
I kept trying to map $SIGN like it’s one thing—a chain, a protocol, just “attestations”—and it never sticks. Every time I look closer, it breaks apart into pieces that don’t sit in the same place. And that feels deliberate.
Sign isn’t really a chain. It’s more like a shared evidence layer sitting above execution, identity, and capital flows. That completely changes how you have to think about it.
Sure, the attestation is what everyone grabs first. It’s where eligibility looks settled, where approvals start feeling usable, where another system can finally read something and stop asking again. But trace it backward, and you won’t find one place where Sign “decides.” The attestation layer handles the final record—signatures, timestamps, structured data, status—while structure, logic, storage, query, and authority live elsewhere.
Schemas sit lower than most people realize. They’re not just formatting helpers; they define what claims can even exist. If input doesn’t fit, it never enters the evidence layer. So what are we really verifying later… the claim, or the fact it was allowed to exist?
Then there are schema hooks. This is where Sign stops being passive. Hooks run during attestation creation—they can inspect data, check whitelists, enforce payments, verify proofs, and just… revert the transaction if rules fail. No attestation, no record, nothing left behind. “Rejection without residue.” This is architecture, not an extension.
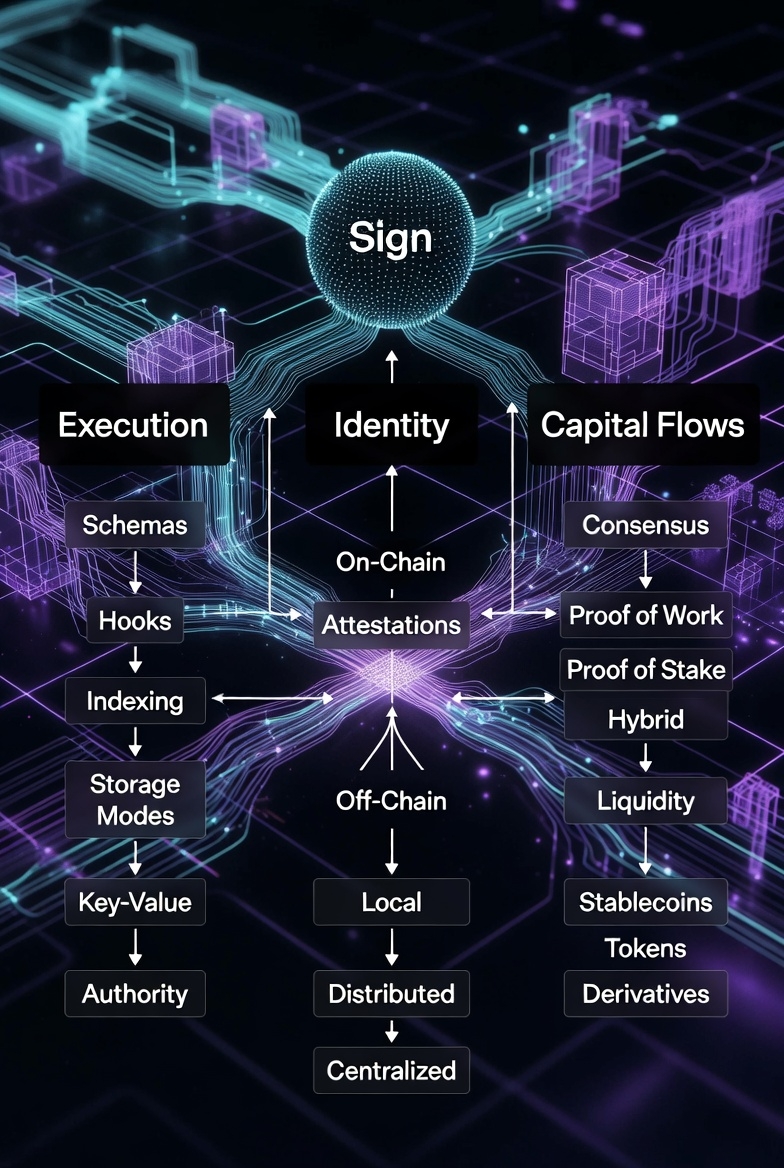
Storage is another split. Some attestations live fully on-chain, some off-chain with verifiable anchors, some hybrid. The point isn’t to keep everything together—it’s to keep evidence verifiable wherever it sits. Data location and verification aren’t the same question anymore.
Then there’s the infrastructure layer: Sign Scan and query interfaces recombine all this fragmented data into a readable surface. People see the explorer or API and think that’s the protocol. It’s not. The attestation created a record, storage anchored it somewhere, and infrastructure pulled it back together so audits, reporting, and compliance can actually work. Retrieval becomes a practical form of verification.
Above all is the trust layer. Sign doesn’t create authority—it captures it. Institutions, accredited authorities, off-chain organizations… they live outside the protocol. Sign makes their trust portable and usable inside applications. TokenTable, EthSign, identity or compliance systems—they don’t create the architecture. They just cash it out into real-world behavior: funds released, benefits denied, approvals accepted, programs executed.
Cross-chain makes it even more interesting. Evidence isn’t locked to one network. Sign uses decentralized TEEs and threshold signatures so verification can happen across chains without relying on a single trusted party. Fetch → decode → verify → threshold sign → push result on-chain. A clean pipeline, but with lots of moving parts.
Schemas, hooks, storage modes, indexing, authority, cross-chain consistency… all separate, all modular. And the attestation? That’s the moment everything briefly agrees. “Everything meets once… then disperses again.”
That’s why it looks simple on the surface but feels messy underneath. Sign didn’t simplify trust—it decomposed it, then recombined it just enough to make something portable, queryable, reusable. By the time you see the attestation, structure is set, rules executed, authority attached, data anchored, query layer ready. Simple, yes—but delayed.
At the center, it’s still just making a claim structured, signed, and verifiable. But Sign makes it practical: on-chain if you want maximum trust, off-chain if you want efficiency, hybrid if you need both. Schemas tie it together, zero-knowledge proofs hide private info, SignScan makes it searchable, TEEs make cross-chain verification possible.
It’s smart, it’s messy, it’s practical, and it actually works. Now the question is… how does it hold up under mainnet stress? Time will tell.
#SignDigitalSovereignInfra @SignOfficial $SIGN

