewing keys and audit keys:A tax authority can be given a viewing key that lets them compute your total taxable income from your private history without seeing individual trades.
A regulator can receive an audit key that proves you’re compliant with sanctions lists without ever learning your counterparty addresses.
You can prove “I’m over 18 and not on any watchlist” to a DeFi lending protocol while keeping your exact balance and identity hidden.
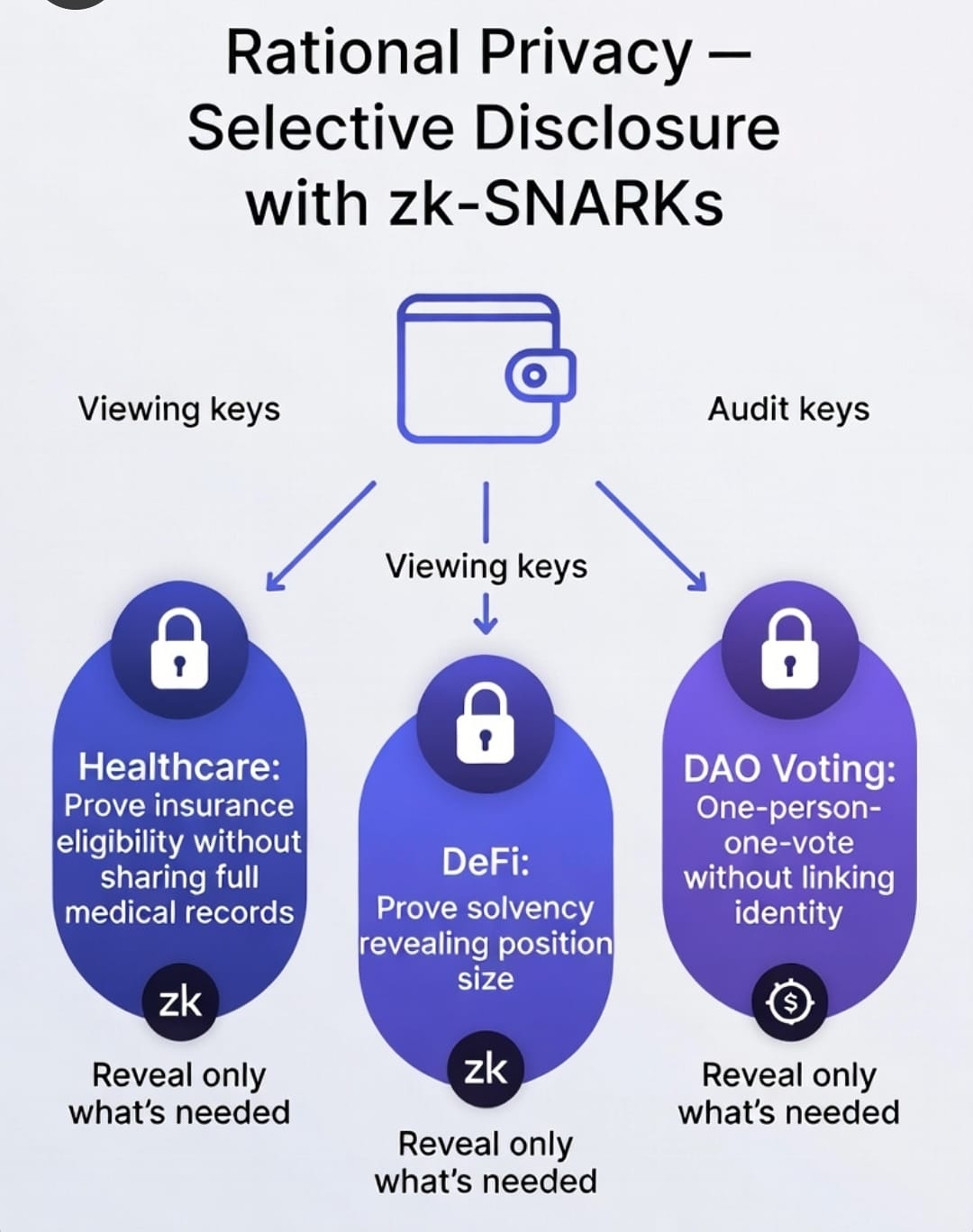
This is the middle path regulators have been begging for: cryptographic compliance without mass surveillance.Performance, Scalability, and the Road to MainnetAs of March 2026, with mainnet either live or hours away, the numbers are promising. Recursive composition on BLS12-381, combined with the dual-state model, targets throughput that would choke most pure-ZK chains. The DUST token (generated from staking NIGHT) pays for private execution in a predictable way—decoupling cost from token volatility.Cross-chain bridges to Cardano (and eventually others) use recursive proofs to attest Midnight state without re-executing everything on the destination chain. That’s how Midnight becomes the privacy layer for the broader ecosystem rather than a siloed island.The Honest Trade-OffsNo system is perfect. Recursive layers add complexity and potential attack surface (though formal verification work is ongoing). The initial launch used some federated nodes for stability—true permissionless consensus is still rolling out. The Minokawa compiler (which turns Compact into circuits) is a trust boundary until it’s fully audited and decentralized. And like any zk-SNARK system, the universal setup still carries theoretical “if the toxic waste is leaked” risks—though BLS12-381’s existing ceremonies are among the most scrutinized in the industry.Critics from the pure cypherpunk camp argue that selective disclosure is just “regulated privacy.” Fair point. But for institutions that actually move real value—healthcare, tradfi, enterprise supply chains—total anonymity is a non-starter. Midnight’s model gives them cryptographic guarantees they can actually use.Why This Matters Beyond CryptoImagine a world where:Your health insurer proves you qualify for a lower premium without seeing your full medical file.
A DAO votes on proposals with secret ballots that are still provably one-person-one-vote.
A company sells aggregated business intelligence as ZK attestations—monetizing data without ever exposing raw records.
That world isn’t science fiction. It’s the logical endpoint of Midnight’s zk-SNARK architecture.The team didn’t just slap Halo2 onto another chain. They rebuilt the contract execution model around proofs from day one, using Kachina’s dual-state and transcripts to make privacy the default rather than the exception. Recursive BLS12-381 proofs give them the scaling headroom. Compact makes it accessible to normal developers. Selective disclosure makes it compliant.In an era where every regulator on Earth is waking up to data privacy and every user is exhausted by constant leaks, Midnight’s zk-SNARKs feel less like a feature and more like the missing piece the entire industry has been waiting for.The proofs are small. The verification is fast. The privacy is programmable. And for the first time, you don’t have to choose between utility and secrecy—you get both, rationally, on-chain.That’s not hype. That’s the architecture Midnight actually shipped. And once you see how the pieces fit together, it’s hard to imagine going back to anything less. #night $NIGHT