@Pixels #pixel $PIXEL I’ve spent enough time in crypto to know how easy it is to fall in love with narratives that sound structurally important. Over the years I’ve watched countless ideas presented as inevitable parts of the future financial systemideas that, on paper, seemed indispensable. Yet many of them never translated into real usage. They existed as concepts that investors discussed, not systems people relied on daily. That experience made me increasingly skeptical of anything that sounds necessary but isn’t embedded into real workflows. When I started paying attention to digital identitydriven blockchain infrastructure, I approached it with the same caution.
What interested me was not the concept itself, but how identity behaves once it is placed directly inside financial infrastructure. In most traditional systems, identity verification sits outside the transaction layer. Banks, exchanges, and service providers handle it as a separate gatekeeping process. But when identity becomes part of the underlying infrastructure, the relationship between users and systems changes. Transactions no longer rely purely on institutional trust; they rely on verifiable identity states embedded within the network. In practice, this shifts the balance of coordination away from intermediaries and toward protocol-level verification.
From a design perspective, the most interesting implementations are the ones where identity operates quietly in the background. Good infrastructure rarely draws attention to itself. Instead of forcing users through constant verification loops, these systems establish identity once and allow it to function persistently across applications. The technical challenge is balancing verifiability with privacy. If the identity layer exposes too much information, it becomes intrusive. If it hides too much, institutions struggle to rely on it. The most effective designs I’ve observed treat identity as a set of cryptographic attestations rather than a visible profilesomething the system can verify without constantly asking the user to prove themselves again.
Repeated usage reveals something theory often ignores: user behavior changes once identity becomes embedded in financial interaction. When verification is frictionless, people quickly stop thinking about it. It becomes part of the environment rather than an action they perform. But if identity verification interrupts workflowsforcing repeated confirmations or exposing too much personal datausers become cautious. I’ve seen traders hesitate before interacting with systems that feel overly invasive, even when the infrastructure itself is technically sound. Trust, in these environments, is less about security guarantees and more about how invisible the verification process feels.
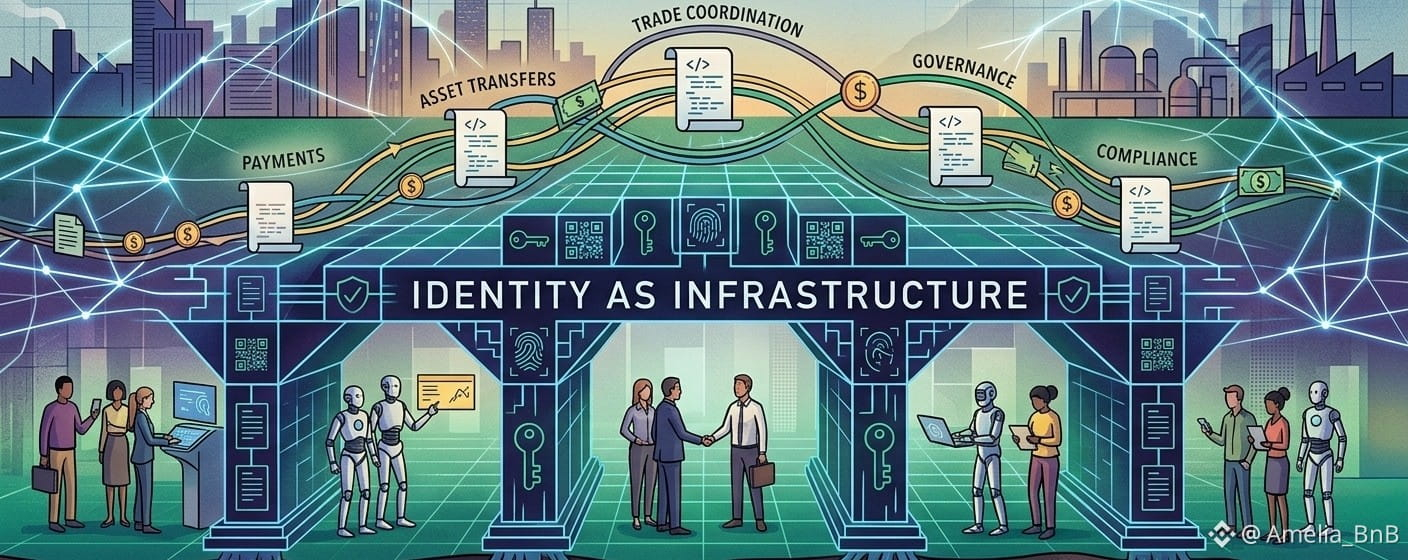
This dynamic becomes especially interesting in regions undergoing rapid digital transformation. In parts of the Middle East, for example, financial infrastructure is evolving alongside large-scale digital identity initiatives. What I’ve noticed is that separating identity from financial systems often creates inefficiencies over time. Institutions repeatedly rebuild verification processes for each new servicepayments, exchanges, licensing, trade platforms. When identity infrastructure sits outside the system, coordination becomes fragmented. Integrating identity directly into transaction layers, on the other hand, allows multiple services to rely on the same verification foundation.
But markets rarely evaluate infrastructure based on long-term coordination. They tend to respond to narratives. I’ve watched many projects gain attention simply because the story surrounding them sounds strategically important. Identity infrastructure is particularly vulnerable to this. It sounds essential for the future of digital economies, which makes it attractive for speculation. Yet trading activity and market excitement often reflect expectations rather than actual usage. When I look at these systems, I try to ignore the narrative and focus on behavioral signals instead.
The most reliable signal is repetition. Infrastructure proves itself not through announcements or partnerships, but through consistent usage patterns. If identity verification appears repeatedly across different applicationspayments, asset transfers, governance systemsthen it begins to function as real infrastructure. If it only appears during onboarding or occasional compliance checks, it remains more of a concept than a working layer.
This is where many systems quietly fail. They introduce identity frameworks but never integrate them deeply enough into everyday workflows. Developers treat identity as an optional feature rather than a foundational component. As a result, users interact with it once or twice and then rarely encounter it again. That kind of usage doesn’t build infrastructure; it builds a feature.
When I evaluate identity-driven blockchain systems today, I look for a few simple signals. Are users interacting with identity layers repeatedly across applications? Are there products where identity is essential rather than optional? Is network participationvalidators, developers, and service providerscontinuing long after the initial excitement fades?
Ultimately, the difference between an idea that sounds necessary and infrastructure that actually becomes necessary is surprisingly simple. Narratives can convince people something should exist. But real infrastructure reveals itself when users rely on it repeatedly, often without even noticing that it’s there.