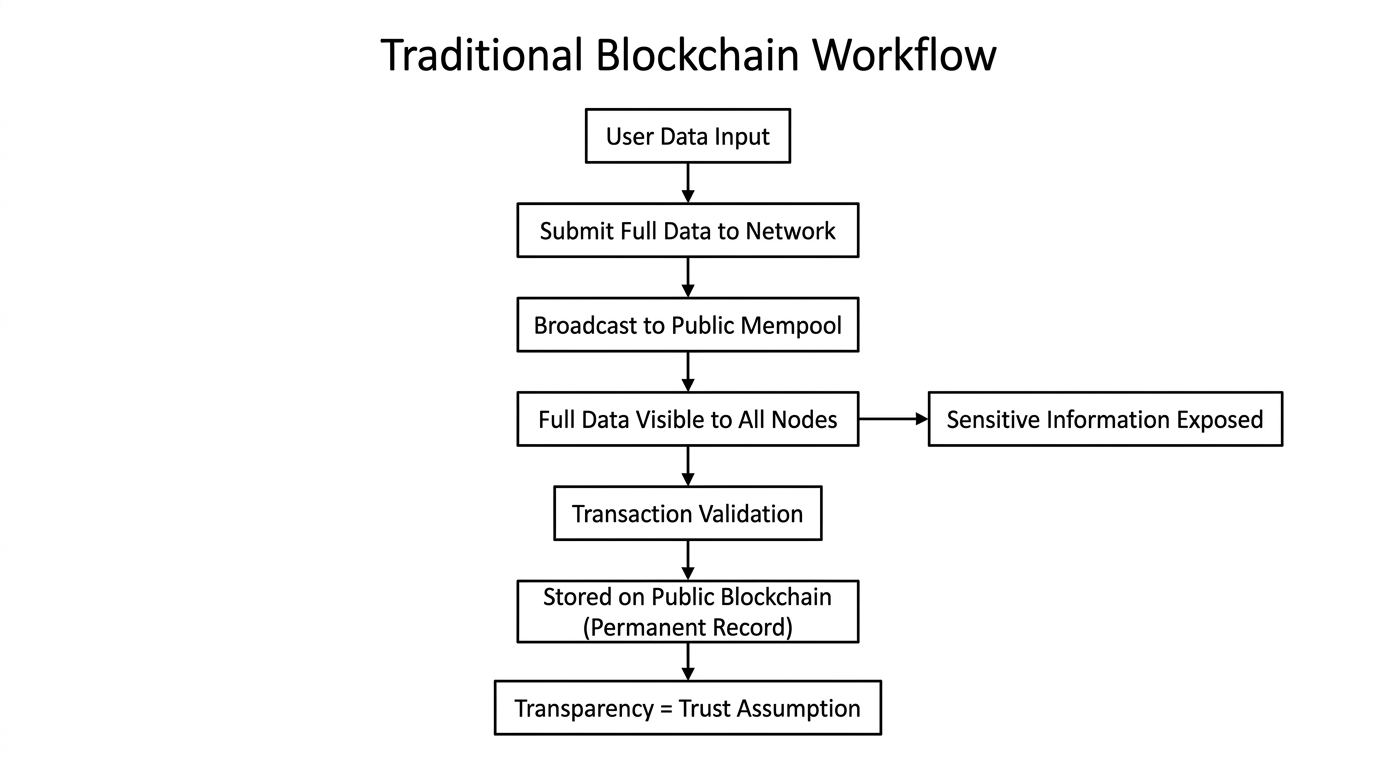
There is a version of trust that most digital systems have never been able to build. Not because the technology was unavailable. Because the assumption underneath every system was wrong from the beginning. The assumption was this: if everyone can see everything, then everyone can trust everything. That logic made sense for certain kinds of transactions. It made sense for moving value between parties who needed a public record. But it never made sense for the kind of information that most human activity actually runs on. Medical decisions. Business negotiations. Legal conditions. Financial qualifications. These do not become more trustworthy when they are fully visible. They become unusable. And most blockchains walked directly into that problem without ever stopping to question the assumption that created it.
That assumption is what Midnight Network is built to replace.
Before explaining what Midnight is doing, it is worth being precise about what it is not. It is not a project that decided privacy was a good narrative and built a token around it. It is not another chain offering anonymity as a substitute for accountability. And it is not operating in the category of older privacy systems that made concealment the entire product and then spent years unable to answer basic questions from regulators about why. Night is approaching this differently. More carefully. With a design that understands the difference between hiding and protecting.
What Midnight Network is building is programmable privacy. Not a fixed state where everything is shielded or everything is exposed — but a system where the boundary between public and private is a deliberate architectural decision. The project calls this rational privacy. The idea is that selective disclosure — sharing only what is required, to the right party, under the right conditions — should be something the network enforces by design rather than something users and developers have to work around. That is a genuinely different starting point. And it is the starting point that makes Midnight Network relevant to industries that have never been able to use blockchain seriously before.
Zero-knowledge proofs are the mechanism that makes this real. Here is how I think about it. Imagine a witness who can testify that a contract was signed correctly, that all conditions were met, that every party was eligible — without ever reading the contract aloud or naming anyone involved. The testimony is complete. The record is binding. The contents stay sealed. That is what ZK proofs do inside Midnight Network. The Kachina Protocol runs the private computation on the user's device. The verified result reaches the public chain. The underlying data never moves. It proves. It does not confess.
That opens blockchain to an entirely different category of real-world use. Healthcare records. Private business logic. Regulatory compliance. Financial eligibility verification. These are not experiments. They are the workflows that serious institutions run every day — and have kept off public ledgers because full transparency was never an option they could accept. Midnight Network is building the privacy layer for exactly that gap, as a partner chain to #Cardano , inheriting Cardano's peer-reviewed security foundation and extending it with private execution that Cardano's public architecture was never designed to provide. The Compact smart contract language makes that private execution accessible — developers build shielded applications without needing cryptography expertise to do it.
What interests me about the structure is the dual-token model. $NIGHT is Midnight Network's governance and capital asset — publicly traded, currently holding around $0.0442. The 4H chart today shows price sitting just above its short-term moving averages — MA(7) at $0.04412, EMA(7) at $0.04424 — with MA(25) and EMA(25) both converged at $0.04562 acting as the immediate resistance above. Volume has eased significantly from the peak days. The market is quiet. That kind of low-volume consolidation directly above short-term support, with the launch level of $0.04240 still intact below, tends to precede a directional decision rather than signal abandonment. Holding NIGHT passively generates #DUST — a shielded, non-transferable resource that powers private transaction execution on Midnight Network and cannot be traded or moved between wallets. DUST is consumed through use and replenishes over time. Speculation lives in NIGHT. Operations run on DUST. That separation is a structural decision that no price cycle changes.
Mainnet is this month. The Kūkolu phase — Midnight Network's first full production launch — is the moment the programmable privacy infrastructure stops being a thesis and becomes a live network running real shielded applications through ZK proofs on-chain.
Because the honest version of this is that elegant architecture does not fill an ecosystem. Rational privacy as a design principle does not guarantee that the applications built around selective disclosure will create the kind of habitual, returning usage that turns a privacy layer into necessary infrastructure. Many networks have launched with serious technology and thin adoption. Midnight needs developers to find the on-chain verification model not just interesting but indispensable.
The design is deliberate. The thesis is coherent. The technology is real. But I keep coming back to the same question every time a network reaches this specific moment — the one between launch and actual use. Not whether Midnight Network can go live. Whether, after it does, there are applications running on it that could not have been built anywhere else.
That is the test that matters. And nothing written about Midnight Network today, including this, gets closer to answering it than the moment the first real application runs.
#night @MidnightNetwork $NIGHT
