Was reading through the SIGN protocol litepaper and a few repo examples earlier, mostly trying to map where it actually sits in the stack. initially it feels pretty straightforward — credentials in the form of attestations, then some logic to distribute tokens based on those credentials. kind of like formalizing what teams already hack together before launches.
and i think that’s the default mental model. people see “credential verification + token distribution” and assume it’s just a cleaner airdrop pipeline. define eligibility, run checks, send tokens. done.
but that’s not the full picture.
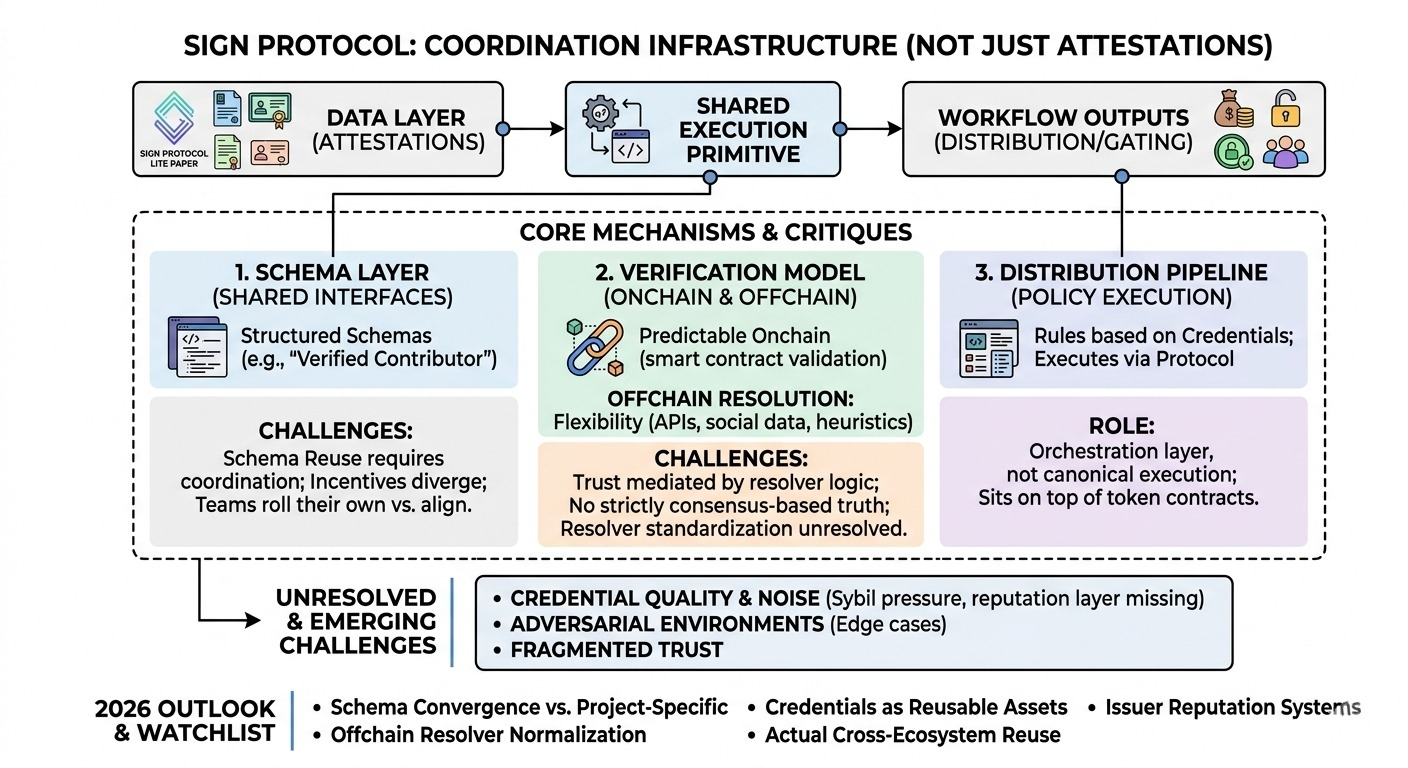
the deeper thing SIGN is doing is trying to turn credentials into a shared execution primitive, not just a data record. instead of attestations being passive (something you query), they become active inputs into workflows — especially distribution. and once you do that, you’re no longer just storing claims, you’re coordinating outcomes.
first mechanism that stands out is the schema layer. SIGN leans heavily on structured schemas for attestations — not just arbitrary key/value blobs, but predefined formats that describe what a credential represents. on paper this looks like standard data modeling, nothing special.
but here’s the thing — if schemas are reused across applications, they start acting like shared interfaces. a “verified contributor” schema in one ecosystem could, in theory, be consumed by another without translation. that’s a big assumption though. schema reuse requires coordination, and coordination tends to break down once incentives diverge.
some of this is live. projects are already issuing attestations against schemas and using them internally. but cross-project composability still feels more like a promise than a reality. i don’t see strong evidence yet that teams are aligning on shared schema definitions instead of rolling their own slight variations.
second is the verification model, which is more nuanced than it looks. SIGN supports both onchain verification and offchain resolution. onchain is predictable — you can validate attestations directly via contracts. offchain is where flexibility comes in: pulling in external data, APIs, social signals, whatever.
and that’s where it gets interesting. once you allow offchain resolvers, you introduce a layer where truth isn’t strictly consensus-based anymore. it’s mediated by whoever runs the resolver logic. two systems could technically “verify” the same credential differently depending on how they resolve external dependencies.
this isn’t necessarily a flaw — it’s probably required for real-world use cases — but it does mean the trust model is more complex than “it’s onchain so it’s correct.” parts of this are already operational, especially in eligibility checks that depend on offchain heuristics. but standardizing resolver behavior, or even defining what guarantees they should provide, feels unresolved.
third piece is the distribution pipeline, which is arguably the most concrete today. SIGN connects attestations directly to token distribution logic. instead of exporting lists and writing scripts, you define rules based on credentials and execute distributions through the protocol.
this is clearly working in production contexts. teams are using it to manage airdrops, contributor rewards, access gating. it reduces manual coordination and makes the process more reproducible. but it also raises a structural question: is SIGN just orchestrating distributions, or is it trying to become the canonical execution layer for them?
right now it feels like orchestration. it sits on top of token contracts rather than replacing them. maybe that’s intentional — staying modular instead of owning the full stack.
the more ambitious parts — persistent identity graphs, cross-chain credential portability, deeper wallet-level integrations — are still forming. they depend heavily on adoption patterns. credentials only become meaningful across systems if other systems agree to honor them, and that’s not something a protocol can enforce.
one thing that keeps bothering me is credential quality. if issuance is cheap and permissionless, then the system needs some way to differentiate high-signal attestations from noise. SIGN doesn’t really solve that directly. it gives you the rails, but not the reputation layer.
so you end up pushing that responsibility to applications or to some future meta-layer. which might work, but also fragments trust again.
also not sure how this behaves under adversarial pressure. sybil patterns, coordinated issuers, schema manipulation — all manageable individually, but together they create edge cases that aren’t obvious from the clean abstraction.
watching:
* whether schemas converge into shared standards or stay project-specific
* how offchain resolvers are implemented and whether they normalize over time
* if distribution remains the main entry point vs credentials becoming reusable assets
* emergence of issuer reputation or weighting systems
* actual cross-ecosystem reuse of credentials, not just within single platforms.
$SIGN @SignOfficial #signdigitalsovereigninfra