Was going through some notes on SIGN Protocol last night… initially just trying to understand where $SIGN actually fits, and why people keep framing it as “credential infra” plus token distribution rails.
at surface level, it looks straightforward: a system to issue, verify, and manage onchain/offchain credentials. badges, attestations, eligibility proofs — that kind of thing. paired with token distribution, it reads like a cleaner airdrop tool. nothing too deep, right?
but that’s not the full picture.
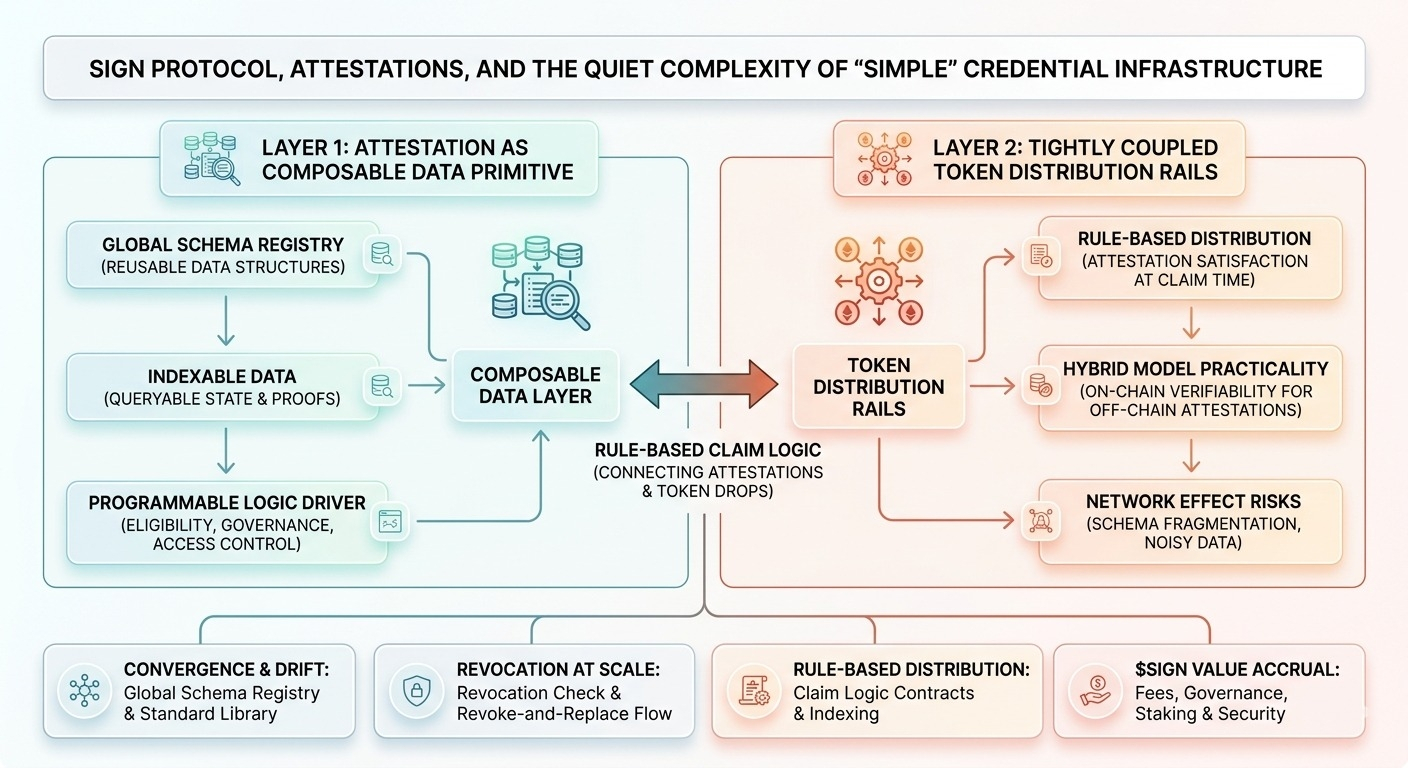
what stood out is how SIGN is really leaning on attestations as a primitive — not just static credentials, but composable, queryable data structures. the attestation registry design (especially if you look at how schemas are defined and reused) starts behaving more like a shared data layer than just a credential store. and that’s where it gets interesting… because once attestations are standardized and indexable, they can drive logic elsewhere — eligibility checks, governance weighting, even offchain access control.
then there’s the token distribution side. on paper it’s “fair drops” or “verified claims,” but under the hood it’s tightly coupled with those attestations. instead of distributing tokens to wallets, you’re distributing based on state — who satisfies which conditions at claim time. it shifts distribution from snapshot-based to rule-based. subtle difference, but operationally very different.
also worth noting the cross-chain / offchain angle. SIGN doesn’t try to force everything onchain — it allows attestations to exist offchain with verifiable proofs anchored onchain. that hybrid model is practical… but also introduces trust surfaces. who runs the attesters, how revocation works, how consistency is maintained across environments — still a bit fuzzy.
some of this is already live — basic attestation flows, credential issuance, simple distribution campaigns. you can see teams using it today. but the more ambitious pieces — like deeply composable identity layers or universal credential portability — feel more like phased intent than reality.
and i guess that’s where my hesitation sits. systems like this depend heavily on standardization and network effects. if schemas fragment, or if attestation quality varies across issuers, the whole thing risks becoming noisy pretty fast.
also… who actually verifies the verifiers?
curious about:
* whether attestation schemas converge or drift across ecosystems
* how revocation and updates are handled at scale
* real usage of rule-based distributions vs traditional snapshots
* whether $SIGN accrues value from usage… or just coordinates it.
$SIGN @SignOfficial #signdigitalsovereigninfra