@MidnightNetwork When people talk about smart contracts, they usually focus on automation. Code runs, conditions are met, and everything executes without trust.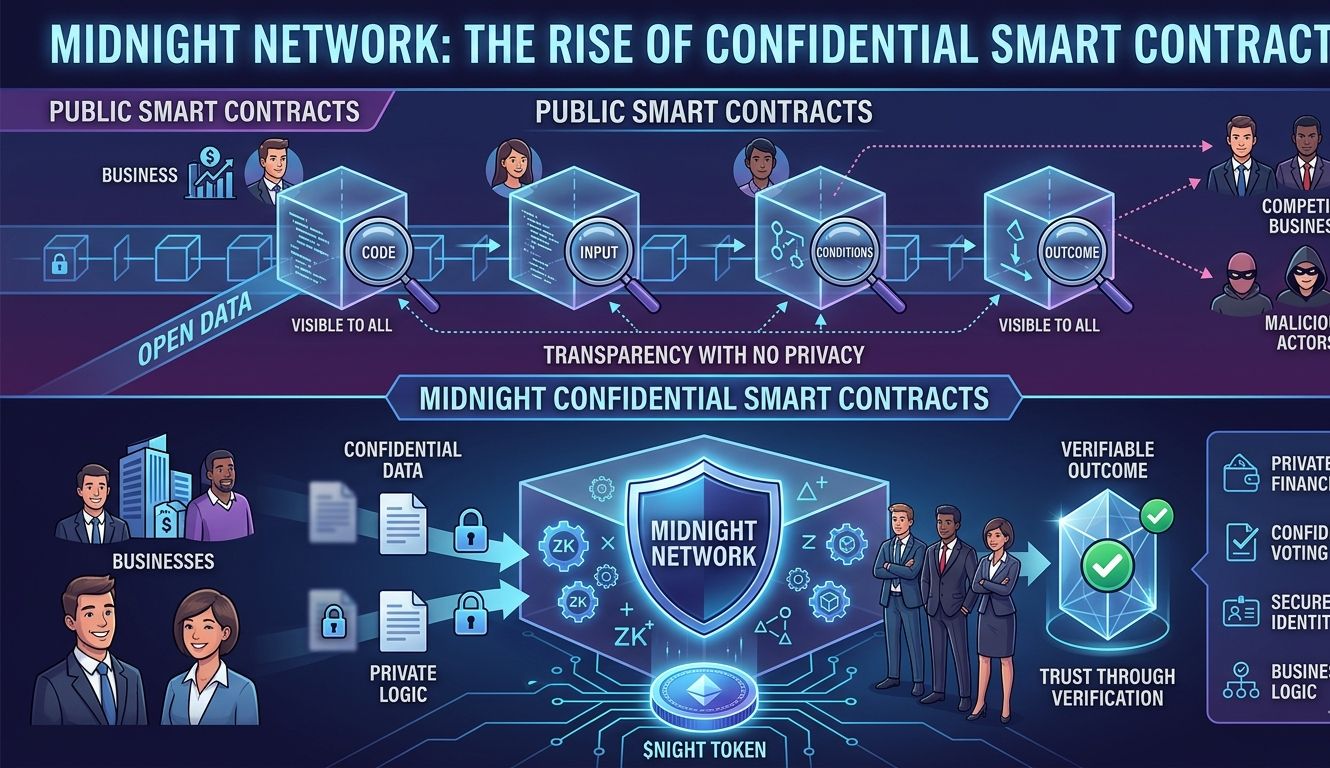
But there’s one thing most people ignore.
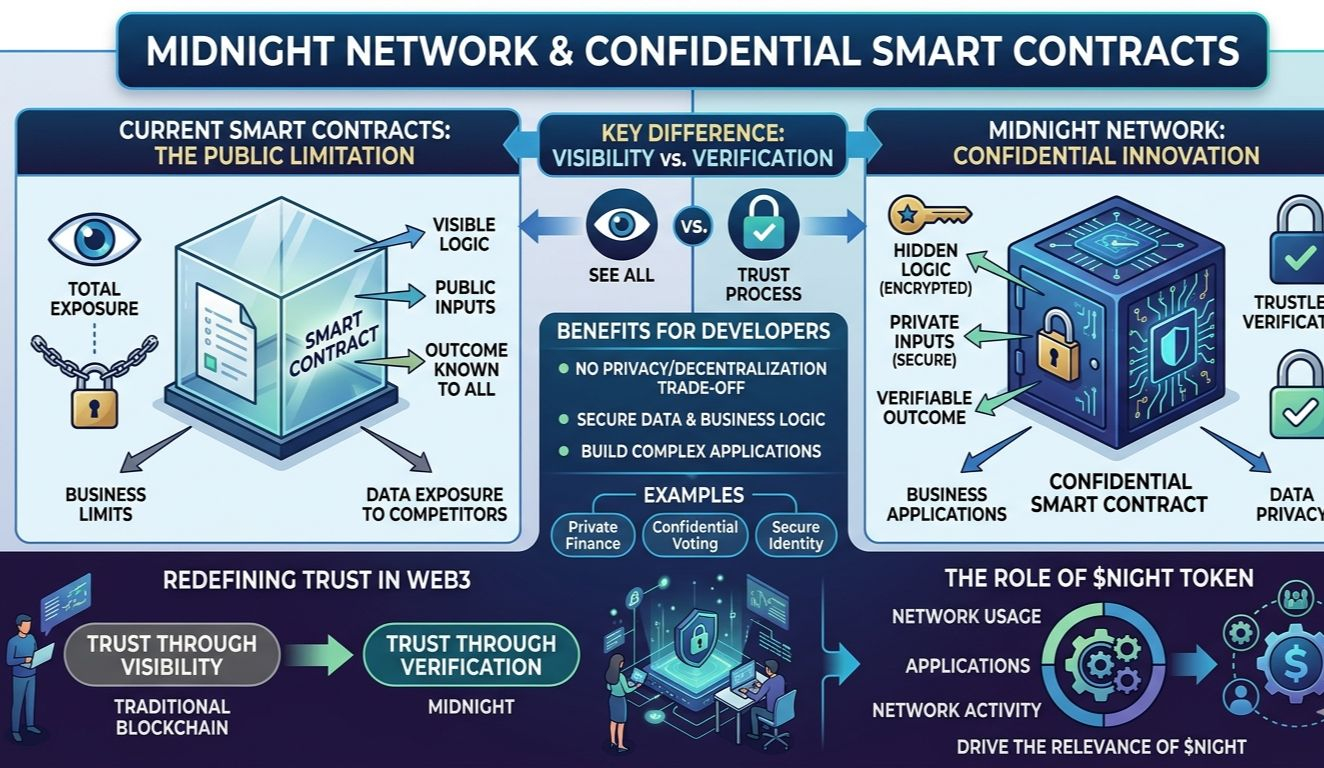
Smart contracts today are completely public.
Every condition, every input, every outcome — visible to anyone.
And while that works for simple use cases, it becomes a serious limitation when things get more complex.
This is where Midnight Network introduces a powerful shift: confidential smart contracts.
Why Public Smart Contracts Aren’t Always Enough
Let’s say a business wants to use blockchain for operations.
If everything is public, competitors can see strategies, pricing models, or internal logic. That’s not practical. The same goes for individuals dealing with sensitive financial or personal data.
Transparency is good — but full exposure isn’t always.
Right now, developers are forced to choose between:
Transparency with no privacy
Privacy with no decentralization
Midnight is trying to remove that trade-off.
What Makes Midnight Different
Midnight Network allows smart contracts to operate in a way where sensitive data stays private, but the outcome is still verifiable.
This means:
The logic can run securely
The result can be trusted
The data behind it doesn’t need to be revealed
It’s like proving that a decision is correct without showing how you reached it.
That’s a completely different model compared to traditional blockchain systems.
A New Type of Application Layer
This opens the door to applications that were difficult to build before.
Think about:
Private financial agreements
Confidential voting systems
Secure identity-based services
Business logic that doesn’t expose internal data
These are real-world needs, not just experimental ideas.
Midnight is positioning itself as a network where these types of applications can exist naturally.
Why This Could Change Developer Behavior
Developers usually avoid building complex systems on public blockchains because of data exposure.
With confidential smart contracts, that barrier starts to disappear.
Builders can create applications that feel closer to traditional systems — but with the added benefits of decentralization.
This could attract a different type of developer.
Not just crypto-native builders, but also those who were previously hesitant to move on-chain.
Trust Without Transparency Overload
One of the most interesting parts of this model is how it redefines trust.
In traditional blockchain systems, trust comes from visibility. You see everything, so you trust the outcome.
In Midnight’s approach, trust comes from verification instead.
You don’t need to see the data. You just need to know that it has been processed correctly.
That’s a subtle shift, but it has big implications.
The Role of $NIGHT
The $NIGHT token connects to this ecosystem as part of how the network functions.
As more confidential applications are built and used, the network becomes more active. And as activity increases, the token naturally becomes more relevant.
It’s not just about trading — it’s about usage.
And that’s an important distinction.
Challenges That Come With It
Of course, this approach isn’t easy.
Building confidential systems is more complex than building fully public ones. Developers need better tools, better documentation, and a smoother experience.
There’s also the challenge of awareness.
Many users still don’t fully understand why privacy matters in these scenarios. That understanding will grow over time, but it won’t happen instantly.
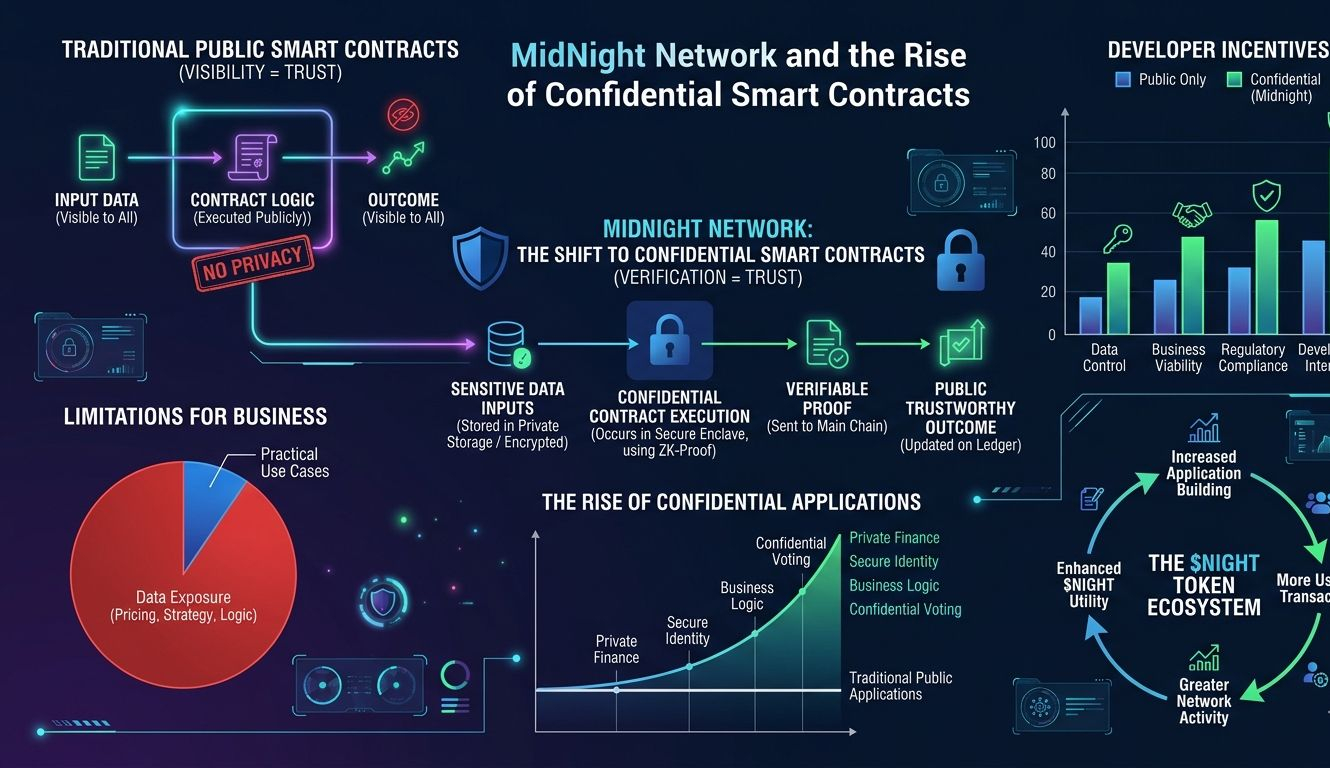
Midnight Network isn’t trying to improve what already exists — it’s trying to expand what’s possible.
Confidential smart contracts are not just an upgrade. They’re a new way of thinking about how blockchain applications should work.
Instead of forcing everything into a public model, they introduce flexibility.
And that flexibility could be the key to bringing more real-world use cases into Web3.
For now, it’s still early.
But if this model gains traction, Midnight could become the place where the next generation of applications is built — not just visible ones, but confidential ones that still earn trust. #night $NIGHT
