i've been thinking that i was wrong about so many things like RIVER and PIPPIN charts and trust infrastructure wrong for most of this year and honestly it took one specific mechanic to show me where my mental model broke 😂
i kept thinking about verifiable credentials the way most people do - as a replacement for paper documents. cleaner, harder to forge, portable across borders. and that framing is correct as far as it goes. but i spent the past two days deep in the revocation layer of the SIGN identity stack and something about it keeps pulling me back. because revocation is where the design gets genuinely hard. and where it gets hard is not where i expected.
What they built here:
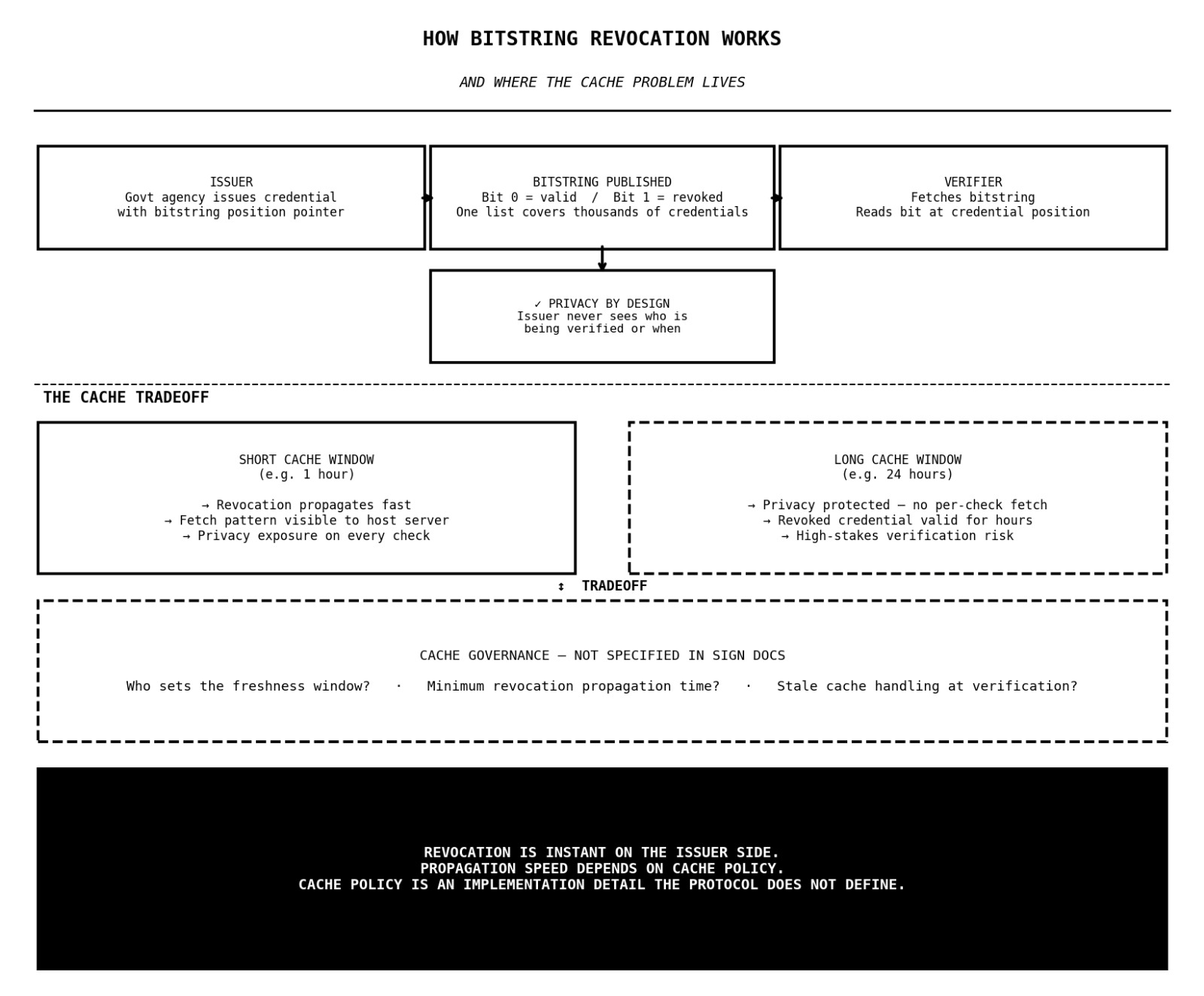
the SIGN identity framework implements credential revocation through the W3C Bitstring Status List standard. here is what that actually means mechanically.
when a government agency issues a credential, a professional license, a land title attestation, an eligibility proof, that credential contains a pointer. a reference to a specific position in a published bitstring. the bitstring is a long sequence of bits, each mapped to a specific issued credential. when the credential is valid, its bit is set to zero. when the issuer revokes it, expired license, fraudulent document, changed eligibility, the bit flips to one.
verifiers check credential validity by fetching the bitstring and reading the bit at the position the credential points to. if the bit is zero, the credential is valid. if its one, its revoked. no need to contact the issuing authority directly. no API call back to the government database. the check is self-contained and the issuer stays out of the verification loop entirely.
that is a genuinely elegant design. the issuer publishes one bitstring that covers thousands of credentials simultaneously. verifiers check status without revealing to the issuer that a specific credential is being verified. the holder presents their credential without the issuer knowing where or when it is being used. privacy is preserved at the issuer-verifier junction by design.
Where i got stuck:
the problem isnt with the bitstring itself. the problem is with who hosts it and what fetching it reveals.
when a verifier fetches the bitstring to check a credential status, that fetch request goes somewhere. it hits a server. and that server, whoever hosts the published bitstring, can see the request. it can see the IP address of the verifier, the timestamp, and by correlating with the credential pointer, potentially infer which credential is being checked and in what context.
the W3C specification acknowledges this. it notes that the hosting server learns something from fetch patterns even if the bitstring itself is privacy-preserving. the mitigation recommended is caching. verifiers download and cache the full bitstring rather than fetching it per-verification, so individual checks become invisible to the host.
the SIGN docs implement the W3C standard but dont specify caching requirements, cache freshness windows, or what happens when a credential is revoked but a verifier is operating from a stale cached bitstring.
My concern with this:
that last part is the one i cant resolve. cache freshness is a direct tradeoff between privacy and revocation speed. a verifier caching the bitstring for 24 hours protects privacy. their fetch pattern reveals nothing about individual verifications during that window. but it also means a credential revoked at 9am is still showing as valid to any verifier operating on a cache from the night before.
for a professional license this is probably acceptable. for a credential used to authorize a high-value transaction or a border crossing, a 24-hour revocation lag is a real operational gap. and for the infrastructure to work correctly, every verifier in every agency across a sovereign deployment needs to be operating on a cache policy that the protocol itself doesnt define.
the design is right
the standard is correct
what isnt specified is the cache governance. who sets the freshness window, what the minimum acceptable revocation propagation time is, and what happens at the verification layer when a revoked credential hasnt yet surfaced in a stale cache.
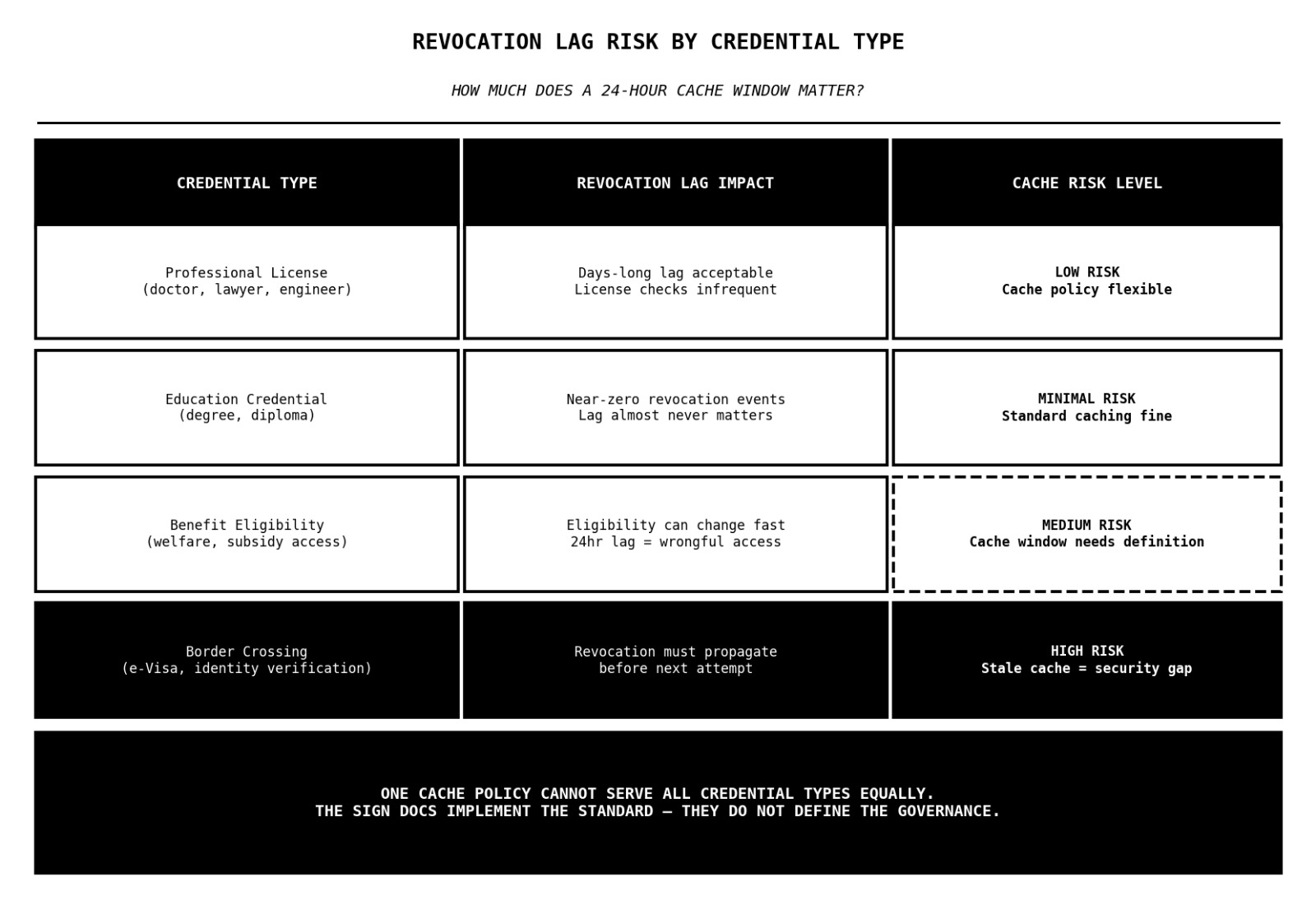
honestly dont know if the bitstring revocation model is clean enough that cache governance is just an implementation detail each deployment figures out or if the gap between revocation and propagation is the kind of thing that surfaces badly in a live sovereign system when it matters most?? 🤔
#SignDigitalSovereignInfra @SignOfficial $SIGN
