A lot of crypto projects are still being analyzed with the wrong lens. People ask the usual questions: Is the product clean? Is the UX good? Will users come? Does the token capture value? Those questions matter for normal crypto apps. I’m not sure they are enough here.What caught my attention with SIGN was not the headline claim, but the deeper assumption underneath it. This does not read like a simple product container. It reads more like an operating blueprint for systems that need to work under pressure, across agencies, across rules, and under public scrutiny. That is a different category of problem.@SignOfficial $SIGN #SignDigitalSovereignInfra
And once a project moves into that category, the standard crypto playbook starts to look shallow.The practical friction is obvious. Markets are very good at rewarding narratives that fit into familiar boxes. Wallet. Chain. Infra layer. Consumer app. Identity tool. But architecture is harder to price because architecture usually looks boring before it looks important. It shows up as process logic, control layers, deployment guidance, auditability, fallback rules, permission structure, and operational discipline. None of that creates instant excitement, but those are exactly the things that matter if the target environment is closer to sovereign infrastructure than startup software.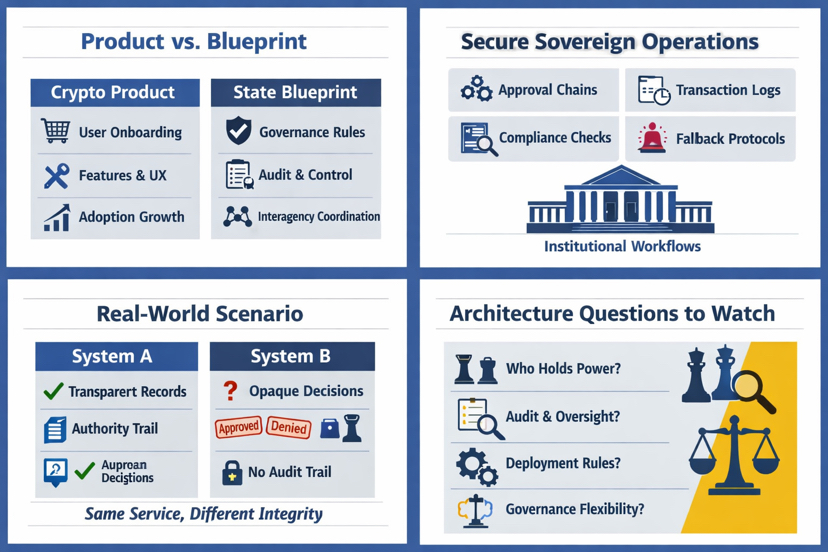
That is why I think SIGN should be analyzed as architecture, not marketing.My basic claim is simple: projects framed as products are judged by adoption curves, feature polish, and surface usability; projects trying to define state-grade operating models should be judged by whether their structure can handle legitimacy, coordination, scale, and accountability. That is a much harder standard. It is also a much more interesting one.
The mechanism here is not just “build a tool and hope institutions adopt it.” The mechanism is closer to defining a container for how sensitive digital processes can be governed. In other words, the real product may not be the interface at all. It may be the operating logic underneath: who can approve what, how records move, how permissions are bounded, how changes are logged, how disputes are reviewed, and how deployment can happen without every implementation becoming a custom political negotiation from zero.
That matters because sovereign-grade operations do not fail the same way normal apps fail.If a consumer crypto app breaks, users get annoyed, maybe funds pause, maybe volume drops. Bad outcome, but still local.If a state-linked system breaks, the damage is wider. Records can slowly fall out of sync, and approval paths can become hard to trace.Different institutions can read the same event differently. A process can continue functioning on the surface while legitimacy decays underneath. That is the failure mode I think people underestimate.
This is where the “blueprint versus product” distinction becomes useful.A product is usually a bounded thing. You ship features. You improve onboarding. You reduce friction. You watch retention. A blueprint is different. A blueprint tells operators how a system should be instantiated, controlled, and trusted in environments where the deployment context matters as much as the code. It is less about one app winning users and more about whether multiple actors can coordinate around the same rules without losing accountability.
That is also why deployment guidance matters so much here. In normal crypto analysis, deployment is often treated as a secondary detail, almost operational housekeeping. For something like SIGN, deployment guidance may be part of the core architecture itself. If a system is meant to support sovereign or public-grade workflows, then questions like validator structure, control boundaries, upgrade authority, audit visibility, interoperability assumptions, and emergency procedures are not footnotes. They are the design.
I think crypto markets still struggle with that. They often reward what can be narrated quickly. Architecture resists quick narration. It tends to look abstract until a real institution needs it. Then suddenly the boring parts become the whole story.
A simple real-world scenario makes the difference clearer. Imagine two digital public systems. Both let a citizen submit a request online. Both show a modern interface. Both provide status updates. On the surface, they look equally advanced. But underneath, one system can show exactly which authority reviewed the request, under what rule set, with what permission scope, with what timestamped record transition, and with what appeal path if the decision is contested. The other system just says “approved” or “denied” and leaves the deeper chain opaque. From a product perspective, both may feel similar. From an architectural perspective, they are worlds apart.
That is why I hesitate when crypto discussions reduce projects like SIGN to branding, UX, or market positioning. Those things are visible, so they dominate attention. But in institutional systems, visibility is not the same thing as integrity. A polished front end can improve convenience. It cannot manufacture legitimacy after the fact.
The reason this matters for crypto is bigger than one project. If blockchain infrastructure wants relevance beyond speculation and retail coordination, it has to prove it can support environments where accountability is not optional. That means moving from “can this app work?” to “can this operating model remain governable under real institutional load?” Those are not the same question.
There is a tradeoff, though, and I think it is an important one. The more a project aims for sovereign-grade operability, the more it may inherit the complexity of sovereign systems themselves. More controls can mean slower execution. More governance can mean more negotiation. More deployment rigor can mean less composability and less speed than crypto users are used to. So the architectural ambition is interesting, but it can also pull a project away from the simplicity that makes products easy to adopt.
That is what I’m watching next.Not whether the messaging gets cleaner. Not whether the surface pitch becomes more appealing. I want to see whether the architecture can be explained in operational terms that survive contact with real deployment constraints. Who holds power in the model? Who audits whom? What gets standardized, and what remains politically configurable? Where does flexibility end and institutional drift begin?
Those questions are less exciting than narrative cycles. They are also more durable.SIGN may be one of those cases where the market’s first instinct is too small for the object being analyzed. If the real value sits in architecture, markets may misread it for a while because architecture does not perform well as a headline. It performs later, when systems are stressed and weak operating models start to break.
Are crypto markets good at pricing architecture, or only narratives?@SignOfficial $SIGN #SignDigitalSovereignInfra 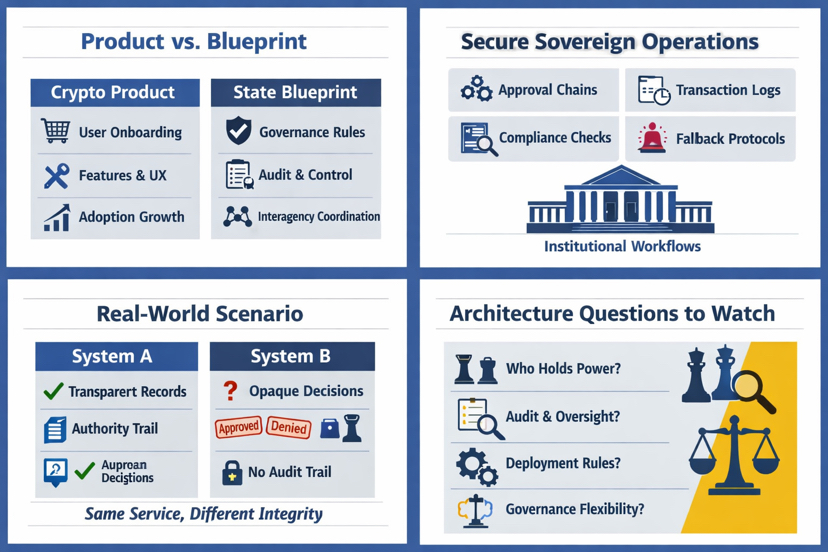
Artigo
SIGN Looks More Like State Architecture Than a Crypto Product
Aviso Legal: inclui opiniões de terceiros. Não se trata de aconselhamento financeiro. Poderá incluir conteúdos patrocinados. Consulta os Termos e Condições.
0
19
177
Fica a saber as últimas notícias sobre criptomoedas
⚡️ Participa nas mais recentes discussões sobre criptomoedas
💬 Interage com os teus criadores preferidos
👍 Desfruta de conteúdos que sejam do teu interesse
E-mail/Número de telefone
