been sitting with the S.I.G.N. governance documentation for the past two days and honestly the more i map out the role structure the more one design principle keeps pulling me back just like the chart of PIPPIN or ROBO 😂
the docs state it plainly
separation of duties
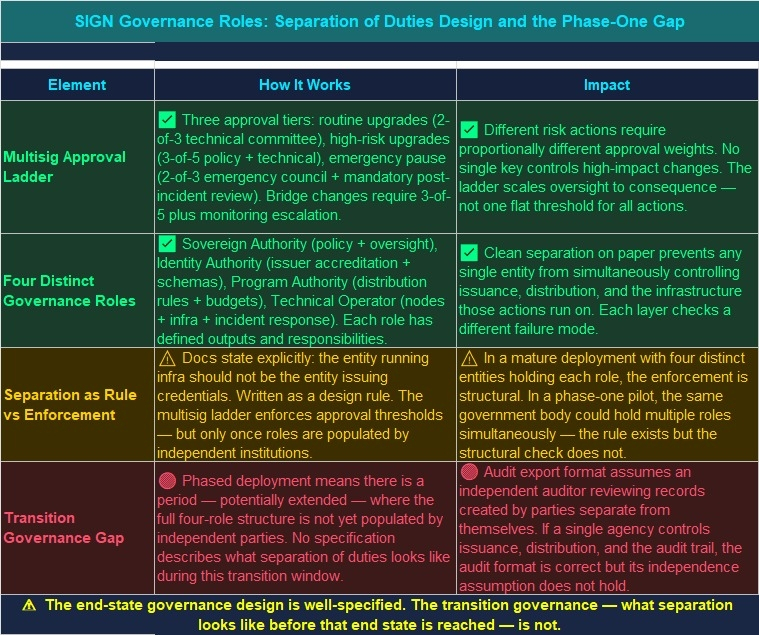
the entity running infrastructure should not be the entity issuing credentials. its written as a design rule, not a suggestion. policy governance, operational governance, technical governance - three distinct layers, each meant to sit with different hands.and on paper the structure is genuinely clean.
the key management design
actually one of the more thoughtful things ive read in a sovereign infrastructure whitepaper. routine upgrades need a 2-of-3 multisig from a technical governance committee. high-risk upgrades escalate to 3-of-5 requiring both policy and technical sign-off. emergency pauses need a 2-of-3 emergency council plus a mandatory post-incident review. bridge parameter changes go to 3-of-5 with a monitoring escalation requirement on top.
thats a real approval ladder
different risk levels
different thresholds
different committee compositions
not one key
not one entity
not one failure point
i spent yesterday afternoon just mapping which actions need which approvals and the logic is consistent all the way through.but here's what kept nagging me after i finished that mapping.
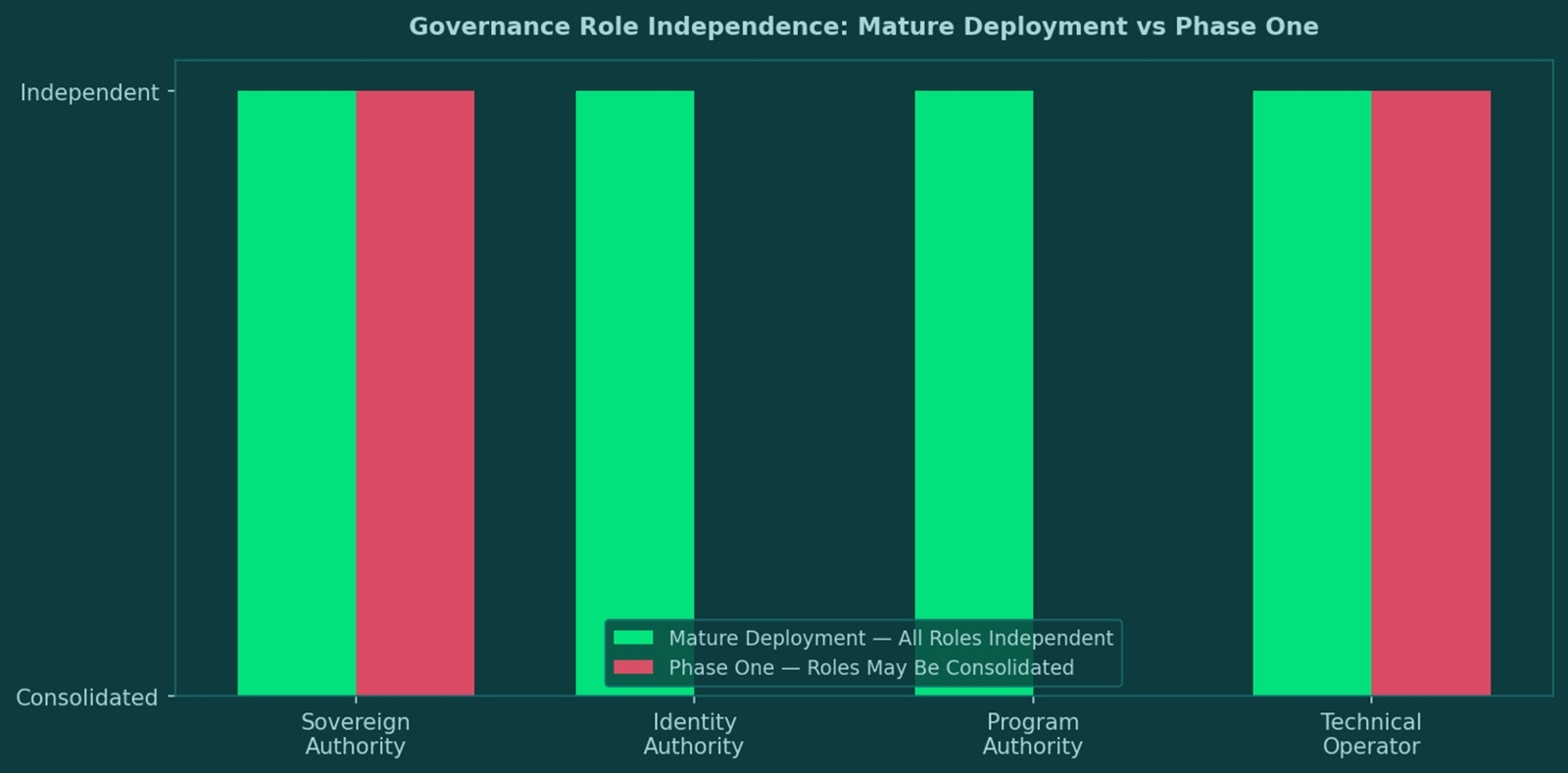
separation of duties is enforced by the approval ladder once the system is fully operational with distinct institutions holding each role. the central bank controls the CBDC network membership. the identity authority accredits issuers and governs schemas. the program authority manages distribution policies. the technical operator runs nodes and executes approved changes. four distinct roles, four distinct entities, clean lines.
the gap isnt in the design. its in the transition.
in a phase one deployment - assessment, pilot, limited scope - a single government agency could realistically be operating as the technical operator, functioning as the identity authority, and approving its own program distributions simultaneously. the architecture explicitly allows for phased rollout. it says nothing about what the separation of duties requirement looks like during that phase before the full role structure is populated by independent institutions.
the docs describe what auditors need: rule definitions, identity proof references, revocation logs, distribution manifests, settlement references. all of that assumes the audit function is held by a party independent from the ones who ran the distribution. but who enforces that independence before the governance structure is fully mature?
the whitepaper points to phased deployment as the practical path forward. pilot first, expand later, full integration last. thats the right approach for adoption. but it means there's a window - potentially a long one - where the separation of duties principle exists as a stated design rule without a structural mechanism enforcing it.
what the design gets right is the end state. the multisig ladder, the distinct role definitions, the audit export format, the monitoring dashboards - all of it is built for a mature sovereign deployment where each layer is independently governed. that end state is well-specified.what i cant find is the transition governance specification
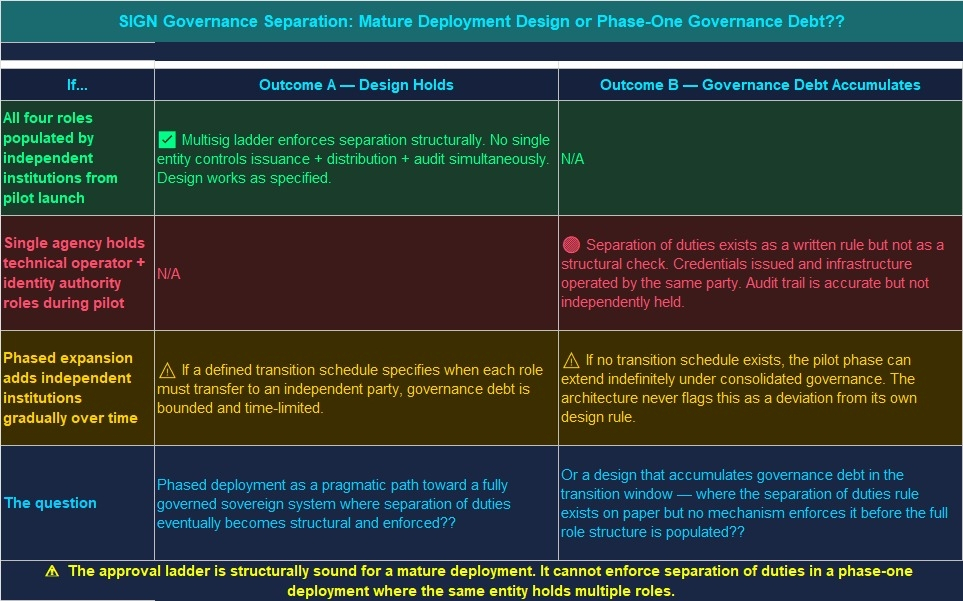
the rules that say: at this point in the rollout, this role must be transferred to an independent institution. before that threshold, these actions require external oversight anyway.
honestly dont know if the phased deployment approach is the pragmatic path to a genuinely well-governed sovereign system or a window where separation of duties is aspirational rather than structural and early deployments accumulate governance debt that the full architecture was specifically designed to prevent?? 🤔#SignDigitalSovereignInfra @SignOfficial $SIGN
