There was a moment when I was experimenting with a contract call that didn’t go through. I had passed the wrong parameter, nothing serious, just part of testing. but when I checked the chain afterward, the failed attempt was fully visible not just that it failed, but what I tried to do. the inputs, the structure, even the mistake itself were all there.
after seeing this happen a few times, it started to change how I think about transparency. in most blockchain systems, verification and exposure come together. if something happens whether correct or incorrect it becomes part of the public record. that works well for trust, but it also means faulty data carries the same visibility as valid data.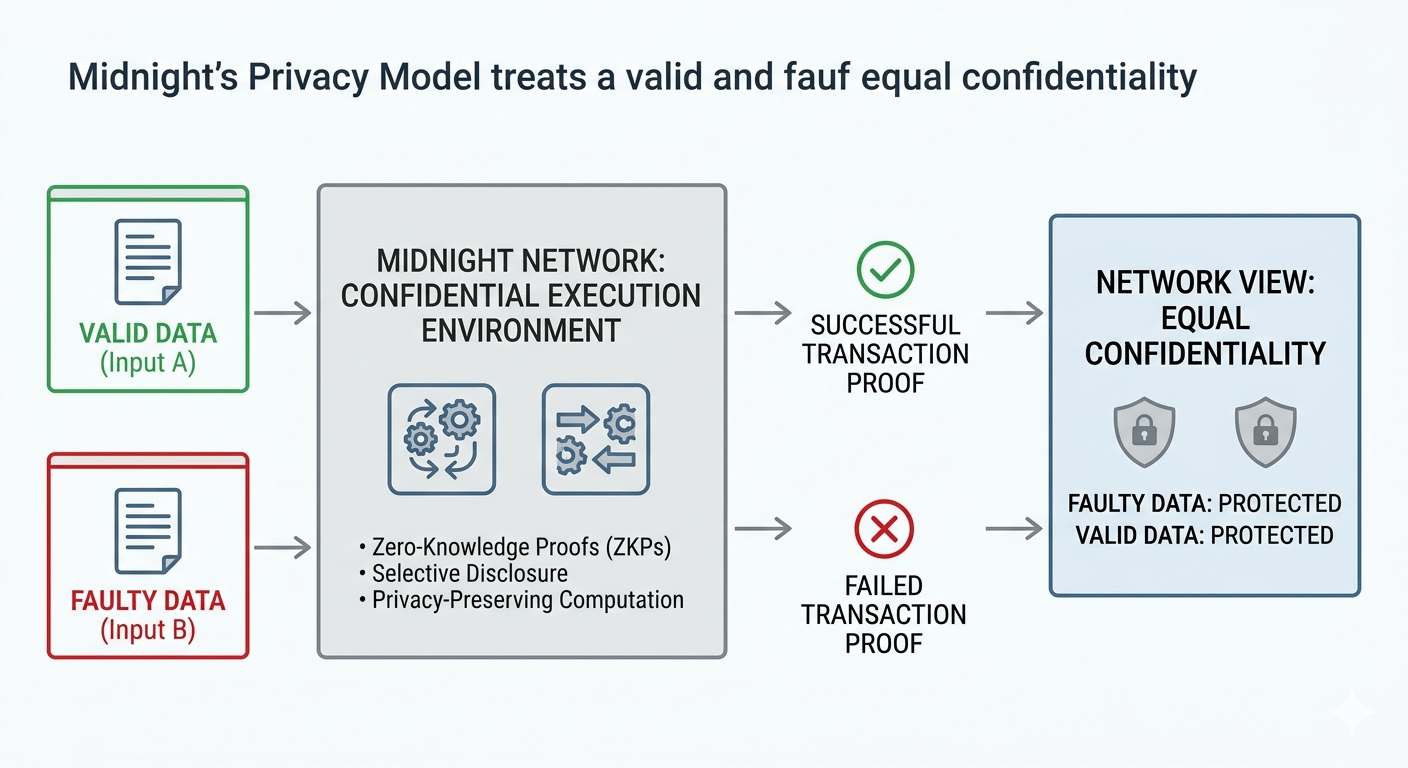
from a system perspective, that creates an interesting imbalance. verification requires openness, but not all data needs to be exposed to achieve that. invalid transactions, failed contract executions, or incomplete logic still reveal patterns. over time, these patterns can expose behavior, experimentation paths, and even developer intent.
I tend to think of it like submitting documents for approval. the system needs to confirm whether your submission meets the criteria, but it doesn’t need to display every rejected draft publicly. the outcome matters, but the intermediate attempts don’t always need to be visible.
when I look at Midnight’s design, what caught my attention is how it approaches this exact problem. the network is built around privacy preserving computation, where data can be validated without being publicly revealed. instead of exposing raw inputs or execution details, Midnight focuses on proving whether conditions are satisfied.
what I noticed is that this approach naturally extends to both valid and faulty data. whether a transaction succeeds or fails, the underlying information remains shielded. the system doesn’t create a distinction where incorrect data becomes more visible than correct data. both are treated with the same level of confidentiality.
from an architectural standpoint, this relies on a combination of selective disclosure and confidential execution environments. smart contracts can run in a way where their logic is enforced, but their inputs and intermediate states are not exposed to the entire network. what gets revealed is the proof of correctness not the full trail of how that result was reached.
in my experience watching networks, consistency here is critical. if a system protects successful outcomes but leaks failed ones, it still exposes meaningful signals. what matters in practice is that both states appear indistinguishable from the outside. otherwise, the difference itself becomes a source of information.
this also changes how developers and users interact with the system. experimentation becomes less risky from a privacy standpoint. testing edge cases or iterating on logic doesn’t automatically create a public record of every misstep. at the same time, the network can still verify correctness and maintain integrity.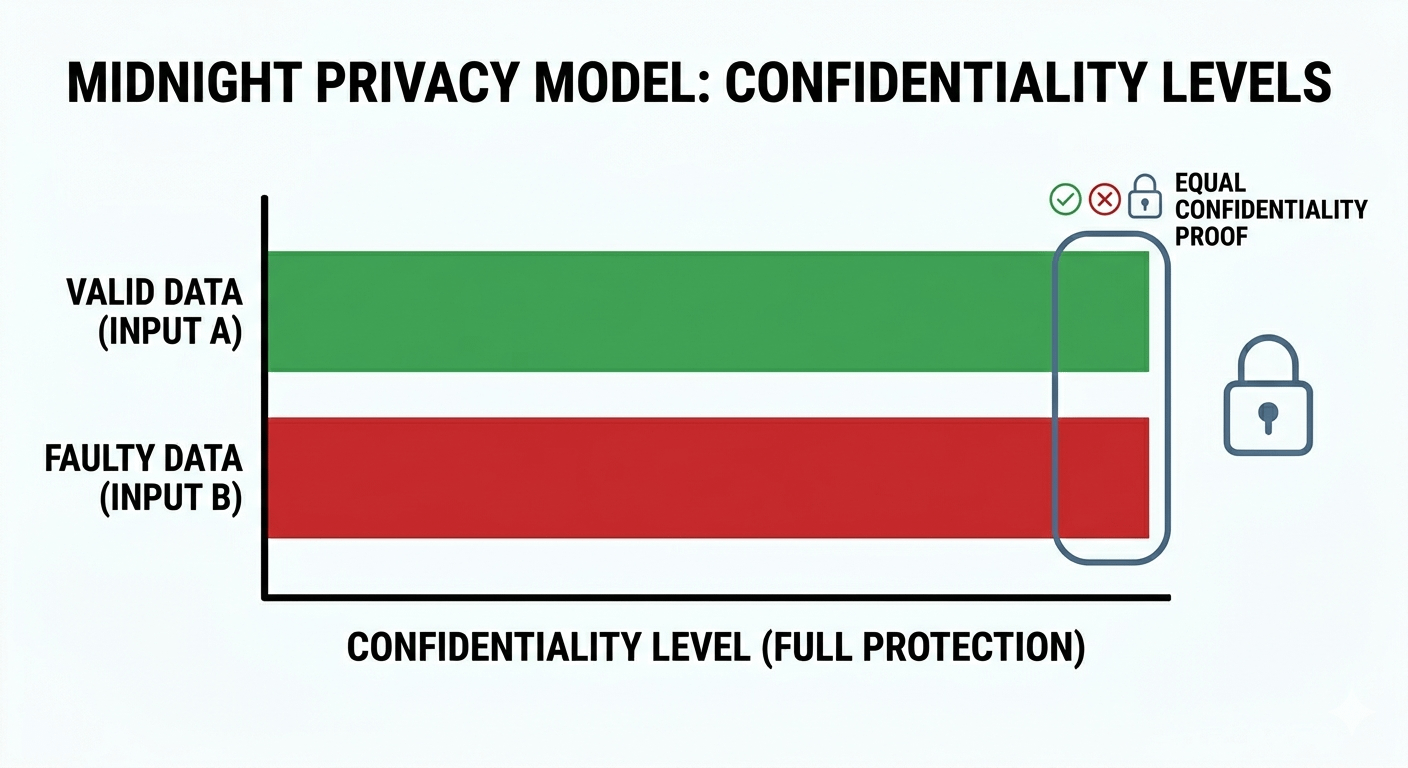
what interests me more is how this balances privacy and trust. Midnight doesn’t eliminate verification it restructures it. instead of exposing everything to prove correctness, it limits visibility to what is strictly necessary.
and that’s where the design feels thoughtful. not because it hides data completely, but because it removes the assumption that faulty data should be publicly observable by default.
a reliable system is not the one that exposes every detail for the sake of transparency, but the one that proves what needs to be proven while keeping everything else valid or faulty equally protected.