When I first realized I wasn’t dismissing Midnight in the first ten seconds, I paused. The feeling itself was strange. This market has trained you to filter quickly, too many generic privacy solutions, too many exaggerated promises that crumble the moment you delve into the details. Midnight didn't trigger that instinct. At least not immediately.
What truly attracted me wasn't the concept of privacy itself. I'd heard that countless times. It was self-discipline. Midnight didn't try to sell privacy as a belief system. It saw it as a constraint, a constraint that must coexist with ease of use, verifiability, and a pragmatic system that doesn't tolerate black boxes. This shift is far more significant than it sounds.
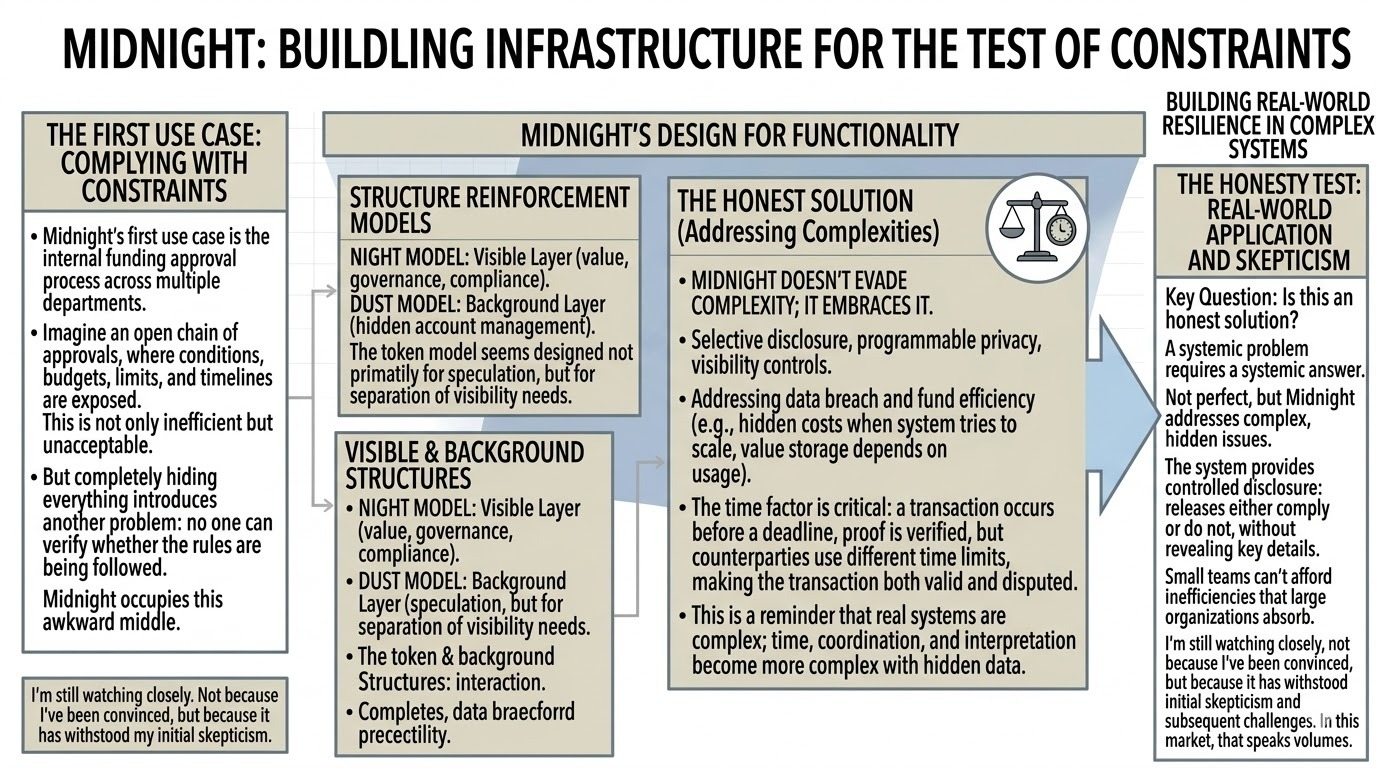
The first use case that truly made me appreciate this was the approval process in a private company.
Imagine a company that needs to manage internal funding approvals across multiple departments. On an open chain of approvals, all conditions, budgets, limits, and timelines, are exposed. This is not only inefficient but unacceptable. But completely hiding everything introduces another problem: no one can verify whether the rules are being followed.
Midnight occupies this awkward middle.
The approval process operates cautiously. Sensitive information, such as budget size or internal assessments, remains hidden. But the results are verifiable. Releases either comply or do not, and this can be verified without revealing key details. This is not secrecy, but controlled disclosure.
From here, the design begins to show functionality.
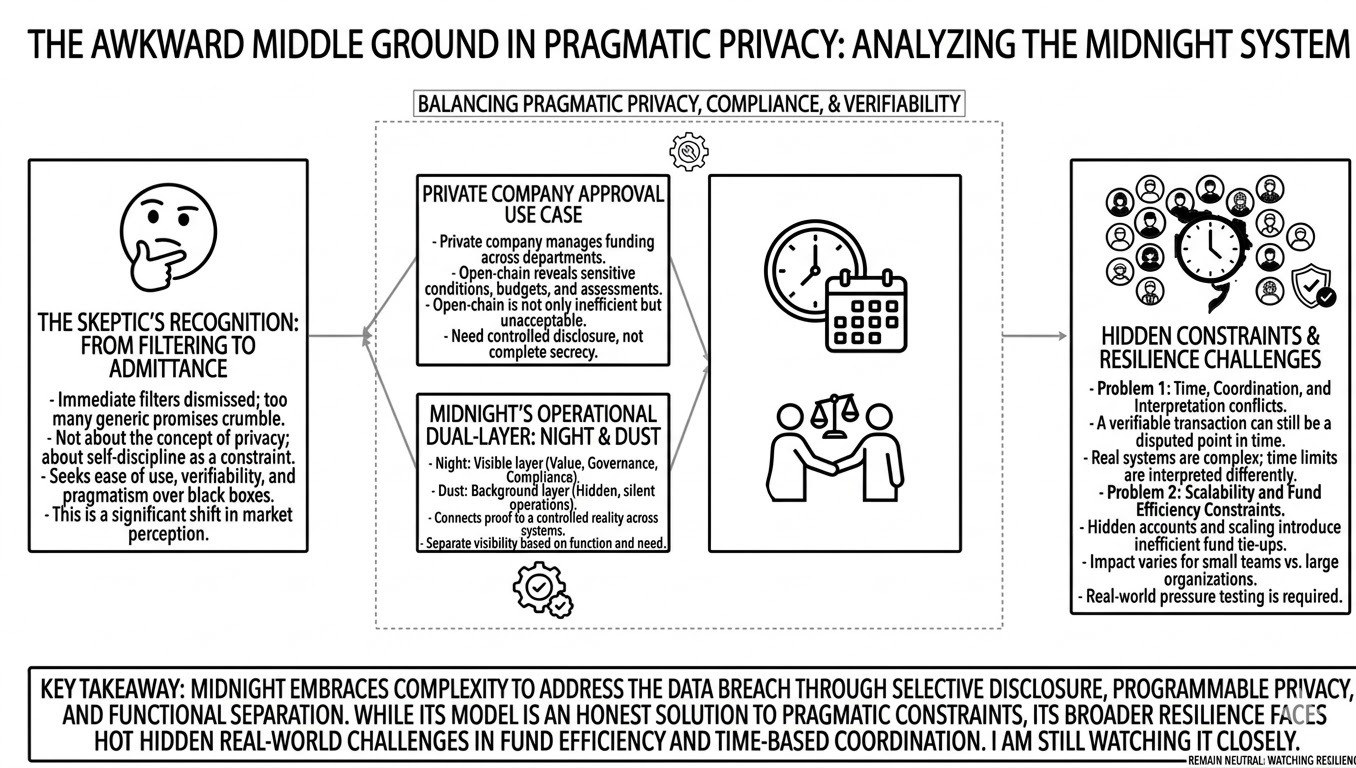
The Night and Dust models reinforce this structure. Night represents the visible layer, value, governance, and compliance. Dust runs in the background, managing hidden accounts. This model separates the parts that need to be visible from the parts that need to operate silently. The token model seems, for the first time, no longer primarily designed for speculation.
On a larger scale, large organizations can afford it. Freezing funds to maintain operations is simply an additional budget item. But for small teams, the situation is entirely different. It's no longer just about building; it's about funding the ability to keep the system running.
This becomes a different kind of constraint.
In trying to address the data breach, the Midnight system raised the issue of fund efficiency. This isn't an obvious problem like gas costs; it's a hidden one. This kind of problem arises when the system tries to scale and suddenly realizes that usage depends on how much value it can store.
Then there's the time factor.
One scenario worries me: a particular transaction occurs before the deadline. Proof is verified. Conditions are met. But the counterparty uses a different time, different time limits and different system limitations. Now, the transaction is both valid and disputed.
The Midnight system proves the rules are followed, but it can't determine which point in time is decisive.
This isn't about privacy violations; it's a reminder that real systems are complex. Time, coordination, and interpretation, these issues don't disappear by hiding data; in some ways, they become even more complex.
And that's what I gradually realized.
Midnight may not be perfect, but it's an honest solution. It doesn't try to evade complexity; it embraces it. Selective disclosure, programmable privacy, and visibility controls, these are not easy problems to solve, nor can they be resolved through simple compromises.
I'm still watching it closely.
Not because I've been convinced, but because it has withstood my initial skepticism and subsequent challenges. In this market, that speaks volumes.
@MidnightNetwork #night $NIGHT
