I have noticed something about how people think about data.
For a long time, the conversation has been about ownership.
Who owns the data.
Who stores it.
Who has access to it.
That framework made sense when systems were centralized. Data lived inside platforms, companies controlled it, and users interacted with it through those systems.
Blockchain changed that conversation.
It introduced the idea that data could be shared across a network instead of controlled by a single entity. Ownership became more distributed. Verification became more transparent.
But in solving one problem, it created another.
Sharing data widely does not mean controlling how that data is used.
When everything is visible, ownership becomes less important than exposure.
Midnight Network approaches this problem from a different angle.
Instead of focusing only on who owns the data, it focuses on who controls how that data is revealed.
This is a subtle shift, but it changes the structure of how systems can operate.
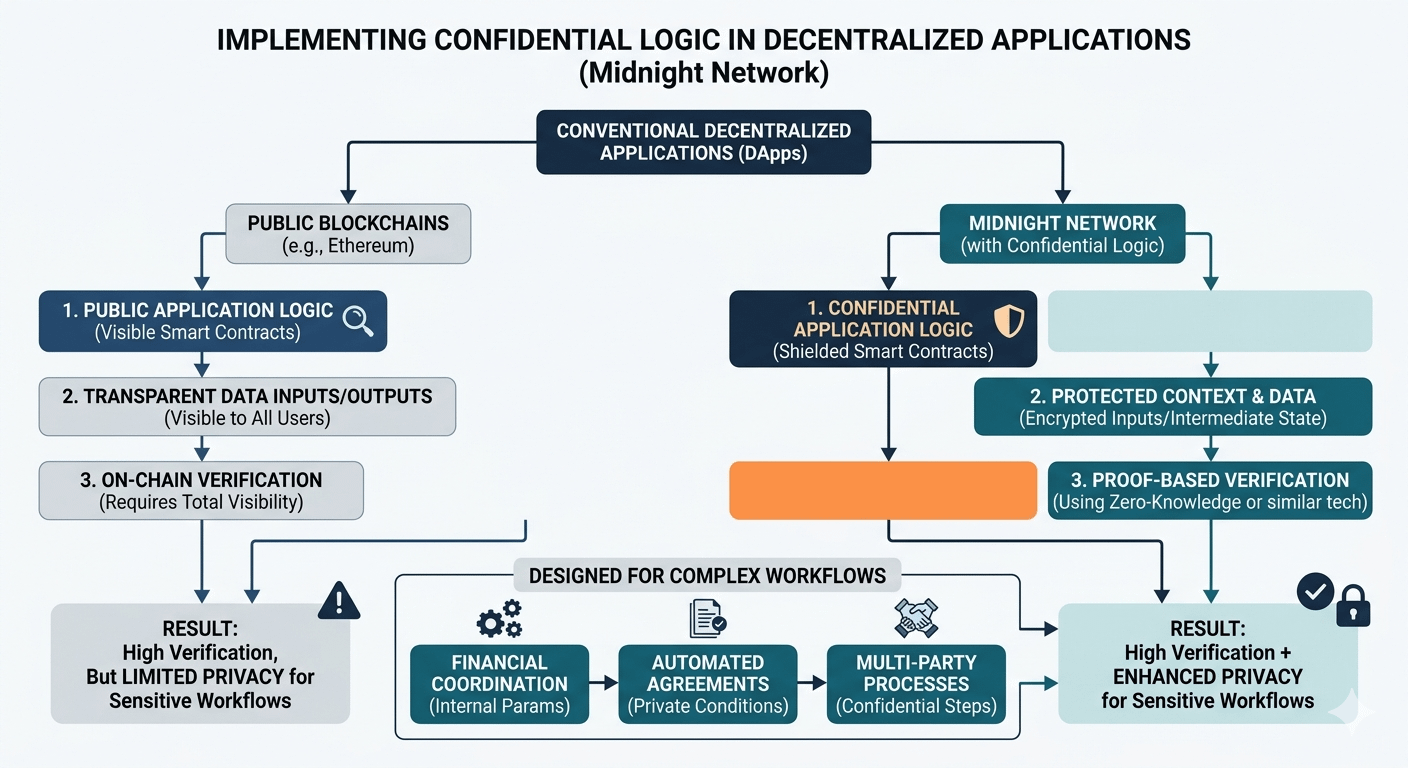
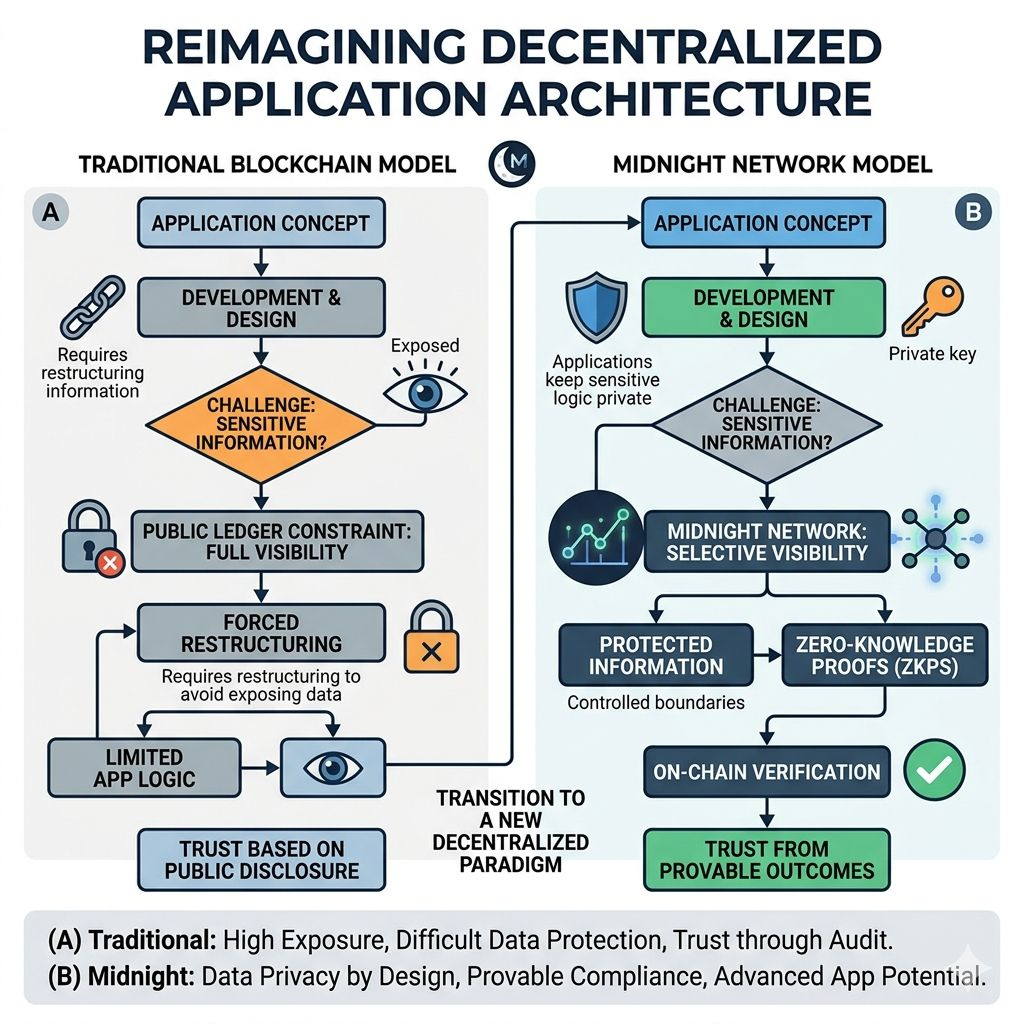
In most blockchain environments, participation requires disclosure. Transactions are visible. Activity is recorded publicly. Verification depends on the ability to inspect what happened.
Midnight separates these concepts.
Using zero-knowledge systems, it allows participants to prove that something is valid without revealing the underlying data. The system confirms outcomes while keeping the details protected.
This introduces the idea of control instead of exposure.
Participants can decide what information becomes visible and what remains private. They can interact with the system without giving up access to all their data.
This distinction becomes more important as blockchain systems expand into environments where data sensitivity is not optional.
A business may need to prove that it followed certain rules without exposing internal operations.
A user may need to confirm identity without revealing personal details.
A process may require validation without making every step public.
In these situations, ownership alone is not enough.
Control over disclosure becomes the critical factor.
Midnight’s model allows systems to operate within those constraints.
Instead of forcing data into a fully public environment, it enables selective visibility. The system verifies what needs to be verified while leaving the rest of the information protected.
This creates a different kind of flexibility.
Applications that were difficult to build on transparent systems become more practical. Interactions that required trust in centralized entities can be replaced with cryptographic verification.
But like all infrastructure ideas, the concept only becomes meaningful when it is used.
Most existing blockchain applications are built around transparency because it is the established model. Users and developers understand how it works. The trade-offs are already accepted.
Shifting toward systems that prioritize control over disclosure requires a change in how applications are designed.
Developers need to think about what information is necessary to reveal. Users need to trust outcomes that are proven rather than observed.
This transition does not happen immediately.
It develops as more systems encounter situations where full transparency becomes a limitation rather than an advantage.
Midnight is positioned around that transition.
It assumes that future applications will require more control over how data is shared. Not everything will be public, and not everything will be hidden. Systems will need to operate within a balance between visibility and privacy.
If that assumption proves correct, networks that enable controlled disclosure may become an important part of how blockchain technology evolves.
If the demand develops more slowly, adoption may take time.
This uncertainty is common for infrastructure projects.
They are built for shifts that are beginning to appear but have not yet become universal.
Midnight is exploring what happens when data is not just owned, but controlled.
Whether that idea becomes standard will depend on how systems evolve and what constraints they begin to face.
For now, it introduces a different way to think about information.
Not as something that must be shared.
But as something that can be revealed with precision.