A lot of people treat credential-based systems as if they automatically make Web3 better. I think the reality is more complicated than that.
The promise sounds strong: reduce fraud, improve distribution, and make eligibility easier to prove. On paper, that makes sense. Ecosystems do need better ways to decide who qualifies, who should receive incentives, and who can access certain products or services. Without that, sybil attacks, fake participation, and inefficient token distribution remain constant problems.
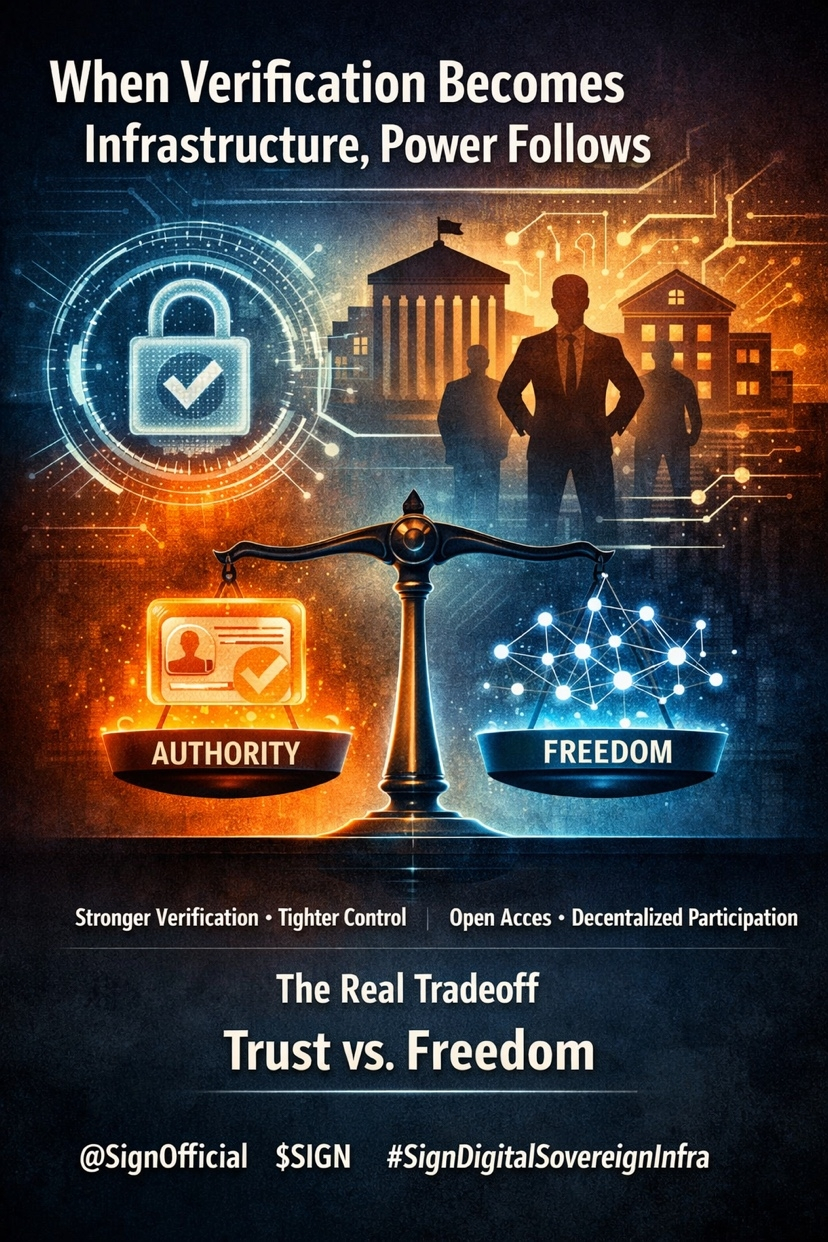
But the deeper issue begins the moment verification stops being a tool and starts becoming infrastructure.
Once a system depends on attestations, it also depends on issuers, standards, and trust assumptions. That is where the discussion becomes more uncomfortable. Who decides which credentials matter? Who is allowed to issue them? Who verifies whether an attestation is valid? And just as importantly, who gets excluded when those rules become tighter?
That is why this is not only a technology question. It is also a governance question.
A credential layer can absolutely improve efficiency. It can reduce spam, filter fake users, and make distribution more targeted. But it can also move Web3 closer to a model where access depends on recognized authorities, approved issuers, and predefined standards of legitimacy. That may improve order, but it also introduces a form of control that many people originally came to crypto to avoid.
This is the real tradeoff.
A cleaner system usually requires stronger identity signals. Stronger identity signals usually require trusted intermediaries. And trusted intermediaries, even when useful, always introduce some degree of centralization. The system may become more practical, but it may also become less open.
That does not mean the model has no value. It means its success depends on whether it can improve coordination without simply rebuilding Web2-style gatekeeping in a new wrapper.
In my view, that is the real test. If this kind of infrastructure helps verify eligibility without making participation feel permissioned, it could become meaningful. But if verification turns into a new form of access control dominated by a small set of accepted issuers, then one weakness may be solved by creating another.
The hardest problem is not proving who belongs.
It is doing so without making openness disappear.