I was comparing two credentials this morning and something didn’t line up.
Same fields.
Same structure.
Different schema IDs.
I checked the first one.
Valid. Issuer active. Everything resolving cleanly.
I checked the second.
Same result.
Both passed.
Both looked identical.
So I tried something simple.
I ran a verification against the first schema ID using the second credential.
Nothing came back.
No error.
Just nothing.
I checked the registrant addresses.
Different.
Same structure registered twice.
By two different addresses.
Two schema IDs.
At first I thought I pulled duplicate records.
So I traced each one back to its registration.
They weren’t duplicates.
They were separate registrations.
Same fields.
Same intended structure.
Completely independent.
I had to go back and check I wasn’t missing something obvious.
That didn’t sit right.
Because from the outside, nothing separated them.
Same data.
Same format.
Same behavior inside their own schema.
But a verifier checking against one schema ID would never recognize a credential issued under the other.
I stayed on it longer than I meant to.
Checked how many credentials existed under each schema.
Not a small number.
Two populations.
Issued under schemas that looked identical.
Unable to cross-verify.
That didn’t sit right.
That’s where I stopped assuming this was just a duplicate.
For a second I thought this was a one-off registration mistake.
Then I checked another pair.
Same pattern.
That’s when it clicked.
Schema fork.
Two independent credential populations.
Identical structure.
Different registrant.
Different ID.
No bridge between them.
From the outside they’re indistinguishable. From inside the verification layer they’ve never met.
I kept going.
I wanted to see where this actually showed up.
The first place I noticed it was access.
The verifier never needed the content.
The schema was enough.
And the decision happened anyway.
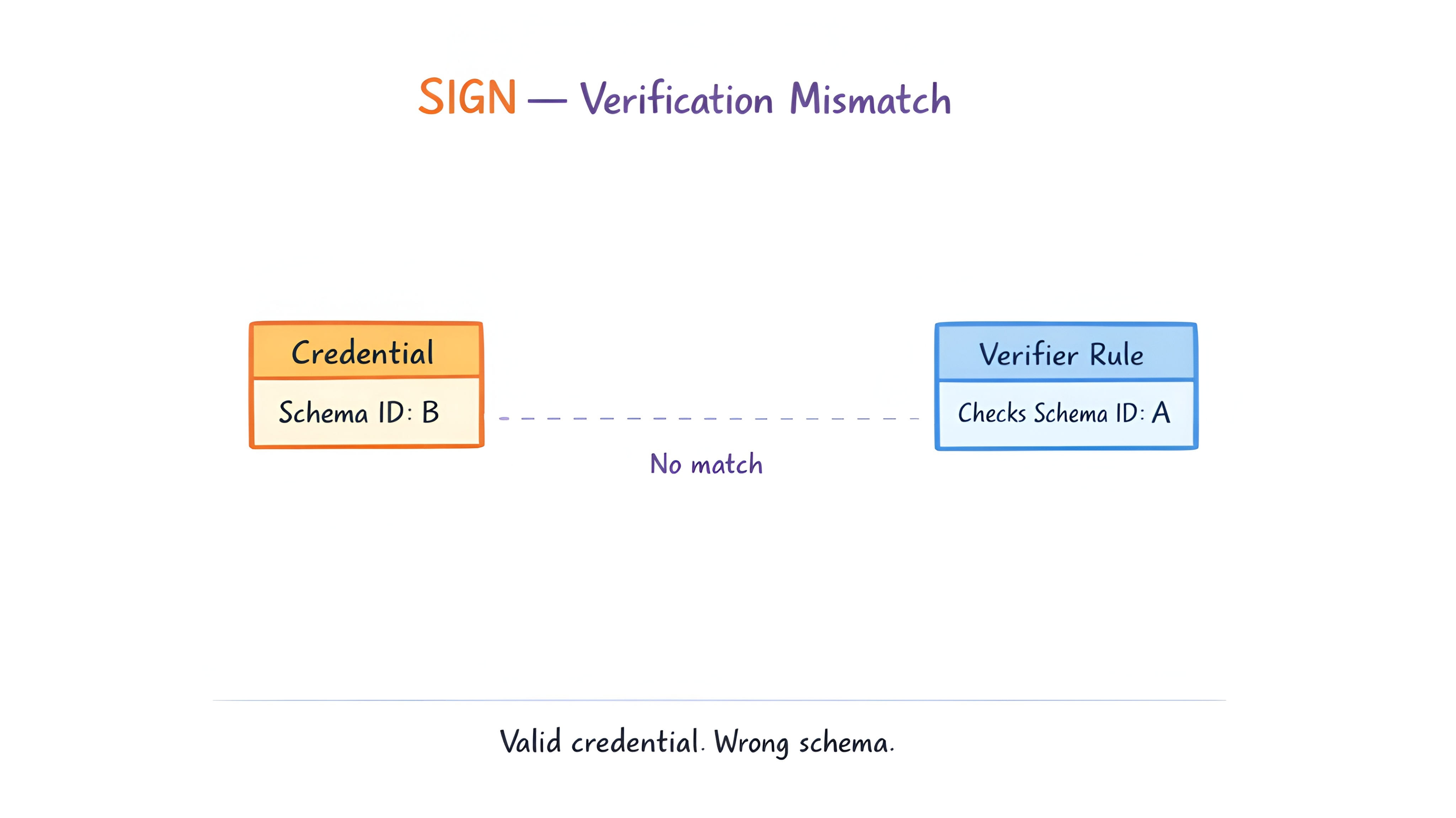
A condition checks against one schema ID.
A credential issued under the other doesn’t register.
Not because it’s wrong.
Because the verifier is reading a different fork.
The decision still happens.
Just against half the picture.
That stayed.
Then distribution.
A distribution gated by schema-specific attestations runs cleanly.
One population passes.
The other never even appears.
Not excluded by design.
Just… not seen.
The credentials exist.
The schema being checked just isn’t theirs.
Couldn’t ignore it.
Then trust.
Two issuers building toward what looks like the same schema.
Same fields.
Same intent.
One issuer recognizes a credential immediately.
The other runs the same check and gets nothing back.
Both think they’re working on the same standard.
They’re not.
They’ve forked without realizing it.
One accepts.
One rejects.
Same credential.
Different outcome.
I checked a few more schema registrations after that.
Looked for structural overlap across different registrants.
The pattern showed up more than I expected.
Not everywhere.
But enough.
Especially where multiple issuers were building toward the same use case.
That’s when it stopped feeling like a registration mistake.
And started looking like a structural pattern.
$SIGN only matters here if two schemas with identical structure but different registrants can be recognized as equivalent by the verification layer without either side having to rebuild from scratch.
Because right now the fork is silent.
Nothing in the attestation tells you which population you’re looking at.
And every eligibility check that passes one fork and misses the other is making a decision on incomplete information.
How many credential holders right now are failing verification not because their credential is wrong… but because the verifier is reading a different fork of the same schema?
#SignDigitalSovereignInfra #Sign


