I keep coming back to the idea that data minimization is not actually that complicated. To me it simply means using the data you truly need and leaving the rest alone. Regulators describe it in much the same way when they say personal data should be relevant and limited to what is necessary for a specific purpose. What makes Midnight interesting is that it tries to turn that legal and ethical principle into network design. Its own material presents it as a privacy first blockchain built around zero knowledge proofs and selective disclosure with a structure that puts only essential data on chain while sensitive data stays in local storage.
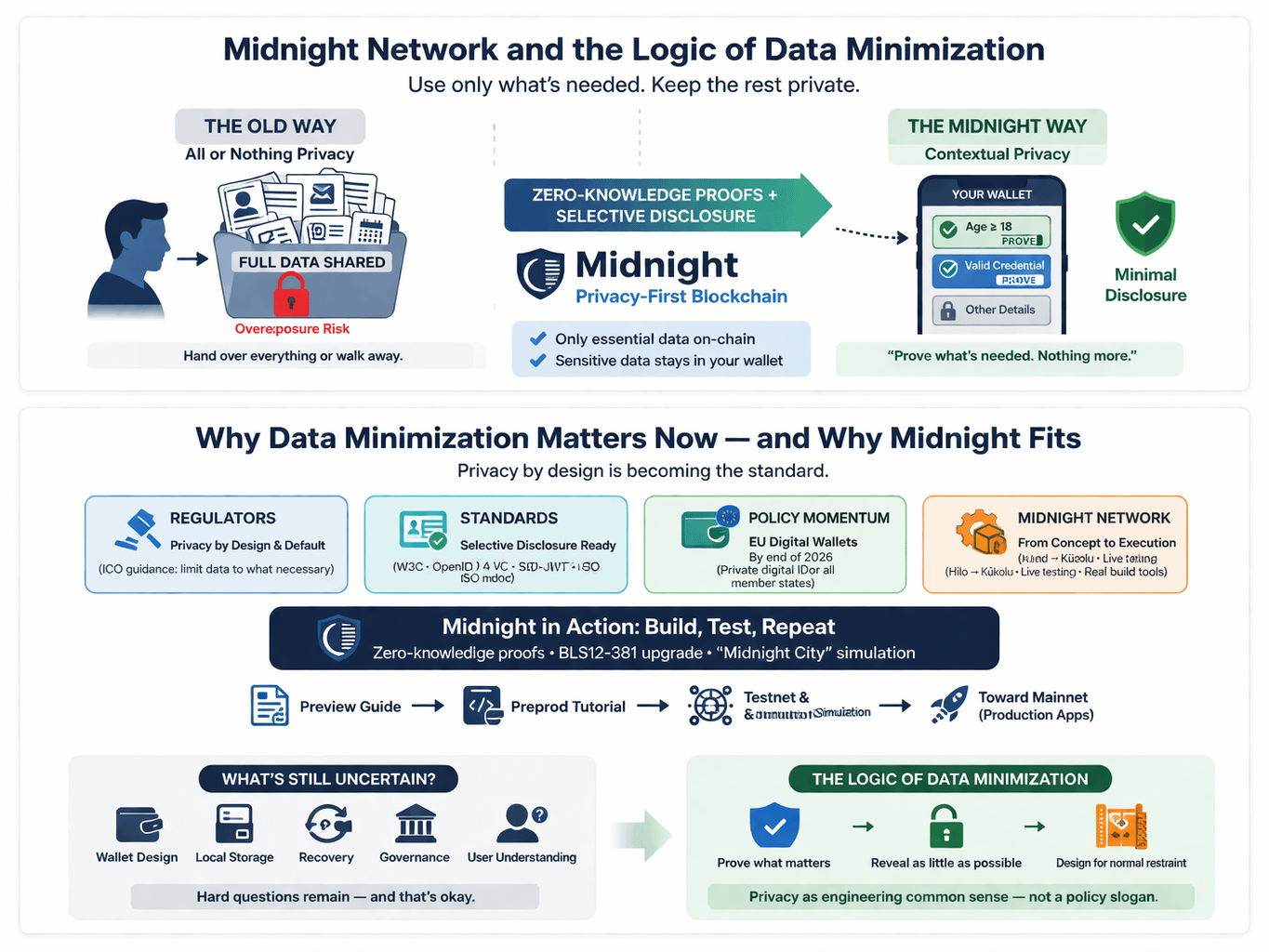
I used to think privacy in systems like this meant hiding everything as if the only real choice was total secrecy or total exposure. The more I look at Midnight the more that feels like the wrong way to understand it because its approach to selective disclosure treats privacy as something shaped by context rather than as an all or nothing condition. The idea is to reveal what is necessary for a specific interaction and nothing more. That fits with the way broader identity standards are developing. The W3C’s Verifiable Credentials Data Model 2.0 makes room for selective disclosure so that only part of a credential needs to be shared and it also allows for zero knowledge presentations. What matters here is not the fantasy that nothing is ever disclosed. What matters is that proof and exposure no longer have to be the same thing. A person might prove they are above a required age or that they hold a valid credential without handing over the full document and every detail attached to it.
That also helps explain why this discussion feels more timely now than it did five years ago. Data minimization is no longer treated as a nice extra that can be added later. More often it is being framed as something that should be built in from the start. The ICO’s current guidance on data protection by design and by default reflects that shift by stressing that privacy needs to be part of the design phase and the full life cycle of a system with personal information limited to what is actually needed for each purpose. At the same time the standards around digital credentials and selective disclosure have become more mature and more usable. OpenID for Verifiable Credential Issuance 1.0 was published in September 2025 with support for formats such as SD JWT VC ISO mdoc and the W3C credential model. On the policy side the European digital identity wallet effort has also moved closer to real implementation. The European Commission describes these wallets as a private means of digital identification and the EDPS has noted that member states are expected to offer them by the end of 2026. Taken together these changes make Midnight’s core idea feel less experimental and more practical.
What also stands out to me is that Midnight itself seems closer to the build and test phase than the imagine it phase. In January 2026 the project said it had entered its Hilo phase and was aiming next for a federated mainnet phase called Kūkolu with attention on first production applications. The documentation now includes a Preview network migration guide and a Preprod deployment tutorial which feels very different from a project that is still speaking only in broad concepts. There have also been quieter technical changes that seem important. Midnight says it completed a move to BLS12 381 for its proving system in 2025 partly to improve efficiency and security and it has also shown Midnight City which is a simulation meant to show how selective disclosure and programmable privacy behave under more lifelike network activity. I do not take any of that as proof that every hard problem has been solved. I take it as a sign that the discussion has moved from theory toward operations.
There is still plenty that remains uncertain and I think it is better to say that plainly. Keeping sensitive data off chain does not make the difficult questions disappear. It shifts them toward wallet design local storage recovery governance and the everyday reality of whether people actually understand what they are sharing and why. What surprises me is that this does not make the idea weaker. It makes it more honest because it treats privacy as something that must be worked through in practice rather than promised in the abstract. I find it helpful to look at Midnight less as a claim of perfect privacy and more as a serious attempt to apply a simple rule in a difficult environment. Prove what matters. Reveal as little as possible. Design the system so restraint feels normal rather than exceptional. If that approach holds then data minimization stops sounding like a slogan in a policy document and starts to look more like engineering common sense.
@MidnightNetwork #Night #night $NIGHT

