$SIGN Every major democracy carries within it an uncomfortable truth: there is always at least one election it cannot fully trust. This doubt does not necessarily arise because the results were incorrect or manipulated beyond repair. More often, it exists because the process itself cannot be independently and conclusively verified by everyone. Trust, in such systems, is not absolute—it is assumed, negotiated, and sometimes contested.
#Sign This pattern has repeated itself across some of the most established democracies in the world. The United States spent months entangled in legal battles after the 2020 presidential election, with dozens of court cases attempting to challenge or defend the integrity of the results. In Brazil, the 2022 presidential election led to weeks of protests, with a significant portion of the population unwilling to accept the announced outcome. Kenya took an even more dramatic turn in 2017, when its Supreme Court annulled the presidential election due to irregularities in the transmission of results. Meanwhile, France has repeatedly suspended and reinstated electronic voting systems over persistent security concerns. #Sign @SignOfficial $SIGN

These are not fringe cases or unstable regimes. These are mature democracies with decades—sometimes centuries—of institutional development. Yet even they struggle with a recurring legitimacy crisis when it comes to elections. The uncomfortable conclusion is that traditional voting mechanisms—whether paper ballots or electronic systems—have not fully solved the problem of trust. They have only managed it.
At the heart of this issue lies a fundamental paradox—one that traditional systems have never been able to resolve cleanly. A legitimate election demands two properties that appear, at first glance, to be mutually exclusive.
The first is verifiability. Any observer, whether a citizen, an auditor, or an independent body, should be able to confirm that every vote has been counted correctly and that the final result accurately reflects the collective will of the voters. Without verifiability, elections rely entirely on blind trust in institutions—a fragile foundation in an increasingly skeptical world.
The second is ballot secrecy. No one should be able to determine how any individual voted. This principle is essential to protect voters from coercion, intimidation, and retaliation. Without secrecy, the freedom to vote becomes an illusion, as individuals may feel pressured to align their choices with powerful actors.
In traditional systems, these two principles are in constant tension. Increasing transparency often comes at the cost of privacy. If every step of the process is made visible, the risk of exposing individual votes grows. On the other hand, strengthening privacy tends to reduce visibility, creating blind spots where fraud or manipulation can occur undetected.
This trade-off has shaped the design of electoral systems for centuries. Paper ballots, sealed boxes, and manual counting were attempts to strike a balance. Observers could monitor the process, but only within physical and logistical limits. Electronic voting systems introduced speed and efficiency but often at the cost of transparency, as the underlying processes became opaque to the average citizen.
The result is a system where trust is never absolute. It is always conditional—dependent on institutions, procedures, and the assumption that those in control will act in good faith.
This is where a new class of cryptographic tools begins to change the conversation.
Zero-knowledge proofs offer a fundamentally different approach. Instead of forcing a trade-off between transparency and privacy, they make it possible to achieve both simultaneously. In simple terms, a zero-knowledge proof allows one party to prove that a statement is true without revealing any additional information beyond the validity of that statement.
Applied to voting, this concept becomes transformative.
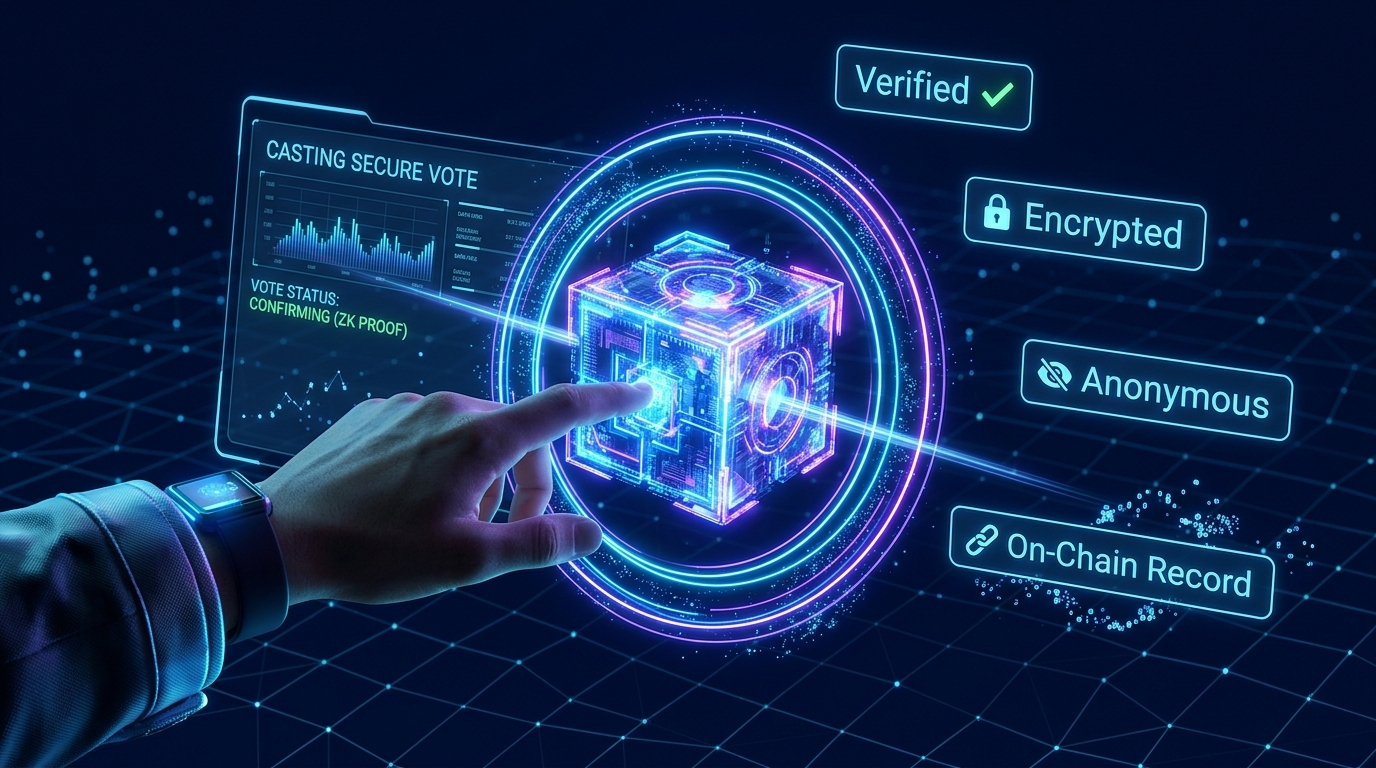
A voter can cast a ballot, and that ballot can be encrypted to ensure complete privacy. At the same time, a cryptographic proof can be generated to demonstrate that the vote is valid—that it was cast by an eligible voter, that it follows the rules of the election, and that it has been included correctly in the final tally. Crucially, this proof does not reveal who the voter chose.
This is not a theoretical abstraction. It is the foundation of modern blockchain-based voting systems such as those built on the Sign Foundation framework. Using the Sign Protocol, these systems integrate identity verification, vote encryption, and public verification into a single cohesive architecture.
The process unfolds in a series of precise steps. A voter first establishes their eligibility through a digital identity system, often based on Self-Sovereign Identity (SSI). This ensures that only authorized participants can vote, without tying their personal identity to their specific ballot.
Once the voter casts their vote, it is immediately encrypted. A zero-knowledge proof is generated alongside it, confirming that the vote is legitimate. This encrypted vote is then recorded on a blockchain, creating an immutable and tamper-resistant record.
When the election concludes, all encrypted votes are aggregated. Another zero-knowledge proof is generated to verify that the final tally has been computed correctly from the set of recorded votes. Observers can independently verify this proof, gaining confidence in the result without ever accessing individual ballots.
The outcome is a system that achieves what was previously considered impossible: a fully verifiable election in which individual votes remain completely private.
The implications of this shift are profound.
Consider overseas voting, one of the most persistently underserved aspects of democratic systems. Citizens living abroad often face significant barriers to participation. Physical ballots must be mailed across borders, leading to delays and logistical challenges. Consular voting facilities are limited, and absentee ballots are frequently rejected due to technical errors or missed deadlines.
A blockchain-based voting system changes this dynamic entirely. An overseas voter can participate using a smartphone or computer. Their identity is verified cryptographically, their vote is cast and recorded within minutes, and the entire process is transparent and auditable. The barriers that once excluded millions of voters begin to disappear.
The impact on election security is equally significant. Traditional forms of election fraud—such as ballot stuffing, manipulation during result transmission, or interference in vote counting—depend on specific vulnerabilities within the system. These vulnerabilities often arise from opacity, where certain stages of the process are hidden from scrutiny.
In a cryptographic voting system, these points of weakness are fundamentally altered. Each vote is a secure, verifiable object created at the moment of casting. There is no opportunity to “add” fraudulent ballots without detection, as every vote must be accompanied by a valid cryptographic proof. There is no transmission stage where results can be quietly altered, as the data is recorded on a decentralized ledger. There is no manual counting process that can be influenced by human bias or error.
To compromise such a system, an attacker would need to break the underlying cryptographic guarantees—a task that is computationally infeasible with current technology.
However, it is important to recognize that technology alone does not solve every problem.
One of the most immediate challenges is access. Digital voting systems require digital infrastructure—reliable internet connectivity, access to devices, and a baseline level of digital literacy. In regions with large rural populations or limited technological resources, these requirements can become significant barriers.
Efforts to address this issue, such as offline verification methods using QR codes or NFC-based credentials, can reduce the dependency on constant connectivity. But they cannot eliminate it entirely. Ensuring equitable access remains a critical concern.
Another challenge lies in governance. Even the most secure system must be governed by rules and institutions that people trust. Questions about who controls the underlying smart contracts, who verifies the cryptographic proofs, and who has the authority to update the system are not merely technical—they are deeply political.
If a small group of developers or officials has the power to modify the voting system during a contested election, the legitimacy of the entire process can be called into question. In this sense, the problem of trust does not disappear; it evolves.
The technology can guarantee that votes are counted correctly, but it cannot, on its own, determine who should be trusted to manage the system. That responsibility lies with governance frameworks, legal structures, and democratic institutions.
This brings us to a crucial realization.
The mathematical problem of voting—ensuring accuracy, privacy, and verifiability—can now be solved with advanced cryptography. Systems built on zero-knowledge proofs and blockchain technology represent a significant step forward in this regard.
But democracy is not purely a mathematical construct. It is a social, political, and institutional system that depends on trust, participation, and legitimacy. These elements cannot be encoded entirely in code.
What cryptography offers is not a complete solution, but a powerful foundation. It reduces the space for doubt, limits the opportunities for manipulation, and provides tools for greater transparency and accountability.
In a world where trust in institutions is increasingly fragile, these tools matter.
They do not eliminate the challenges of democracy, but they make it harder for those challenges to undermine the system itself.
Democracy, in the end, is harder than cryptography.
But for the first time, cryptography gives democracy a fighting chance. 🔥

