@SignOfficial #SignDigitalSovereignInfra $SIGN
I was literally staring at the approval email in one tab, while the next screen made me question my own sanity.
The business had already cleared the review process. There was no ambiguity—the status was green, the timestamp was right there, and the phrasing was definitive enough that no one should have needed a second opinion. Yet, there I was on the next portal, being asked to upload the exact same proof of ownership all over again. I gave it 14 minutes, refreshed the page twice, logged out, logged back in, and still hit the same upload prompt.
That was the moment I stopped treating it like a temporary glitch. A much bigger, more frustrating question started bothering me: When one institution accepts a fact about a business, can the next step in the chain actually inherit that trust? Or does every new portal quietly reset your progress back to zero?
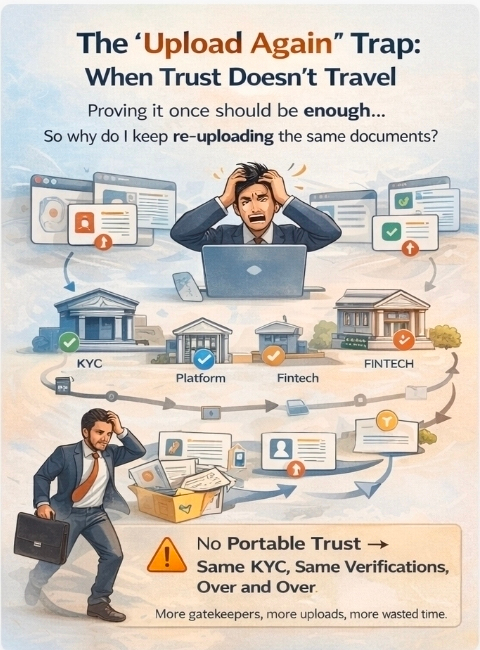
This is a part of the Middle East’s massive growth narrative that rarely gets discussed honestly. People love the big-picture buzzwords—state-led digital infrastructure, massive capital deployment, ambitious policy, new rails. That’s all great. But businesses don't glide through an economy on a single, magical wave of approval. They have to slog through separate gates, guarded by different systems, different teams, and totally different risk appetites.
A free zone verifies your status. A bank demands the exact same paper trail. An SME support initiative wants it, but in a totally different format. A cross-border partner runs another check simply because their software can’t digest what the last system already cleared. The underlying fact hasn't changed. The workload somehow has.
Where Sign Actually Matters
This exact friction is why Sign caught my attention.
I don't care about "credential verification" because it looks good on a pitch deck. Tacking an attestation layer onto a broken workflow doesn't magically fix the design. Sign only matters to me if a cleared fact can actually be reused in the next workflow without turning into a blind, reckless shortcut. I don't care if a digital credential exists in the ether; I care if the receiving party can act on it without dragging the business back through the same bureaucratic loop it just escaped.
I’ve spent enough time in operations to know what happens when the handoff between systems is weak. System A says "approved." System B still sees a pending status, so someone manually re-uploads the packet just to force the process forward. Next thing you know, developers are adding "wait guards" because the approval data arrives slower than the action it triggers. Watcher jobs are spun up because trust in the system's timing is gone. Support tickets start piling up with vague "please wait a bit longer" responses. Eventually, the manual fallback rules kick in. Reconciliation becomes a dreaded weekly ritual.
And that’s usually when the spreadsheets appear.
The Hidden Cost of "Efficiency"
Here is the hard truth: a portable approval is not the same thing as a visible approval. Repeated reviews are just the loudest way a system wastes time. The quieter, deadlier cost hides in the operations layer. From a distance, the tech stack looks efficient because the primary decision only happened once. But the true cost bleeds out through retries, queue delays, manual exceptions, and the quiet workarounds that operators invent but never document. The review might be done, but the waiting isn't. The business bleeds time; the team bleeds labor. The system still pays the price, it just hides the receipt in "operations."
This is why I’m not sold on Sign unless it attacks this transfer problem at the root. It shouldn't just let Institution A declare a fact is true. It needs to give Institution B the exact context: Who verified this? When? Under what scope? Which policy version? Has it been revoked since yesterday? That might sound overly fussy until you are the person deciding whether yesterday’s approval is safe to unlock today’s money. Without that deep structure, reuse just devolves back into human guesswork. And the moment humans have to start guessing, the process gets expensive again.

Context is Everything
This is where Sign has to graduate from generic infrastructure into something highly specific. Storing a credential is easy. The hard part is carrying enough context alongside that credential so the next system can inherit the trust without overstepping.
A narrow approval for a grant program shouldn't accidentally trigger broad permissions for a massive financial payout. A revocation that takes too long to update can leave downstream systems acting on stale confidence—a nightmare scenario. These aren't edge cases; managing this is the job.
In the Middle East, this is critical. So much of the region's economic momentum relies on businesses moving seamlessly across public programs, financial rails, and partner networks. If every checkpoint acts like an isolated island, we haven't built digital infrastructure—we’ve just built prettier, disconnected forms. Sign only becomes true infrastructure if it actually kills the duplicate proof-work across these institutional borders.
The Real Test
I also don't believe unlimited, frictionless portability is the answer. That creates a different kind of chaos. If approvals travel too loosely, weak trust spreads like a virus. A revoked condition might survive in a downstream cache longer than anyone anticipated. I would much rather see Sign be strict and readable than smooth and vague. Saving work is great; blurring accountability is a disaster.
This is why @SignOfficial has to be more than just branding for me. I don't need a network that carries trust cheaply—I need it to carry trust with intense discipline. And I have zero interest in the $SIGN token unless it is paying for real operational heavy lifting: sustaining verifier incentives, enforcing revocation discipline, handling disputes, and routing credentials reliably when the network is under stress. Otherwise, it’s just crypto-decoration on a web2 workflow problem.
My test for Sign is incredibly straightforward. When the system is bogged down and stressed, do previously accepted facts keep flowing into the next action with clear scope, freshness, and status? Or do human teams have to step in and rebuild that trust by hand?
I’ll be watching for the telltale signs of failure: duplicate document uploads, swelling reconciliation queues, rogue watcher jobs, and support tickets that scream "approved here, but blocked there."
If those metrics stay boring and quiet under load, then Sign is actually fixing the invisible friction that slows down real economic growth. The victory isn't in getting the first approval. The victory is the second system knowing exactly what to do with it.