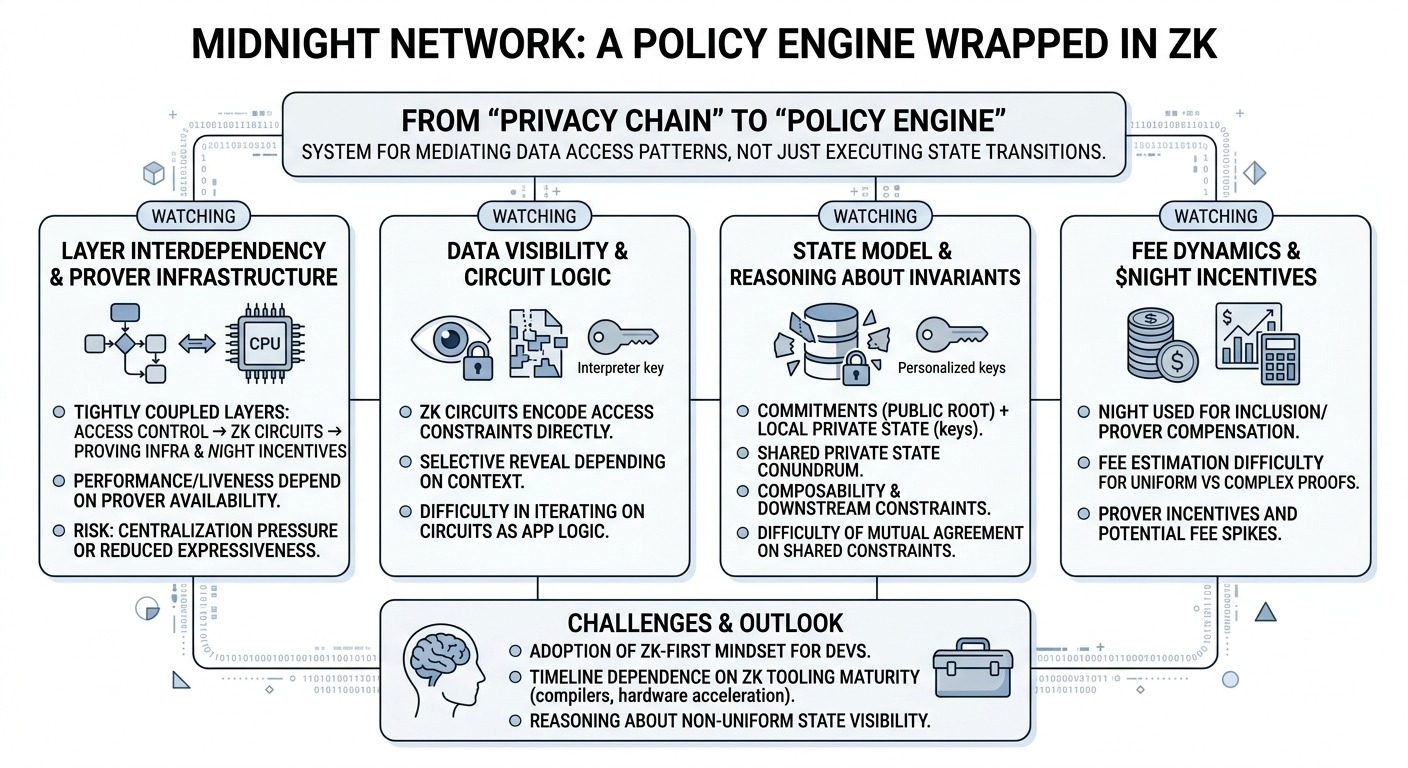
Been going through midnight’s architecture and honestly… i don’t think calling it a “blockchain with privacy” really captures what’s happening. it feels closer to a system where zk is being used to enforce policies over data, not just validate transactions. which is subtle, but changes how you think about the whole stack.
the oversimplified take is: “users keep their data private, zk proves correctness, done.” but that skips over the fact that midnight is trying to make data flows conditional. not just hidden vs visible, but selectively revealed depending on context. and that means the protocol isn’t just executing state transitions — it’s mediating access patterns.
first thing that stands out is how zk circuits are doing more than validation. they’re encoding access constraints directly. so instead of a contract checking permissions at runtime, the proof itself guarantees that only certain outputs are exposed. that’s real, not hypothetical — we’ve seen similar patterns elsewhere. but the catch is circuit design becomes application logic. and circuits aren’t easy to iterate on. once deployed, changing access rules might mean reworking the proving logic entirely.
second, the state model. i think this is where things quietly get complicated. if state is stored as commitments and users hold keys to interpret slices of it, then “state” isn’t a single globally readable object anymore. it’s more like a shared root with personalized projections. that’s powerful, but also awkward. how do you reason about invariants if different actors see different subsets? like, does every participant agree on the same constraints, even if they don’t see the same data?
third, the proving layer. execution is effectively outsourced to whoever can generate proofs. validators just check them. which means performance and liveness depend heavily on prover availability. if generating a proof for a complex transaction takes seconds (or longer), then UX suffers. and if only a few actors can afford to run high-performance provers, you get centralization pressure — even if the validator set is decentralized.
fourth, incentives via $night. i assume it’s used to pay for transaction inclusion and maybe compensate provers. but zk costs aren’t uniform. a simple proof and a complex one might differ by orders of magnitude in compute. pricing that correctly is tricky. either users overpay for simple actions, or provers avoid complex ones unless fees spike. neither is ideal.
what i don’t see discussed enough is how tightly coupled these layers are. access control depends on zk circuits, which depend on proving infrastructure, which depends on economic incentives. if one layer underperforms, the others inherit the problem. for example, if proving is slow, developers might simplify circuits, which reduces the expressiveness of access control.
there’s also an implicit assumption that developers will adopt a zk-first mindset. not just writing contracts, but thinking in terms of proofs, visibility scopes, and constraint systems. that’s a non-trivial shift. most devs today rely heavily on transparent state for debugging and composability.
composability itself feels like an open question. if contract A reveals partial data to contract B, what prevents B from exposing it further? is there a protocol-level mechanism to enforce downstream constraints, or is that left to contract logic? if it’s the latter, privacy guarantees might degrade at integration boundaries.
timeline-wise, this feels dependent on zk tooling maturing — better compilers, faster proving, maybe hardware acceleration. without that, midnight risks being technically sound but practically difficult to use.
a concrete example: imagine a payroll system where employees prove eligibility for bonuses without revealing salaries. clean idea. but then auditing, dispute resolution, cross-contract integrations — all of those require different visibility levels. coordinating that without leaking data or duplicating proofs gets complicated quickly.
so yeah, i’m not entirely sure how to categorize midnight. it’s not just a privacy chain, and not quite a general-purpose L1 either. it’s something in between — a system for controlling how data moves through contracts.
watching:
* whether prover infrastructure becomes a bottleneck or commoditizes
* how they enforce or model data visibility across contract boundaries
* developer tooling for building and debugging zk-based access logic
* fee dynamics for complex vs simple proofs
i keep wondering if the real challenge here isn’t the cryptography… but whether developers and users can actually reason about a system where “state” isn’t uniformly visible anymore.
$NIGHT @MidnightNetwork #night