When I first started looking at SIGN, I assumed it was just another token distribution layer dressed up with better tooling. That felt like a crowded category already. Airdrops, reward campaigns, and credential gating have been circulating for years. What changed my mind was realizing that SIGN is less about who gets tokens and more about how systems decide who should get them in the first place. The common framing treats SIGN as a distribution engine. That view is incomplete. The deeper thesis is that SIGN is attempting to standardize how credentials are verified and used across digital systems. In other words, it is not optimizing payouts. It is trying to formalize trust as a reusable infrastructure layer.
The common framing treats SIGN as a distribution engine. That view is incomplete. The deeper thesis is that SIGN is attempting to standardize how credentials are verified and used across digital systems. In other words, it is not optimizing payouts. It is trying to formalize trust as a reusable infrastructure layer.
On the surface, SIGN looks like a platform where users receive tokens based on certain conditions. Underneath, it is building a verification layer where credentials such as identity, participation, or reputation are issued, stored, and validated in a structured way. This enables developers and organizations to rely on shared proofs instead of rebuilding trust logic from scratch each time. The risk, however, is that standardizing credentials introduces dependency on the quality and integrity of those attestations.
This mechanism matters more than it initially appears. Most crypto systems struggle not with execution but with coordination. Who qualifies for access, rewards, or governance is often decided through fragmented or opaque methods. SIGN tries to reduce that friction by turning credentials into portable signals. Instead of asking “who are you” repeatedly, systems can ask “what has already been verified about you.”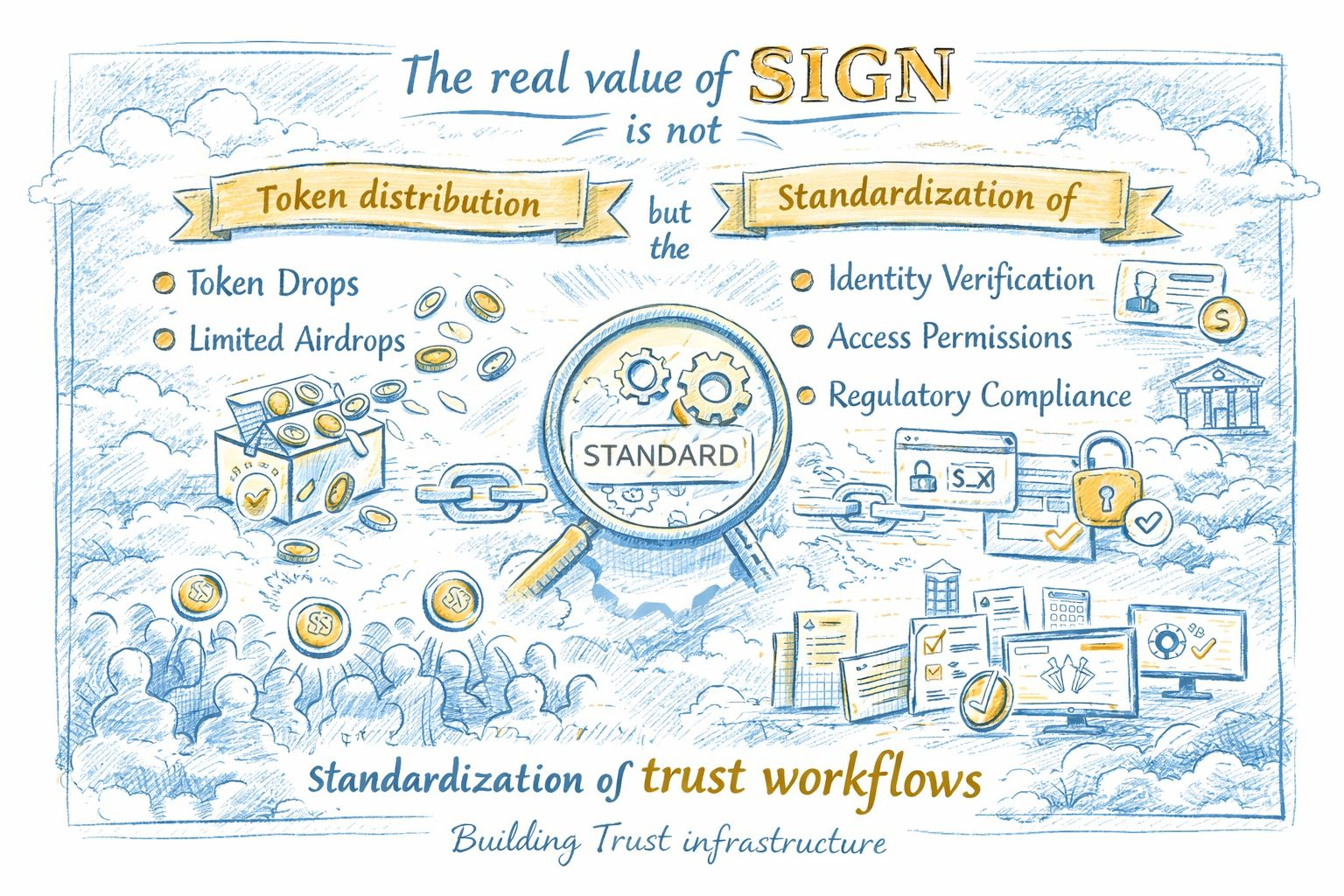 The token layer sits on top of this, but it is not the core innovation. Incentives in SIGN appear to function as a way to encourage participation in verification flows and ecosystem growth. Token distribution can suggest early engagement and awareness, but it does not confirm whether the underlying credential system is being reused in meaningful ways. If incentives drive short-term activity without long-term reliance on the verification layer, the model weakens.
The token layer sits on top of this, but it is not the core innovation. Incentives in SIGN appear to function as a way to encourage participation in verification flows and ecosystem growth. Token distribution can suggest early engagement and awareness, but it does not confirm whether the underlying credential system is being reused in meaningful ways. If incentives drive short-term activity without long-term reliance on the verification layer, the model weakens.
Where this becomes more interesting is at the ecosystem level. If multiple applications begin to rely on shared credentials, SIGN could act as connective infrastructure across otherwise isolated platforms. This shifts it from a single-use tool into something closer to administrative middleware for digital coordination. It aligns with a broader trend where crypto systems move from visibility-first design toward selective disclosure and structured trust.
Still, the gap between design and adoption remains significant. Credential systems only work if they are widely accepted and consistently used. A fragmented landscape where each project issues its own incompatible attestations would limit the value of standardization. Current activity around SIGN can suggest growing interest, but it does not necessarily confirm deep integration into real workflows.
The real test is not how many tokens are distributed, but how often credentials issued through SIGN are reused across different contexts. If developers begin treating it as a default verification layer, that would strengthen its position. If usage remains tied to isolated campaigns or short-term incentives, the system risks being reduced to another distribution tool.
There is also a subtle tradeoff here. Making credentials portable increases efficiency, but it raises questions about privacy, control, and potential over-reliance on shared standards. The balance between interoperability and independence will shape whether the model scales sustainably.
What SIGN surfaces is a broader shift. Digital systems are moving from proving ownership to proving qualification. That requires infrastructure that can carry trust across environments without constant revalidation.
If that infrastructure becomes reliable, token distribution becomes a secondary effect rather than the main event. And if it does not, no amount of incentives will compensate for the absence of credible, reusable trust.
@SignOfficial $SIGN #SignDigitalSovereignInfra