I have started paying more attention to public infrastructure design lately, not from the angle of speed, but from the angle of proof.
A system can look efficient on the surface and still become fragile when different institutions need to verify the same fact without depending on the same database, the same operator, or the same internal workflow.
That is the point where SIGN began to feel interesting to me. It reads less like a place to store claims and more like a way to make claims portable, checkable, and durable across systems that do not naturally trust one another.
The friction is easy to underestimate. Sovereign-grade systems do not fail only because data is missing. They also fail when evidence exists, but cannot travel cleanly between agencies, vendors, financial rails, or regulated service layers.
@SignOfficial #SignDigitalSovereignInfra $SIGN 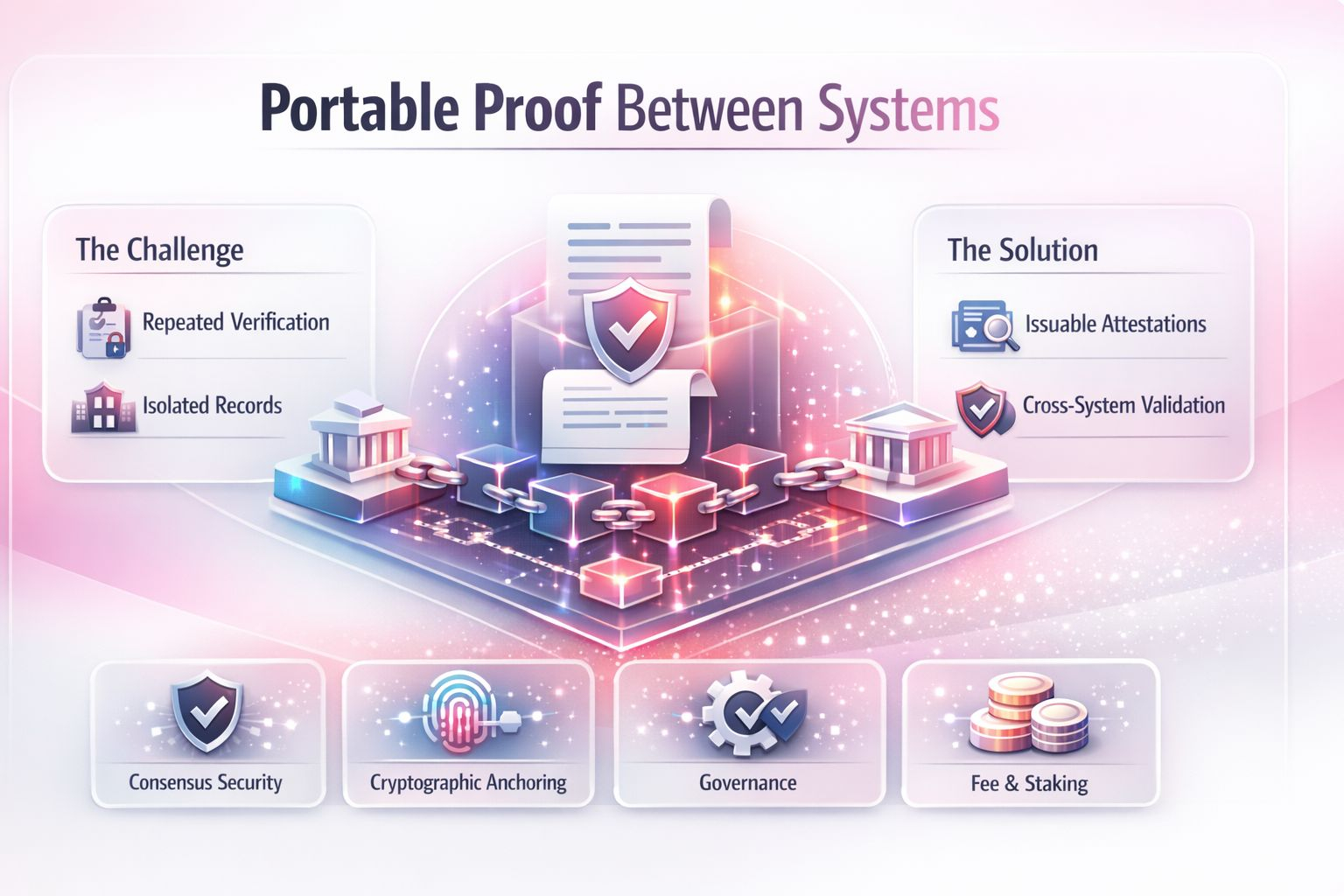
One office may confirm that a condition has been met. Another may need to rely on that outcome.
A third may need to audit the decision later. If each party has to reconstruct the full process from scratch, coordination becomes slow, expensive, and inconsistent. If they simply trust a copied record without a verifiable trail, the system becomes too soft at the edges.
It feels a bit like carrying a stamped transit pass instead of retelling your route at every checkpoint.
What matters here, in my view, is that the protocol turns evidence into a structured onchain object rather than leaving it as an informal attachment to some separate process.
An attestation is not just a note that something happened. It is a claim with an issuer, a subject, a schema, a timestamp, and a verification path. That framing changes the role of infrastructure.
The chain is not trying to replace every institutional workflow. It is providing a common evidence layer so different workflows can produce outputs that other systems can verify without inheriting the whole internal machinery behind them.
That only works if the mechanism underneath is disciplined. The consensus layer has to decide which attestations become final and in what order, because sovereign or regulated environments cannot treat sequencing as a casual detail.
Finality matters when eligibility, compliance, payment release, or administrative status may depend on the exact moment a claim became valid.
The state model also matters. Evidence cannot behave like a loose message floating around the network. It has to sit inside a defined state transition model where issuance, update, revocation, and reference are all legible actions with distinct consequences.
I also think the schema model is doing more work than people sometimes admit. If one institution describes a claim one way and another describes it differently, interoperability becomes cosmetic. So the network’s value is not just that it stores attestations,
but that it anchors them to explicit structures that other participants can read consistently. That gives the evidence a reusable shape. A verifier does not need to guess what fields matter, what was signed, or what rule set the issuer intended to follow.
The cryptographic flow is where the design becomes practical rather than theoretical. An issuer creates a claim, signs it, and anchors that result so its integrity can be checked later. A relying party does not need blind trust in the issuer’s database.
It needs proof that the claim matches the signed structure, that it came from an authorized source, and that it has not been revoked or superseded. In stronger settings, selective disclosure or proof-based verification can reduce unnecessary data exposure, which is important because sovereign systems rarely want raw transparency everywhere. They usually want controlled verifiability.
That distinction matters. A lot of digital systems still confuse visibility with trust. I do not think that works at institutional scale. Real systems need evidence that can be validated without turning every underlying record into an open document.
That is why this architecture feels more serious to me than a simple registry model. It is trying to separate the proof that a condition is true from the need to expose everything surrounding that condition.
The utility model fits that logic in a fairly direct way. Fees support the cost of writing, verifying, and maintaining evidence-related activity across the chain.
Staking helps align validator or participant behavior around honest operation, which matters when the value of the system comes from confidence in the integrity and ordering of attestations.
Governance gives holders a way to influence upgrades, standards, and operating parameters, which is important because evidence systems are never static. Schemas evolve, compliance expectations change, and the rules for acceptable verification often need revision over time.
I do not view any of that through a price lens here. The more relevant point is whether the token functions map cleanly to the network’s role as shared proof infrastructure.
What stays with me is the design priority underneath it. The protocol is not mainly asking whether systems can exchange data faster. It is asking whether they can rely on evidence with less repetition, less ambiguity, and less dependence on private reconciliation behind the scenes.
That is a harder problem, but also a more durable one. My only real hesitation is that evidence layers often look coherent in architecture diagrams long before they prove they can handle institutional edge cases, competing standards, and governance pressure at real scale.
@SignOfficial #SignDigitalSovereignInfra $SIGN

