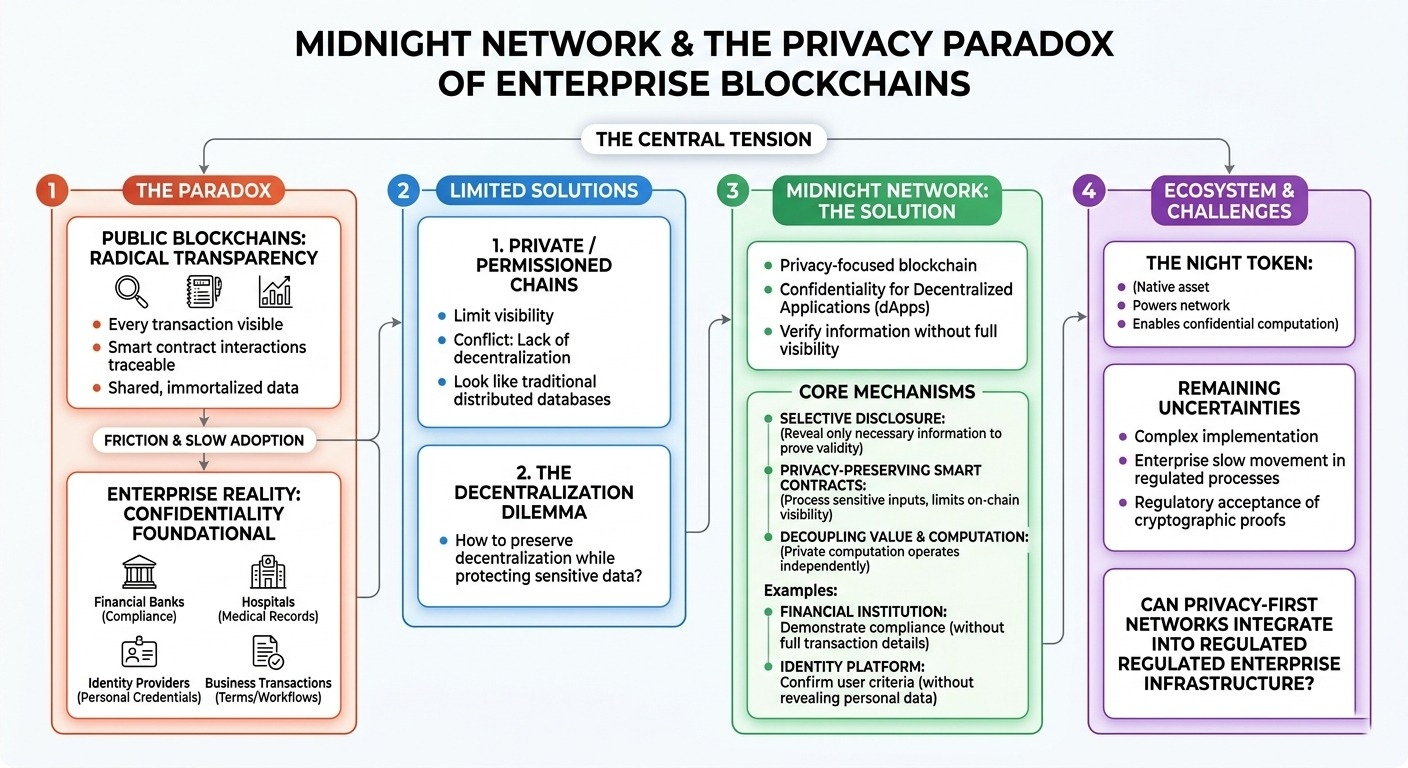
For all the enthusiasm around blockchain technology, there’s a quiet contradiction that tends to surface whenever enterprises seriously consider using it. Public blockchains are built around radical transparency. Every transaction is visible, every smart contract interaction traceable, every piece of data effectively immortalized in a shared ledger. That openness is supposed to create trust.
But when you think about how most large institutions actually operate, the model feels a little unrealistic.
Banks don’t run their internal systems in public. Hospitals certainly don’t broadcast patient data. Identity providers don’t publish verification trails for the world to analyze. The reality is that many of the industries that could benefit from decentralized infrastructure also depend on carefully controlled access to information. Privacy isn’t an afterthought in those sectors — it’s foundational.
Financial institutions operate under strict compliance regimes. Healthcare systems must protect medical records by law. Identity networks are built around safeguarding personal credentials. Even routine business transactions often contain confidential terms that companies have no interest in exposing to competitors.
And that’s where things get complicated.
Traditional public blockchains were never really designed with this kind of operational privacy in mind. Their transparency makes them powerful tools for open financial systems, but it also creates friction for organizations that deal with sensitive information. Transaction histories can reveal business relationships. Smart contract logic can expose internal workflows. Even metadata can leak signals about how companies operate.
Honestly, it’s one of the reasons enterprise blockchain adoption has been slower than many early advocates predicted.
Over the years, some companies tried to solve this by building private or permissioned blockchains. Those systems limit visibility to trusted participants, which helps with confidentiality. But they also drift away from the decentralized model that made blockchain infrastructure interesting in the first place. Without shared verification and open participation, these networks start to look suspiciously similar to traditional distributed databases.
So the real challenge isn’t simply adding privacy. It’s figuring out how to preserve decentralization while allowing sensitive data to remain protected.
This is roughly the problem space where Midnight Network enters the conversation.
Midnight positions itself as a privacy-focused blockchain designed to enable decentralized applications that require confidentiality. Instead of assuming everything must be publicly visible, the network experiments with mechanisms that allow certain information to remain private while still being verifiable.
One of the core ideas here is selective disclosure.
Rather than publishing all underlying data, systems can reveal only the information necessary to prove something is valid. A financial institution could demonstrate regulatory compliance without exposing the full transaction details. An identity platform could confirm that a user meets certain criteria without revealing personal data. In theory, the network allows verification without full transparency.
That capability becomes particularly important when you consider privacy-preserving smart contracts. These contracts can process sensitive inputs while limiting what becomes visible on-chain. Cryptographic techniques make it possible to confirm that specific conditions were met without revealing the raw data involved.
When you think about it, that approach could shift how compliance works in decentralized systems.
Regulators don’t always need to see everything. Often they just need assurance that certain rules were followed. If cryptographic proofs can provide that assurance while protecting confidential information, privacy might actually support regulatory oversight rather than undermine it.
Midnight also introduces an architectural idea that separates value from computation. In many blockchains, token transfers and application logic are tightly connected. Midnight tries to decouple these layers, allowing private computation to exist independently while still interacting with broader financial networks.
The NIGHT token plays a central role in this ecosystem. It functions as the native asset used to power the network and enable the execution of these privacy-focused smart contracts. But beyond its technical role, the token represents the economic layer supporting a system designed around confidential computation.
Of course, none of this eliminates the uncertainties.
Privacy technologies can be complex to implement securely. Enterprises tend to move slowly when new infrastructure touches regulated processes. Regulators themselves may hesitate to trust systems built on cryptographic mechanisms that are difficult to inspect directly.
The reality is that building privacy into blockchain infrastructure might solve one of the industry’s biggest adoption barriers. But it also introduces new technical and institutional challenges.
Which leaves an interesting question hanging in the air: can privacy-first networks like Midnight realistically integrate into the messy, regulated, and often conservative systems that dominate real-world enterprise infrastructure? That answer may ultimately determine whether ideas like this remain experimental — or quietly become foundational.#night @MidnightNetwork $NIGHT