Systems that don’t turn every internal process into public spectacle. On paper, it sounds like exactly what blockchains have been missing.
And to be fair, it solves a real problem.
But that clean version only works as long as everything behaves.
The moment things don’t—when a case gets flagged, when something feels off, when a decision gets pushed into review—the center of gravity shifts. Quietly, but completely.
At first, it looks simple. A borrower proves collateral. The system verifies it. Funds move. Done.
Then something small breaks the flow. Maybe timing doesn’t line up. Maybe risk shows up late. Maybe a partner asks questions no one planned for. Nothing dramatic—just the kind of messy edge cases that happen in every real system.
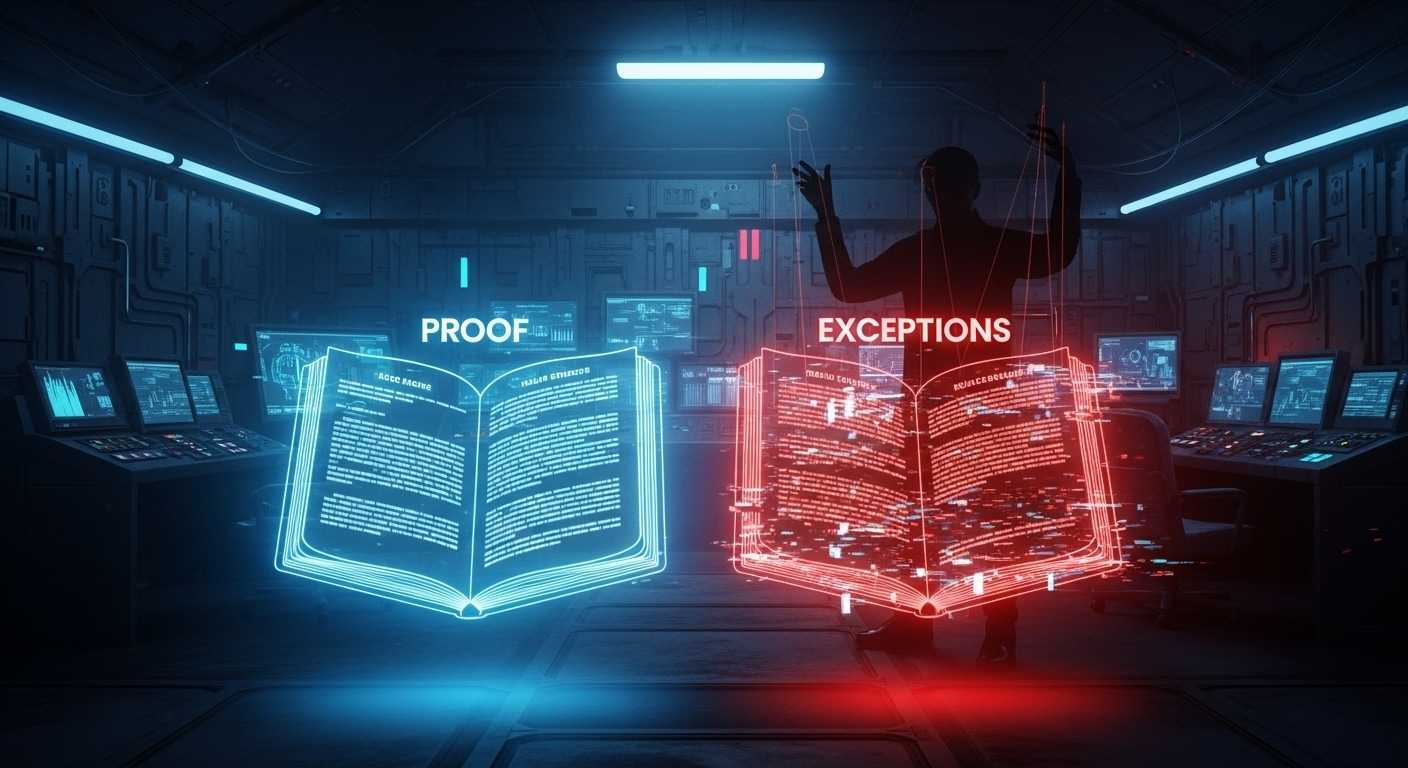
Now the proof isn’t enough anymore.
The borrower trusts what was verified. The counterparty leans on process. Compliance wants more visibility. And suddenly, there isn’t one shared version of reality—just different slices of it, depending on who you are.
That’s where things get uncomfortable.
Because “selective disclosure” doesn’t just happen on its own. Someone controls when it stops being selective.
Someone decides:
when more information gets revealed
who gets to see it
who gets left out
when the workflow can be paused, overridden, or escalated
And once those controls exist, the real power isn’t just in the proof—it’s in the permissions.
That part rarely shows up in the polished narrative. No one highlights the admin roles, the override rights, the escalation triggers. But that’s where the system actually lives once things stop going smoothly.
Two applications can run on the same foundation and tell the same privacy story—yet behave completely differently when something goes wrong. One might require multiple parties to unlock more visibility. Another might let a single role widen the scope instantly.
Same tech. Different reality.
That’s the part people underestimate.
Because it’s easy to believe the proof governs everything. And maybe it does—until it doesn’t. The second an exception appears, the rules quietly change.
Now it’s not about what was proven.
It’s about who controls the exception.
And those exception paths always sound reasonable. Fraud prevention. Compliance checks. Emergency handling. All necessary. All defensible.
But they form a second rulebook.
And that second rulebook is the one that takes over when the clean path breaks.
That doesn’t mean Midnight fails. The cryptography can still hold. The privacy guarantees can still technically exist.
But the real question moves somewhere else:
Who decides when privacy bends?
Who gets access when it does?
And did the user ever really understand that this was part of the system?
Because in the end, the proof might still be valid.
It’s just not the thing running the room anymore.
#night $NIGHT @MidnightNetwork