 Web3 has spent years talking about interoperability as if the hard part were simply moving assets from one chain to another.
Web3 has spent years talking about interoperability as if the hard part were simply moving assets from one chain to another.
It is not.
The real problem is what happens to privacy the moment that movement begins.
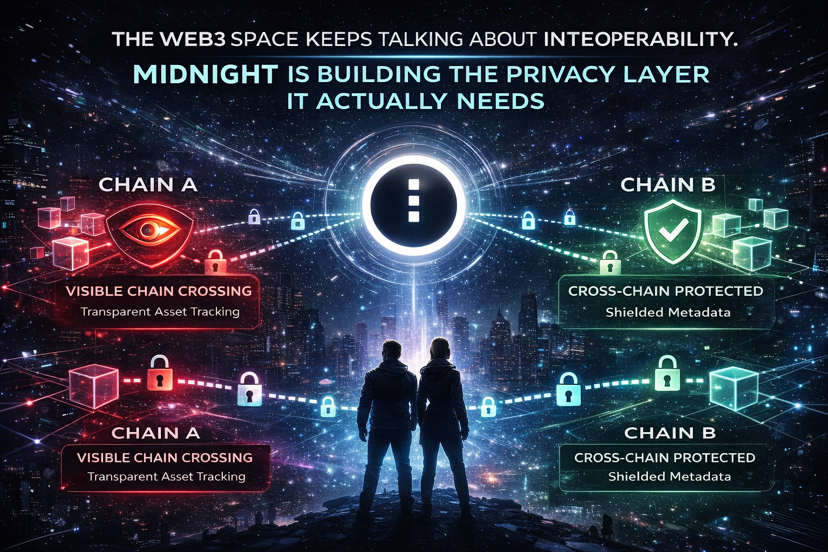
Every bridge creates a trail. One chain shows assets leaving. Another chain shows them arriving. Even when the underlying networks support privacy, the bridge itself often becomes the weak point that exposes user behavior, timing, and flow patterns.
For ordinary users, that is inconvenient.
For institutions, it is much more serious.
A cross-chain transfer is not just a transfer when confidential capital is involved. It becomes an observable event. And in finance, observability is often just another word for exposure.
That is the gap @MidnightNetwork appears to be targeting.
Privacy Can’t Sit Outside Interoperability
What makes Midnight interesting is that it does not treat privacy as something added after the fact.
Instead, privacy sits inside the interoperability model itself.
The architecture introduces a mechanism where activity on one chain can trigger action on another without forcing the user to expose the full trail in the middle. That distinction sounds subtle, but it changes the design completely.
In practical terms, a user might want to access Midnight’s private execution environment while paying from Ethereum. The user locks value on Ethereum, the protocol recognizes the action, and Midnight’s capacity is made available through its cross-chain logic. The user experiences a simple outcome: pay on one chain, operate privately on another.
What matters is what does not happen.
The proof layer does not need to sit in the user’s face.
The privacy logic stays underneath the interaction, where it belongs.
That is a very different model from the usual bridge design.
The Treasury Story Is More Interesting Than It Looks
There is another part of the structure that deserves more attention: the way Midnight thinks about fees and Treasury inflows.
Most ecosystems rely heavily on their own native token for long-term sustainability. Midnight appears to be building something broader.
Its Treasury is not limited to just NIGHT flows. As cross-chain activity grows, it can receive value from other assets as well. That means the ecosystem fund is not trapped inside a single-token economy. It can accumulate support from outside the network when users interact through different chains.
That matters.
A Treasury backed by multiple assets is a stronger base than one dependent on a single token narrative. It makes the system less fragile and more realistic for long-term operations.
In a market where many projects are still trying to bootstrap liquidity, that is not a small detail.
Why the Cardano Link Matters
Midnight’s design also sits on top of a security foundation that is easy to overlook.
Because of the Cardano Partner Chain framework, the network inherits an established production environment rather than trying to build cross-chain security from scratch. That lowers the risk profile in a space where bridges are often the weakest part of the stack.
This is important because bridge risk is not theoretical anymore. It has been one of the most expensive failure points in crypto.
Midnight’s approach looks more cautious than flashy. And in cross-chain infrastructure, cautious is usually better.
The Ambitious Part Is Still Ahead
The part that really stands out is the longer-term plan: a ZK trustless bridge.
That is the serious piece.
Most bridges depend on a set of validators or signers that attest to what happened on another chain. Midnight’s planned model aims to replace that trust assumption with cryptographic proof. In that setup, the security does not depend on whether a validator set behaves honestly. It depends on the proof itself.
That is a much stronger design.
It is also much harder to execute.
But if it works, it would be a meaningful step forward for cross-chain security.
Midnight Is Not Trying to Be the Center
This is what I find most structurally interesting.
Midnight does not seem to be positioning itself as the main hub of everything.
A lot of interoperability projects want to become the center of the network graph. They want every chain flowing through them. Midnight feels different. It looks more like a privacy layer that other chains can route through when users need confidential cross-chain activity.
That is a more complementary role, and probably a more realistic one.
The Babel Station concept shows that clearly. Users can interact with Midnight’s privacy infrastructure using assets that are not NIGHT, which means they can access the system without needing to adopt the token mechanics first.
That lowers the barrier to use.
And lower friction is usually what decides whether infrastructure gets used at all.
The Open Question
The timing may actually be favorable.
Cross-chain activity is still growing. Institutional participation is still rising. Regulatory attention is increasing. All of that makes privacy more, not less, relevant in interoperability.
The question is not whether the need exists.
The question is how fast Midnight can prove that its model works in production before the rest of the market starts chasing the same gap.
That window is open now.
It may not stay open for long.
