Usually, the mistake starts with the label. People hear “ZK-rollup” and think same engine, different paint. I did too, for a minute. Then the details ruin that lazy view. A general zkEVM like ZKsync is built to prove that Ethereum-style code ran the right way, then post enough public data back to Ethereum so the chain state can be rebuilt.
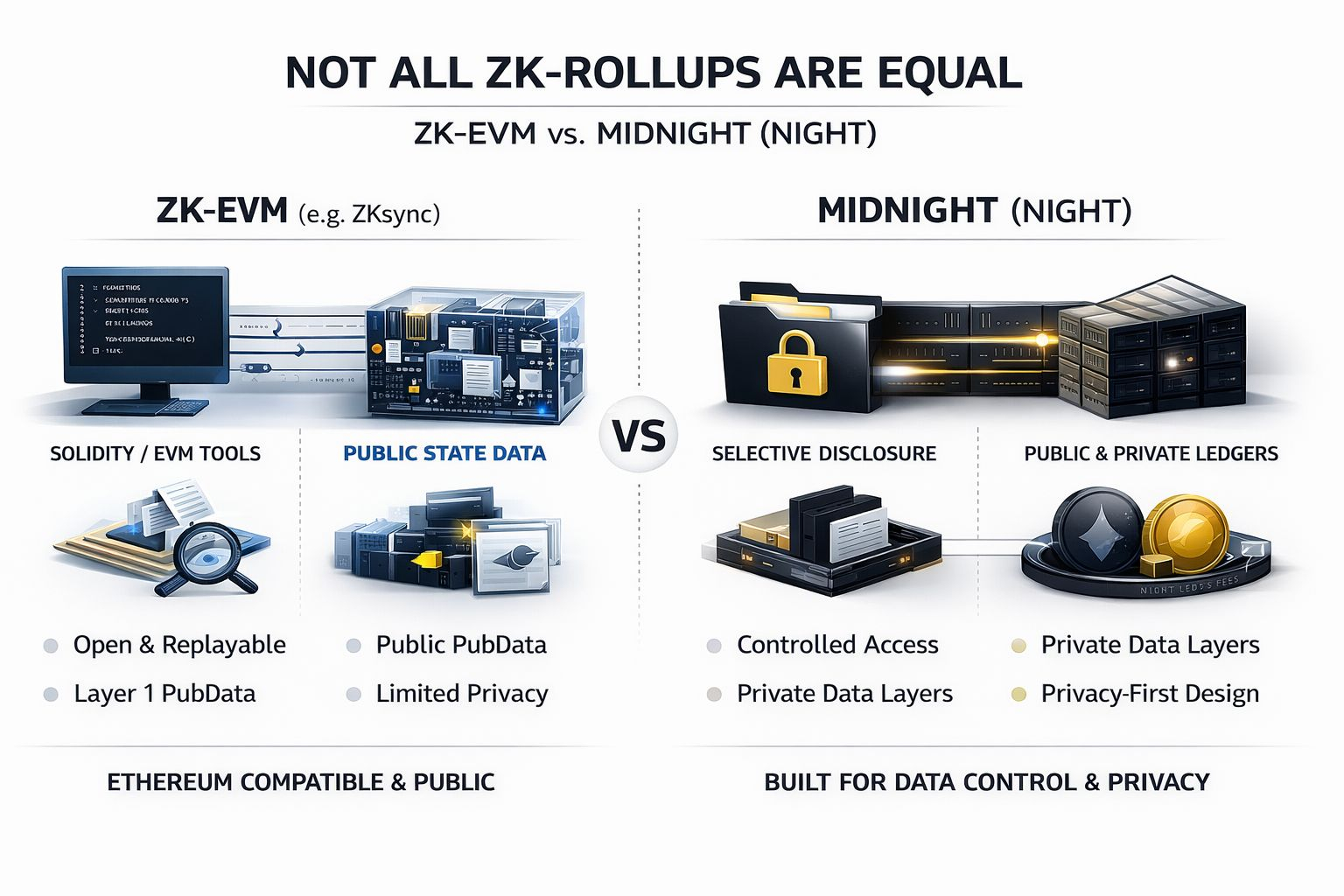
Midnight comes at the problem from a very different angle. Its docs talk about selective disclosure, private and public ledgers working side by side, and proving correctness without exposing the data itself.
Wait, let’s see what that means, One model asks, “How do I keep Ethereum habits and still scale?” The other asks, “How do I let people and firms use a chain without laying their files on the table?” Those are not small design tweaks. They shape what leaks, what stays hidden, and who really controls the data trail.
I keep coming back to one simple test is what does the base layer assume should be public? With ZKsync, the answer is pretty clear. The system is made to feel close to Ethereum: Solidity or Vyper, EVM tools, normal wallets, and public data availability so the full L2 state can be rebuilt from L1 pubdata and state diffs. Look, that is not a flaw by itself. It is a trade.
Upside is fast porting, lower dev pain, and broad app range. The downside is that privacy often gets pushed up to the app layer, where teams try to patch over a public machine with extra crypto, extra trust, or both. That tends to be where data sovereignty starts to slip. If the base system wants public traces to preserve shared state, then your control over who sees what becomes partial, not native. You may hide some content, sure. You do not fully own the leak surface.
Privacy, in Midnight’s case, looks less like a feature tab and more like the floor plan. Midnight says contracts can work across public and private ledgers, reduce transaction correlation, and use selective disclosure so a user proves what matters without dumping the full record. Its stack also leans on a UTXO base for privacy and parallel work, while still letting apps use account-style tokens through smart contracts. That mix matters more than the buzzwords.
Here is the real-life picture I use. A zkEVM often feels like running a clinic inside a glass office tower: you can frost the exam room door, but the building map, lift stops, and foot traffic still tell a story. Midnight feels more like a records room with sealed drawers and a sign-out slip. The guard checks that I had the right file. He does not read the file. Fine, that is not magic. It is just a better starting point for apps that deal with payroll, health, credit, or trade data.
Strip away the branding and even the fee design tells the same story. Midnight’s NIGHT token is the capital asset, while holding NIGHT generates DUST, a shielded and non-transferable resource used for fees and contract execution. I think that matters because cost and privacy are linked more than most market decks admit. On many chains, paying to use the network leaves its own public trail and invites the usual gas games.
Midnight’s model aims to split long-term value from day-to-day private usage. By the way, that does not make it pure, easy, or free from edge cases. It does show intent. The chain is trying to make private use a native path, not an afterthought. Put that next to selective disclosure and you get the core point: Midnight is not trying to be a better Ethereum clone with zero-knowledge paint on top. It is trying to make controlled disclosure a system rule.
NIGHT only makes sense if that rule matters. Okay, here is where I land after cutting through the slogans. Not all ZK-rollups are equal because the proof does not tell you the product goal. A zkEVM can be the right tool when you want broad EVM reach, public composability, and easy contract porting.
Midnight, tied to NIGHT and its DUST model, makes more sense when the real problem is data control: who can verify a fact, who can inspect a record, and how much of the trail must stay exposed. Personally, I trust purpose-built systems more when the use case is narrow and costly to get wrong.
I have seen too many teams say “we added privacy” when what they really added was one locked drawer in a glass house. Midnight may still have to prove adoption, tooling depth, and market fit. That part is real. Still, the architecture tells a cleaner story than most zkEVM pitch decks do: privacy first, then compute, then disclosure on purpose.
@MidnightNetwork #night $NIGHT
