My main view on $SIGN is pretty simple: the interesting part is not the slogan, it’s the attempt to turn digital claims into reusable, verifiable infrastructure. In crypto, we already have plenty of ways to move assets, but we still don’t have a clean universal way to prove eligibility, approvals, credentials, or actions across different apps and systems. That’s why Sign stands out more to me as infrastructure than as a pure market story.
I’m anchoring this note to the latest public metrics I could verify from official docs and Binance Research, rather than pretending I have fresher data than the market does.
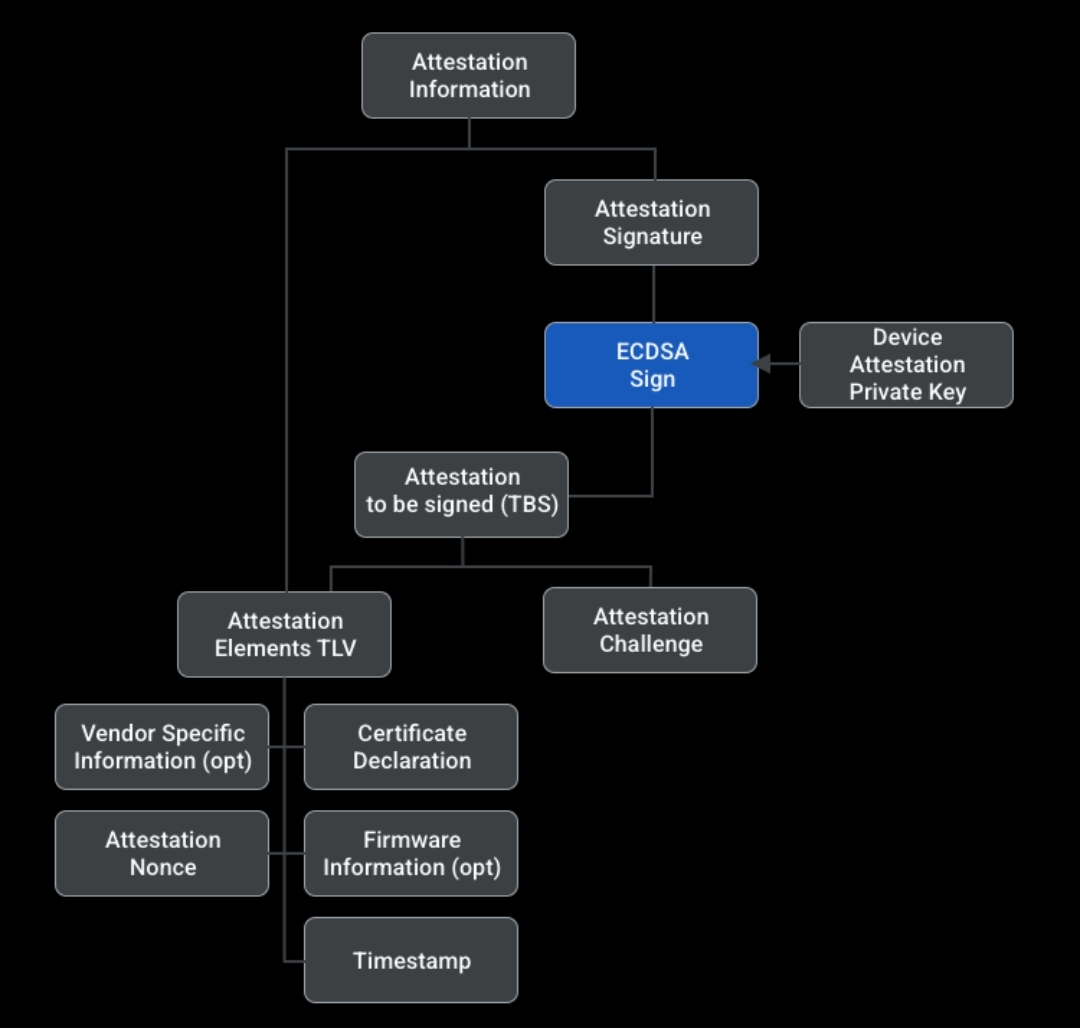
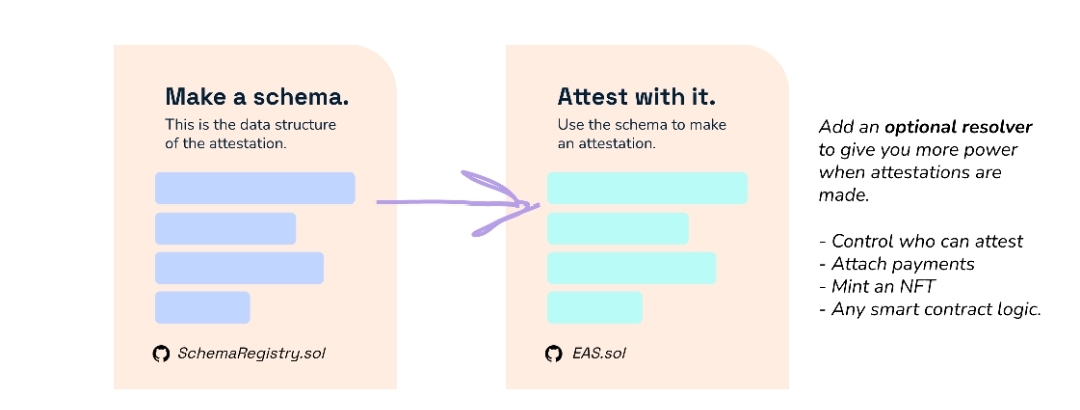
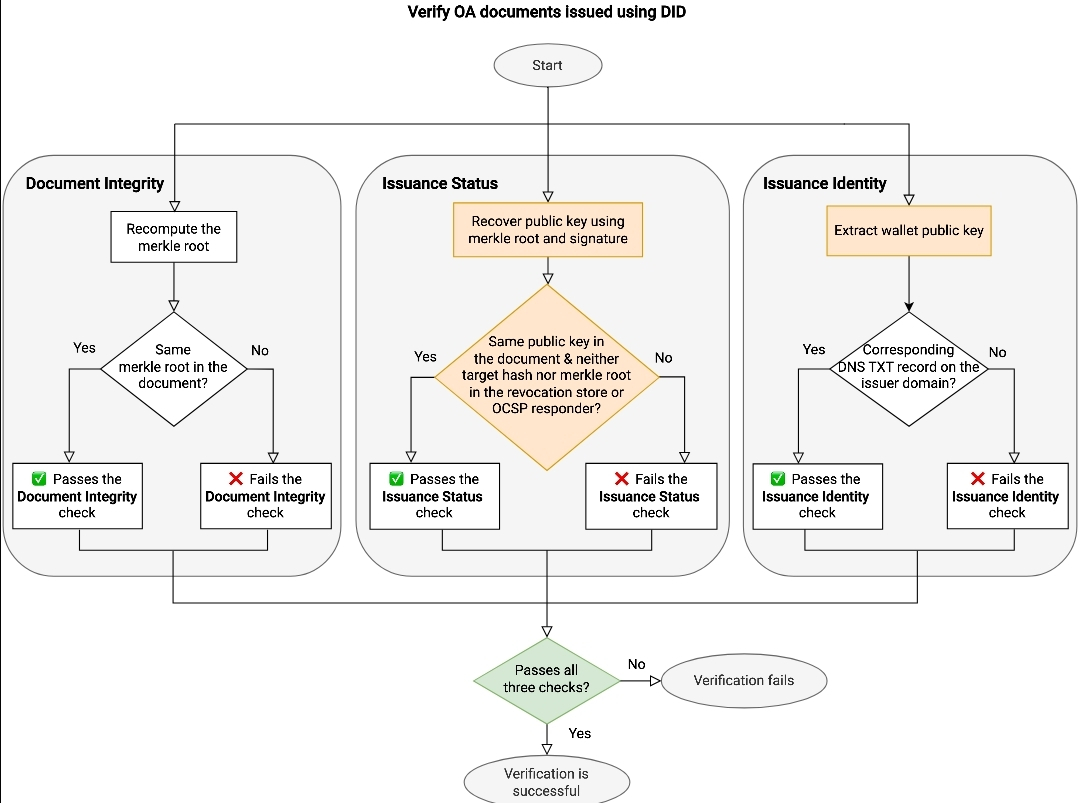
Sign Protocol is described in the docs as the cryptographic evidence layer of the S.I.G.N. stack. Its core building blocks are schemas and attestations: schemas define the structure, field types, validation rules, and versioning, while attestations are signed statements that can be public, private, ZK-based, or cross-chain.

That matters because “proof” in Web3 usually breaks when the format is inconsistent. If one app treats a claim as a PDF, another as a backend entry, and a third as a wallet tag, nothing composes well. Sign’s design tries to fix that by making claims machine-readable, verifiable, and queryable through REST, GraphQL, and SDKs.
This is where I think the project gets more serious. Sign is not only about making data visible; it also supports public, private, and hybrid attestations, and Binance Research says the stack uses asymmetric encryption and zero-knowledge proofs to redact sensitive information while keeping records provable.
One example Binance Research gives is proving age or country of residence from a passport scan without the raw passport data leaving the device.
Still, I’d be careful not to over-romanticize the tech. An attestation framework does not magically make bad inputs trustworthy. The quality of the schema, the credibility of the issuer, and the conditions around revocation or updates still matter a lot, even if the record itself is cryptographically clean.
The strongest bullish argument, in my opinion, is that Sign already has usage metrics people can inspect. Binance Research says schema adoption grew from 4,000 to 400,000 in 2024, while attestations increased from 685K to more than 6M.
The same report says TokenTable has distributed over $4B to 40M+ wallets, and that Sign generated $15M in revenue in 2024.
There are also real-world deployment claims behind the story. Binance Research says Sign is live in the UAE, Thailand, and Sierra Leone, with active expansion into more than 20 countries.
On the product side, the docs also show concrete use cases around benefits eligibility, compliance-gated services, approved distributions, and auditable registry updates.
A case study that caught my eye was ZetaChain’s KYC-gated airdrop flow. Sign’s docs say TokenTable helped distribute 17,789,923 ZETA worth about $29.7M, with 12,858 users passing KYC and a reported median verification time of 14 seconds.
That doesn’t prove mass consumer adoption by itself, but it does show the system being used for a specific high-friction workflow where proof quality actually matters.
The biggest risk is still adoption-to-token translation. Binance Research is clear that $SIGN is the native utility token across the ecosystem, but strong product usage does not always flow neatly into sustainable token demand.
I also think investors should watch for execution risk around government-facing narratives, because those cycles are slower, more political, and harder to model than standard crypto app growth.
There’s a second risk too: the market can get excited about “digital identity” as a broad theme before checking whether the most important schemas and issuers are becoming real standards. If that standardization layer doesn’t deepen, growth can look impressive without becoming truly defensible.
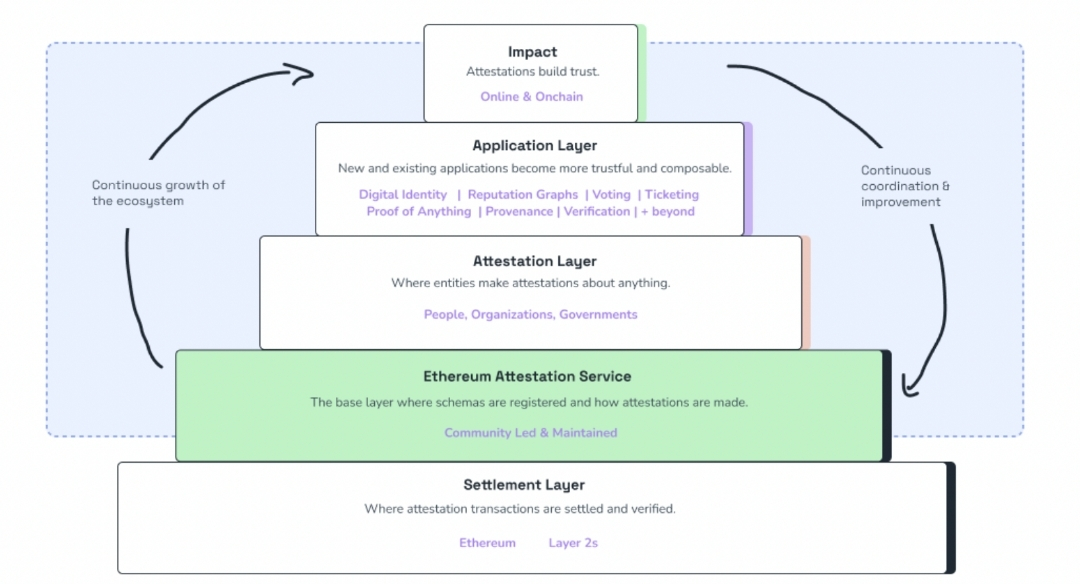
What stands out to me is that Sign feels more credible when I judge it like backend infrastructure, not like a retail-facing app token. The mix of schema growth, attestation growth, TokenTable scale, and actual revenue gives it a stronger base than the average narrative-heavy infrastructure project.
Where I’d stay cautious is simple: I want to see the next round of verifiable usage data, not just replay the same 2024 numbers forever. For now, I think the upside case is real because the product solves a genuine proof problem, but the market still needs evidence that this verification layer becomes sticky enough to matter beyond one campaign, one airdrop cycle, or one hot narrative.
My bias here is simple: I trust usage metrics more than slogans. Are you looking at $SIGN as infrastructure first, or mainly as a narrative trade?

