I didn’t think much of it at first.
Another alert. Another protocol pausing contracts. Another “suspicious activity” post that usually turns into a contained incident within a few hours.
But this one didn’t stay contained.
What started as a bridge issue Kelp DAO inside quickly turned into something bigger — something that moved across protocols, across assumptions, and across balance sheets faster than most people expected.
And that’s what makes this story worth slowing down for.
A Simple Headline, A Complicated Reality
On the surface, the facts are straightforward.
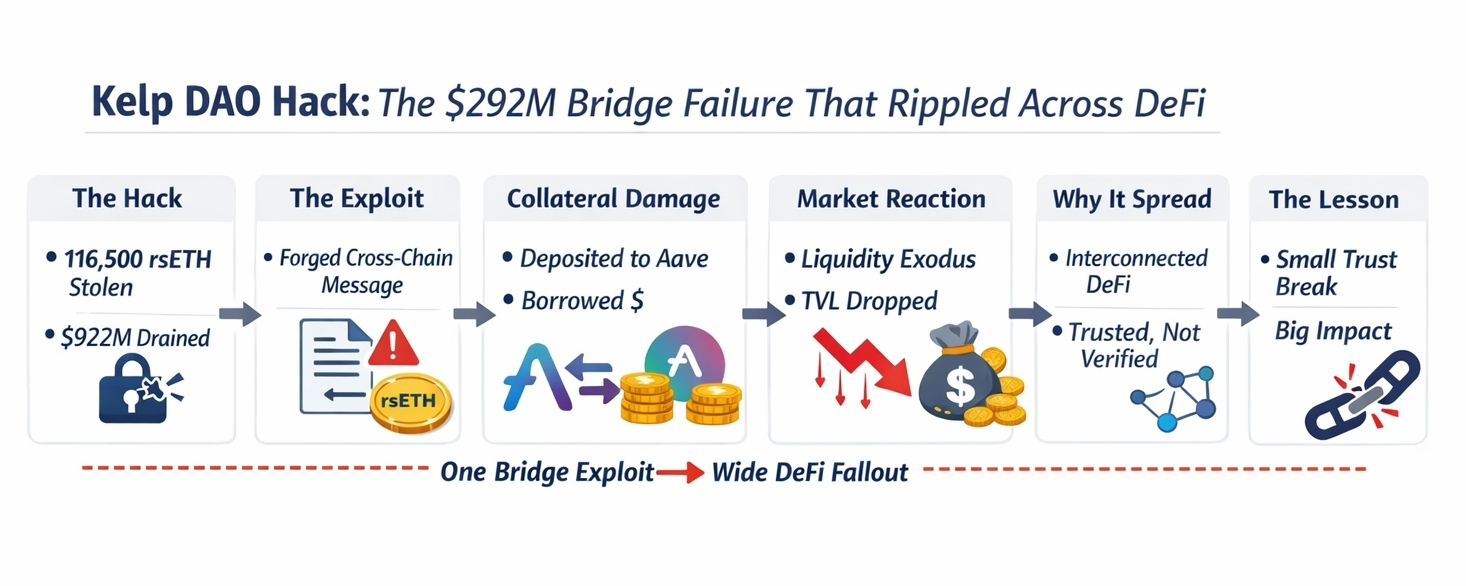
Around 116,500 rsETH was drained, worth roughly $292 million.
Kelp DAO detected unusual cross-chain behavior, paused contracts, and began investigating alongside LayerZero.
That’s the version that fits neatly into a headline.
But headlines don’t capture what actually happened here.
Because this wasn’t just a hack.
It was a breakdown in trust — and not just in one place.
Where Things Actually Broke
If you trace the event back, it doesn’t look like a traditional exploit where someone cracks a contract open and drains funds directly.
Instead, it looks like something quieter.
The attacker appears to have taken advantage of how the bridge handled cross-chain messages. At some point, the system accepted something it shouldn’t have — a message that looked valid, but wasn’t.
And that was enough.
No need to break the core system. No need to rewrite the rules.
Just convince the bridge to believe something false.
From there, rsETH was effectively created or released without proper backing.
And once that happened, everything downstream treated it as real.
The Moment It Stopped Being “Just Kelp”
What really changed the tone of this incident was what came next.
The attacker didn’t just sit on the stolen rsETH.
They used it.
They moved it into Aave, posted it as collateral, and borrowed out real assets — primarily ETH.
That’s the pivot point.
Because now the problem wasn’t isolated anymore.
Aave wasn’t hacked. Its contracts weren’t broken.
But it accepted an asset that had quietly lost its backing.
And that turned someone else’s exploit into Aave’s problem.
Liquidity Moves Before Explanations Do
Once the situation became clear, the reaction was immediate.
Markets tied to rsETH were frozen. Borrowing activity was restricted. Risk controls kicked in.
But users didn’t wait for full explanations.
They withdrew.
Liquidity started leaving. TVL dropped. Confidence shifted almost in real time.
That’s one of the less talked about truths in DeFi.
Systems can be designed to react quickly — but users react faster.
And once trust starts to slip, it rarely pauses to ask for details.
Why This Spread So Easily
It’s easy to ask why one exploit caused so much damage.
But the answer is already built into how DeFi works.
rsETH wasn’t just sitting in one place. It was everywhere.
It was:
Bridged across multiple networks
Used as collateral in lending markets
Integrated into different strategies and platforms
That level of integration is usually seen as strength.
It means utility. Liquidity. Efficiency.
But it also means something else.
It means that when one assumption breaks, it doesn’t stay local.
It travels.
The Difference Between Safe and Trusted
There’s an important distinction that this incident brings into focus.
An asset can be widely trusted without being deeply verified.
rsETH had adoption. It had liquidity. It had presence across protocols.
That created confidence.
But confidence isn’t the same as resilience.
When the bridge layer failed — or more precisely, when the assumptions around it failed — the trust didn’t disappear instantly.
It lingered just long enough to be used as collateral.
And that window was enough.
What We Know, And What We Don’t
Some parts of this story are clear.
The amount drained. The contracts paused. The reaction from protocols like Aave.
But the exact root cause is still being investigated.
Was it a misconfigured verification system? A flawed trust model? Something more specific in how messages were validated?
Those answers will likely come later, in a full post-mortem.
For now, what matters is understanding the shape of the failure — not just the details.
A Pattern That Keeps Repeating
If this feels familiar, it’s because it is.
DeFi keeps building systems that are:
More connected
More efficient
More composable
And every time, the same tension shows up.
On the surface, everything works beautifully.
Underneath, the system depends on layers of assumptions — technical, economic, and cross-chain — all holding at the same time.
Most of the time, they do.
Until one doesn’t.
A Quiet Ending Thought
There’s a tendency to focus on the number — $292 million.
But the number isn’t the most important part.
What matters is how easily something that looked stable turned into something uncertain.
Not because everything failed.
But because one small piece was trusted just a little too much.
And in a system where everything connects, that’s all it takes.