When I first started paying attention to privacy in crypto, it felt like everyone was yelling about transparency or tossing out bold slogans that never actually solved anything. Every project promised privacy—real privacy, too—but almost always forced users to give up convenience or could only tick off a checkbox instead of actually working in the real world. I figured that was just how things were. Privacy in blockchain would always come with trade-offs, and that was that. But recently, when I took another look, Midnight Network caught my eye—not because it’s loud or making waves, but because it’s quietly working on something that actually changes how we approach privacy itself.
These days, if you’re browsing blockchain ecosystems, you see it’s a systemic problem. Transparency is baked in—over 90% of on-chain data is out in the open, based on multiple independent studies. On one hand, this kind of openness builds trust. Anyone can check transactions, balances, contracts—you name it. But there’s always more to the story. Patterns start emerging: wallet behavior, when you send transactions, how often you do it, and how you interact with others. This stuff piles up into something that’s basically an identity—not just random data. Most people don’t realize they’re leaving a traceable trail.
What Midnight Network does differently is smart—it runs resources and verification side by side. Traditional networks chase raw throughput or play with staking incentives, but don’t really factor in privacy where it matters. Midnight rolls out a programmable resource model: validators, nodes, participants—they’re coordinated not just by who stakes the most tokens, but by how the network decides to allocate privacy-preserving resources and verification power. So the system figures out which data needs to be out in the open for trust, and which can stay private; it’s always shifting, balancing security, compliance, and user privacy.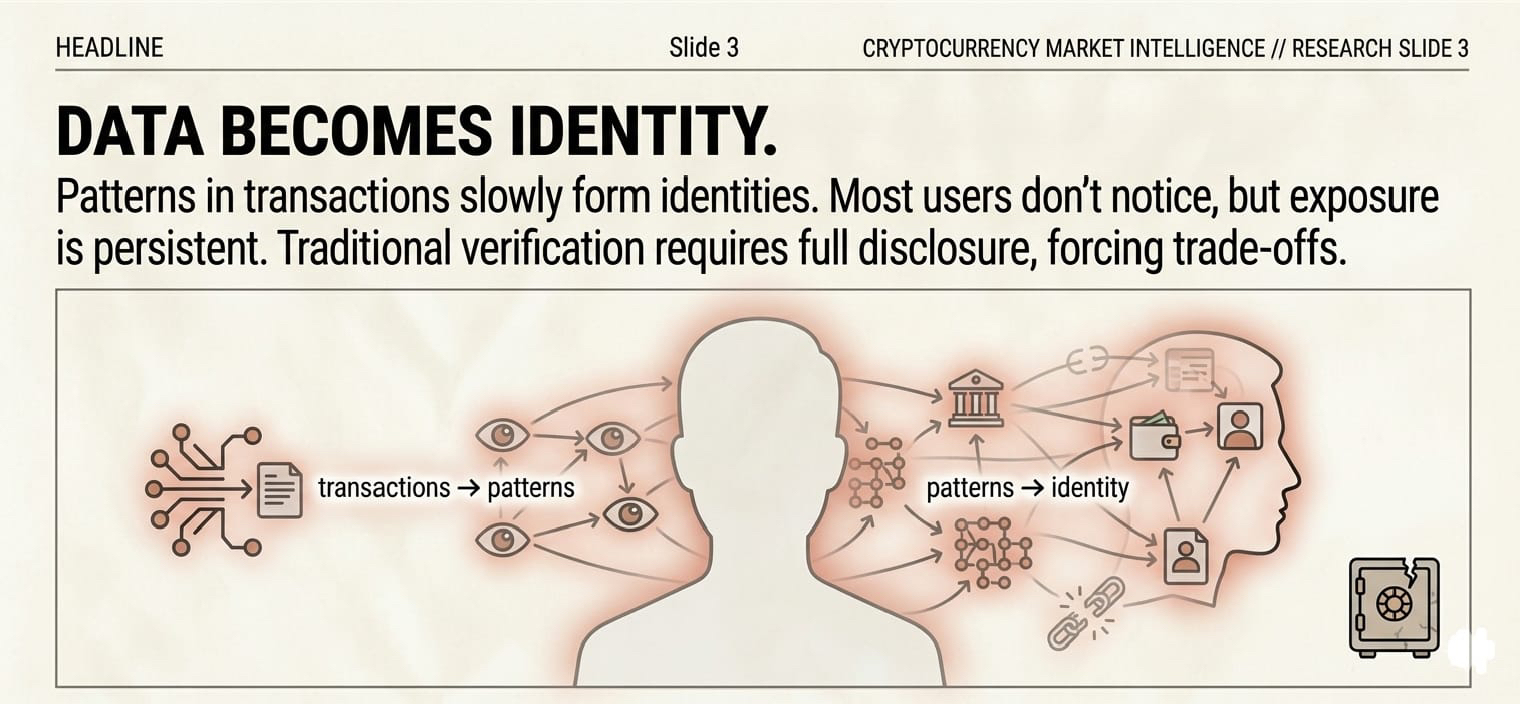
In practice, this lets you do things like identity checks, compliance, or DeFi moves with full validation, while keeping every single detail off public display. Picture sending money across borders: you want to prove you’re allowed to hit a certain limit, the system needs to confirm funds are real and rules are followed, but nobody else needs to see your whole balance history. Midnight’s approach makes that workable. It's not about hiding everything—just showing what’s necessary.
This model flips the economics of joining in, too. Resource allocation isn’t stuck in place—it changes with the volume, verification demand, and how users interact. Validators get rewarded for privacy-preserving work, which is a bit heavier on computing but crucial for the network’s trust. NIGHT token holders basically support this; by holding NIGHT, they help power the network’s integrity and get benefits as the platform grows. Compared to old-school staking models that only pay out for uptime or locked assets, Midnight pushes for contributions that matter for both privacy and usability.
We’re already seeing signs this could fill a major gap in crypto adoption. Whenever privacy coins got a big hype wave, their value often ballooned—but people didn’t really stick around to use them. The interest was there, but the execution always lacked something. Folks wanted easy-to-use privacy, not awkward networks that felt like speedbumps. Midnight’s model—linking privacy tasks to utility and smart incentives—aims right at that sore spot.
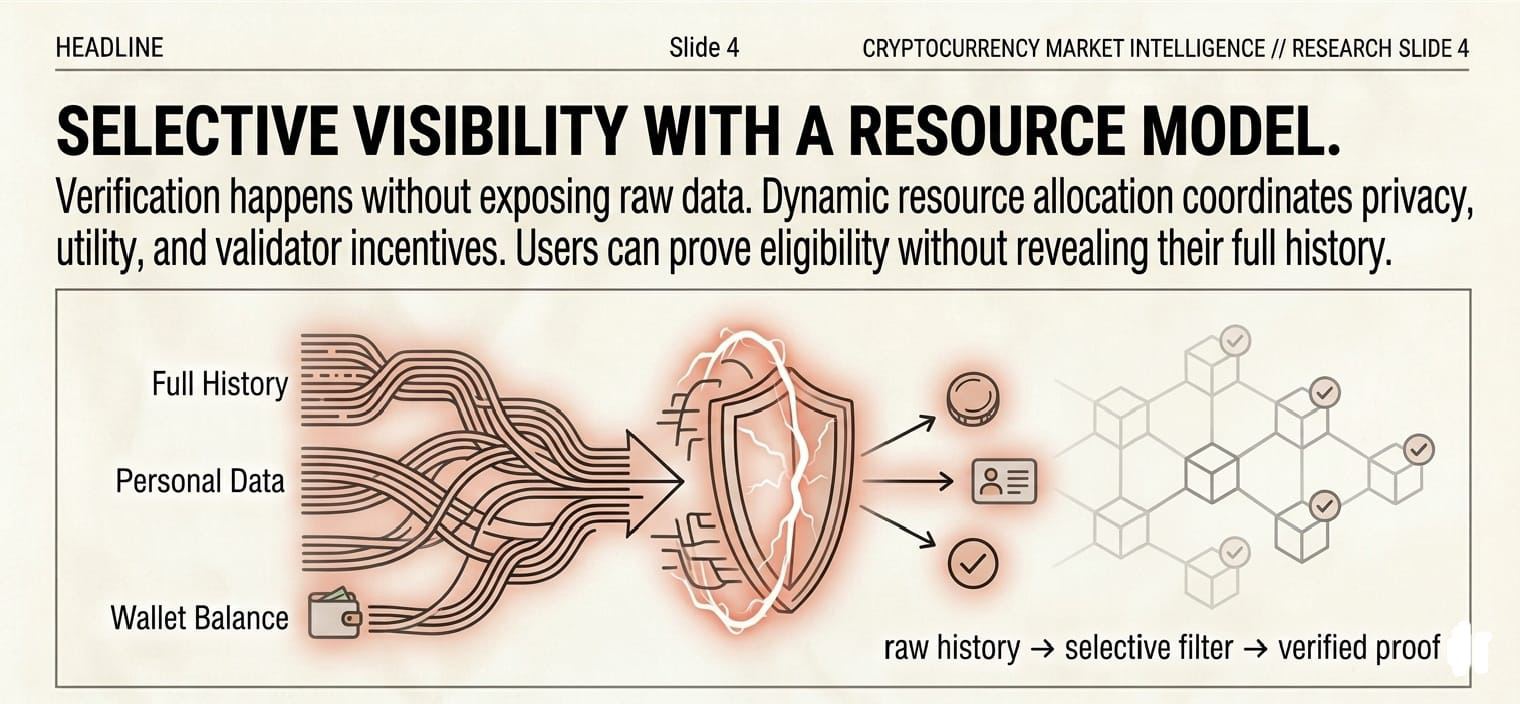 Regulation is always a hurdle, though. Pure transparency is easy for auditors, but selective disclosure can make people uneasy. Midnight tackles this by designing systems where everything can still be verified, but nobody’s personal stuff is thrown open unless needed. Regulators get what they need for audits or compliance—users keep control over what’s private. This balance could push new standards for privacy-first blockchains if regulators continue engaging positively. Maybe it’s even a blueprint for the next generation.
Regulation is always a hurdle, though. Pure transparency is easy for auditors, but selective disclosure can make people uneasy. Midnight tackles this by designing systems where everything can still be verified, but nobody’s personal stuff is thrown open unless needed. Regulators get what they need for audits or compliance—users keep control over what’s private. This balance could push new standards for privacy-first blockchains if regulators continue engaging positively. Maybe it’s even a blueprint for the next generation.
There’s also the user side—behavior matters. Surveys say around 70% of users worry about online privacy, but still tolerate platforms that leak their info. Crypto showed up promising freedom from those compromises, but most chains turned out to be even more transparent, ironically shrinking real privacy. Midnight fixes that gap beautifully. People can interact knowing verification is running smoothly and that their data isn't dumped out for everyone to analyze. That tiny boost in trust? Huge for adoption, especially as people look to the network for more sensitive things like finance and identity.
If you break things down, the secret sauce in Midnight’s design is in the layering. You get usable privacy at the surface, deep verification working under the hood, and incentives built around real privacy tasks. Each layer fits the next—usability, smart coordination, economic support—all reinforcing each other, which makes the whole system tougher and more flexible than standard privacy coins hiding balances or just disguising addresses.
Looking at where crypto’s heading, the market is quietly shifting. For the last five years, everyone cared about speed, cost, scalability, and chasing interoperability. Now, trust, control, and privacy aren’t just buzzwords—they’re real features people demand. Midnight’s model reflects that: less noise, more thoughtful design. If this thing scales up, it could rewrite the rules for user autonomy, privacy, and how networks govern themselves.
There are still risks. Performance limits, adoption numbers, developer buy-in, regulations—they’re all in play. No project wins on clever design alone; execution is everything. But so far, the signs are positive. Rolling this out across different use cases will be the real challenge.
If it works, the impact is big. Privacy, verification, and incentives come together, letting networks handle tough operations with trust and flexibility. Users interact confidently. Validators do meaningful work. The ecosystem grows up—a long way from empty slogans and hypes that fizz out after a big launch.
What gets me most is just how subtle Midnight’s approach is. You don’t see it in loud graphics or wild PR campaigns—the shift happens underneath. Privacy doesn’t have to kill usability. Verification doesn’t always mean breaking secrecy. Trust doesn’t mean giving up control. That’s rare, and it’s a big reason analysts see Midnight as a marker for a maturing privacy landscape—something other networks might copy down the road.
End of the day, Midnight’s story isn’t about hype or clever marketing spins. It’s about solving a real, stubborn problem with careful structure, smart economics, and engineering. If this holds up, it’ll reshape how everyone in crypto thinks about privacy, verification, and how networks run. The next phase might not be the flashiest—it might just be where trust gets quietly built-in, always working behind the scenes. Midnight Network is pointing right at that future.
#night @MidnightNetwork $NIGHT
