Let’s be honest—privacy in crypto has always felt like a trade-off. You either get transparency or confidentiality, but rarely both. That’s exactly where Midnight steps in and flips the script.
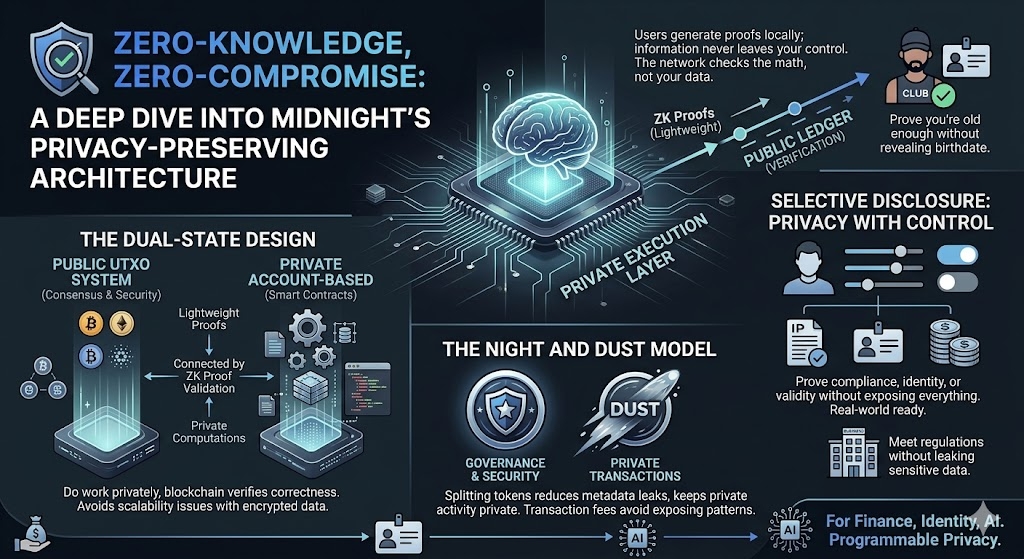
At its core, Midnight is built on zero-knowledge proofs (ZKPs)—a cryptographic method that lets you prove something is true without revealing the underlying data. Think of it like proving you’re old enough to enter a club without showing your actual birthdate. It sounds simple, but technically, it’s a huge leap.
What makes Midnight interesting isn’t just that it uses ZKPs—it’s how it builds an entire system around them.
Privacy Without Blindness
Traditional blockchains are like open books. Every transaction, every balance—visible to anyone. Midnight takes a different approach. It separates data into two layers: a public ledger for verification and a private execution layer where sensitive data stays hidden.
So instead of broadcasting everything, users generate proofs locally and only submit those proofs to the chain. The network checks the math, not your data. Your information never leaves your control.
That’s what “zero-compromise” really means here—you don’t sacrifice usability to get privacy.
The Dual-State Design (Where the Magic Happens)
Midnight’s architecture uses a hybrid model. On one side, you’ve got a UTXO-based public system handling consensus and security. On the other, there’s a private, account-based environment for running smart contracts.
These two worlds are connected through a protocol that allows private computations to be validated publicly using ZK proofs. In simple terms:
you do the work privately, and the blockchain just verifies that you did it correctly.
It’s a clever design because it avoids one of the biggest problems in privacy tech—scalability. Instead of overloading the chain with encrypted data, it only deals with lightweight proofs.
Selective Disclosure: Privacy With Control
Here’s where Midnight feels very “real-world ready.” It doesn’t force total secrecy. Instead, it lets you choose what to reveal.
You can prove compliance, identity, or transaction validity without exposing everything else. For businesses, this is huge. It means you can meet regulations without leaking sensitive data.
It’s not about hiding everything—it’s about controlling what matters.
The $NIGHT and DUST Model
Another interesting piece is its dual-token system. The NIGHT token handles governance and security, while DUST is used for private transactions.
Why split it? Because it reduces metadata leaks and keeps private activity truly private. Even transaction fees are handled in a way that avoids exposing patterns.
It’s a small design choice, but it shows how deeply privacy is baked into the system.
Final Thoughts
Midnight isn’t trying to be another “anonymous coin.” It’s aiming for something more practical—programmable privacy.
And honestly, that’s what makes it stand out. It acknowledges a simple truth: people don’t just want secrecy, they want control.
If blockchain is going to move into real-world use—finance, identity, even AI—this kind of architecture might not just be useful. It might be necessary. @MidnightNetwork #night $NIGHT