While examining the infrastructure of Web3, one recurring challenge emerged across various blockchain systems. The same feature that made blockchains revolutionary, complete transparency, also created friction in real-world applications. Every transaction on most public networks is visible, traceable, and permanently stored in an open ledger. This transparency works well for simple transfers or decentralized finance interactions. However, as blockchain technology intersects with identity systems, business processes, and sensitive data environments, the drawbacks of full transparency become more apparent.
This issue highlights a broader problem in the industry. Many blockchain designs focus primarily on openness and auditability. While this fosters trust in decentralized systems, it often clashes with the practical needs of businesses, institutions, and individuals who cannot publicly expose every detail of their operations. Financial records, compliance data, supply chain agreements, and personal identity credentials are rarely intended for a fully transparent environment. Consequently, developers looking to build real-world applications on public blockchains often face a challenging compromise between transparency and confidentiality.
In this context, Midnight Network starts to stand out as an infrastructure experiment aimed at resolving this tension. Rather than solely improving transaction speed or lowering fees, Midnight explores how blockchain systems can maintain the benefits of decentralization while protecting sensitive information. Its main idea is that verification and privacy can coexist.
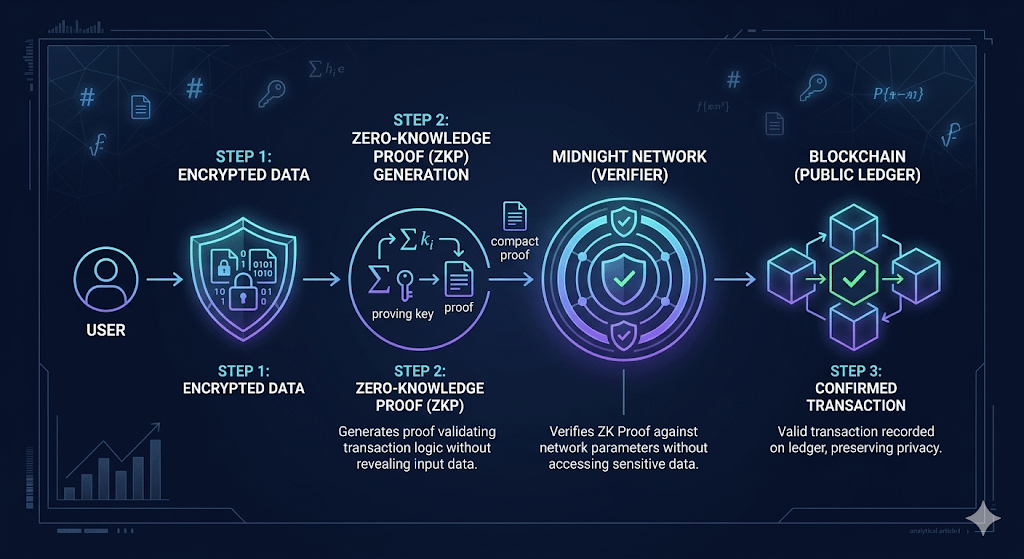
The network’s design heavily relies on Zero-Knowledge Proofs, a cryptographic method that allows one party to prove that a statement is true without revealing the underlying data. While the concept may seem abstract, it is easier to understand through everyday scenarios. For instance, imagine a company needing to show that it meets regulatory requirements or financial conditions. Instead of making internal data public on a blockchain, the system could generate a mathematical proof confirming compliance. The blockchain verifies this proof while keeping the underlying information confidential.
Midnight incorporates this capability directly into its network design. Developers on the platform can structure transactions so that validation occurs without unnecessary exposure of private data. Essentially, the blockchain acts as a verification layer instead of a fully transparent record of every internal detail. This design shifts the role of blockchain infrastructure from purely public ledgers to systems that can support privacy-sensitive digital interactions.
Another crucial aspect of Midnight’s design is its relationship with the Cardano ecosystem. Rather than trying to function in isolation, Midnight serves as a complementary layer that adds privacy-preserving features to decentralized applications connected to that ecosystem. This approach suggests collaboration, where existing networks provide scalability and development environments while Midnight contributes specialized cryptographic infrastructure aimed at confidentiality and data protection.
Like most decentralized networks, Midnight includes a native digital asset that supports the protocol’s economic structure. The token, NIGHT, serves as the incentive mechanism that manages participation within the network. Tokens typically have several functions within blockchain systems, including paying transaction fees, rewarding validators who maintain the network, and enabling governance participation among stakeholders. In Midnight’s case, the token acts as the economic layer, ensuring participants are encouraged to support the infrastructure that verifies transactions and upholds the network’s privacy-preserving environment.
What makes Midnight particularly fascinating from an infrastructure viewpoint is that it indicates a shift in blockchain thinking. Earlier networks primarily demonstrated that decentralized consensus could operate at scale. Later designs emphasized performance improvements and application ecosystems. Now, the focus is gradually moving towards usability and integration with real-world systems, many of which cannot function when all data is publicly accessible.
Privacy-preserving cryptography, especially zero-knowledge verification, is likely to play a more significant role in the next phase of Web3 development. Systems that can verify information without exposing it may enable blockchain technology to expand into sectors like regulated finance, identity verification, healthcare data management, and business coordination. These areas require trust and verification while also demanding strict control over sensitive information.
Of course, the success of such infrastructure will rely more on practical adoption than on theoretical design. Privacy technologies can be complicated to implement, and developers need accessible tools, reliable performance, and clear documentation to create meaningful applications. The growth of the ecosystem, particularly the rise of decentralized applications that showcase the benefits of privacy-preserving verification, will ultimately influence how significant Midnight becomes within the broader blockchain landscape.
For now, Midnight offers an intriguing solution to one of the quieter structural challenges of Web3. If blockchain systems are to advance beyond transparent ledgers and become widely accepted digital infrastructure, they must find ways to verify truth without requiring exposure. The vision behind Midnight suggests that privacy and decentralization can work together. Rather than competing, they may serve as complementary foundations for the next generation of blockchain networks.