When I first dug into the idea of architectural invariants in digital identity systems, it reminded me of why I became fascinated with this space in the first place. I was standing on a street in Berlin, watching a friend struggle to prove who she was with three different apps on three different phones. There was promising tech, but everything felt fragile underneath the surface. I wasn’t looking for perfection, just stability. That search is exactly what these five invariants in @SignOfficial are trying to pin down.
Thinking about controllable privacy makes you realize how little control we actually have over our own identity data today. Public facing systems have trained us to overshare by default, and the result is a constant tradeoff between convenience and privacy loss. Controllable privacy says: keep the public public, but hold what’s private truly private. In practice that means data is visible only to those who need it, not anyone who can peek. When S.I.G.N. says “minimal disclosure by default,” it’s not marketing talk; it means you only reveal what is strictly necessary. If an airport needs to know you’re over 18, it doesn’t get your birthday, your passport number, and your last five addresses. That’s a texture of privacy most of us have never experienced, and it matters because every extra data point is a risk multiplier.
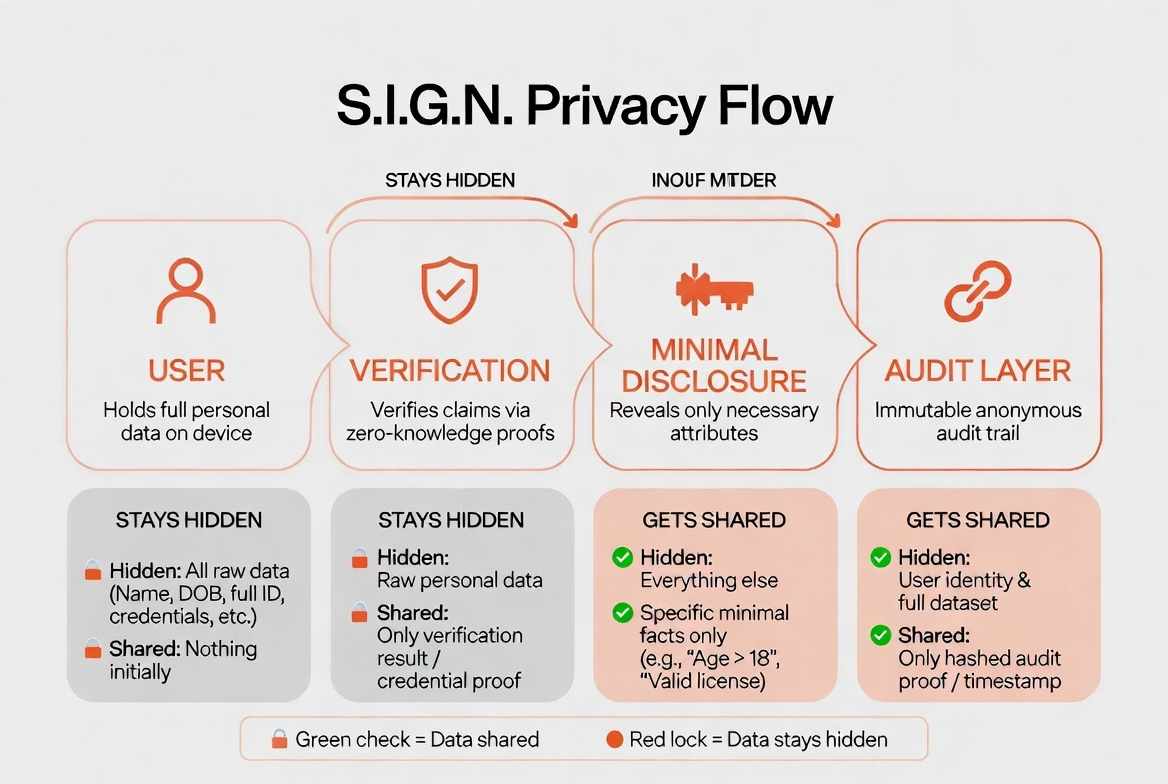
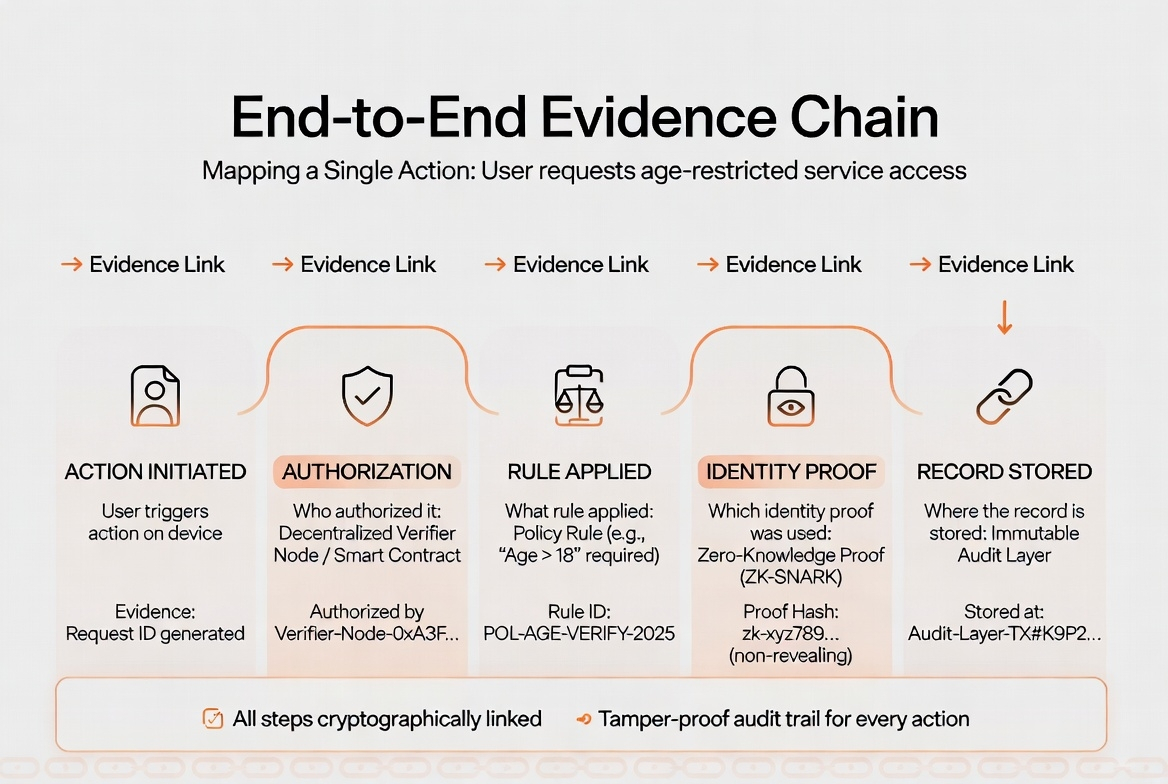
But privacy without auditable to lawful authorities is just a playground for bad actors. This invariant recognizes the tension: private to the public, auditable to authorities. Getting that right is complicated. You have to bake in evidence trails that even non‑technical auditors can follow. In S.I.G.N. every access event logs who did what, when, and based on which proof. That’s not a checklist item; that’s a foundation for trust, because without it sovereign entities can’t verify compliance, and citizens can’t trust the system themselves.
The second invariant, national performance, often gets overlooked because people fixate on privacy, which is more abstract. But when I looked at deployments in India’s identity system, which serves 1.3 billion people, the lesson was clear: scale is not optional. You can have the slickest cryptography in the world, but if it bogs down at peak times or fails across carriers, it’s useless. Multi‑operator workflows and strict service level agreements aren’t buzzwords. They determine whether a farmer in Punjab can access a subsidy before his window closes. “Millions of users” isn’t an exaggeration, it’s a requirement for any system that aims to be truly national.
Then there’s sovereign control. What struck me here is how often technology projects hand over too much power to third parties in the name of efficiency. Upgrades, key custody, and emergency controls stay with the sovereign with the state or entity that is responsible to its people. That doesn’t mean heavy‑handed control, but rather a clear accountability path. There’s texture here: under the surface, this invariant reshapes responsibility. It says that technology is a public utility, not a private black box.
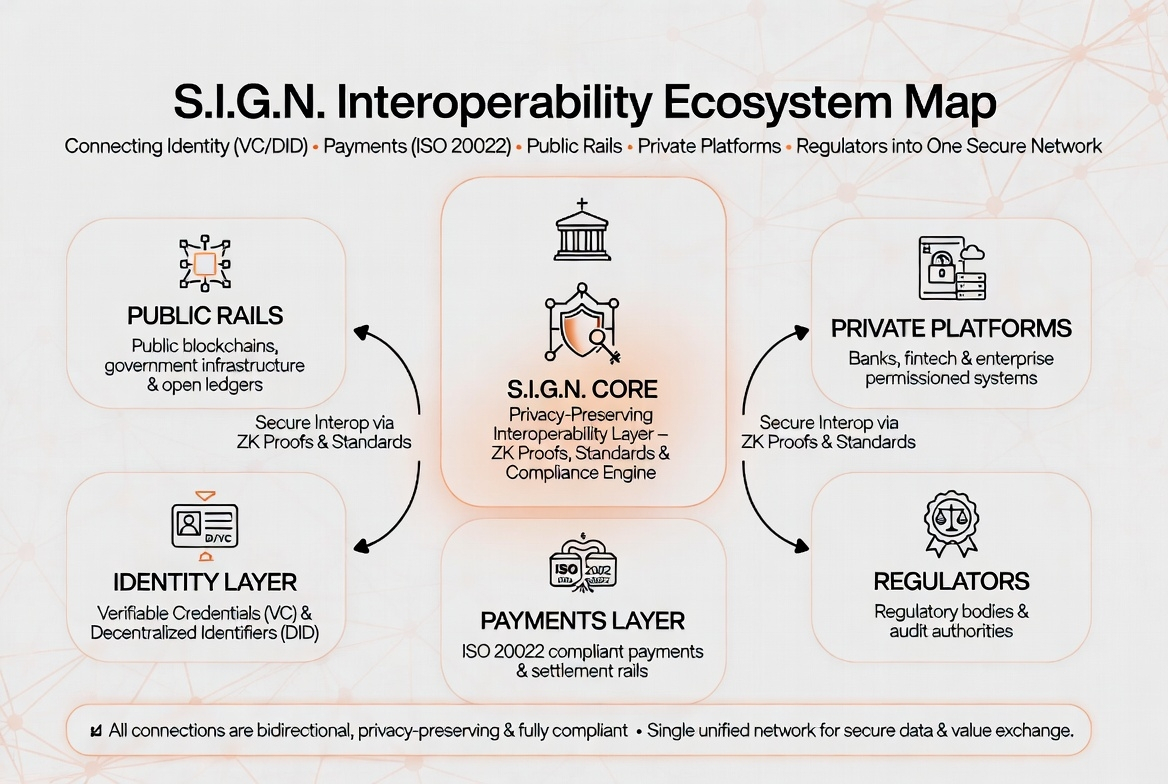
Interoperability ties all of this together. We’ve learned the hard way that silos kill adoption. Aligning with identity standards like VC and DID, using payments that speak ISO 20022, and being compatible with both public and private rails means you’re not building a closed garden. You’re building a network. The value compounds when wallets, banks, governments, and apps can all plug in with predictable behavior. One recent study found that systems built around standards see 30 to 50 percent higher integration success rates in the first year. That’s not a guarantee of success, but it’s a solid early signal.
All these invariants culminate in inspection‑ready evidence. That’s the quiet heart of the architecture. You don’t just log transactions; you create durable evidence of intent and authorization. That’s the texture that enables accountability without surveillance. It’s the difference between an audit trail that ‘might’ answer questions and one that actually does.
If this holds at scale, what we’re seeing isn’t just another identity framework. It’s an architecture that acknowledges the messy reality of public systems: billions of users, conflicting incentives, and the need for both privacy and oversight. The deeper pattern is unmistakable stability isn’t about locking everything down or opening everything up. It’s about invariants that persist no matter how the system grows.
And here’s the sharp observation that sticks with me: a system that can prove what it did, when it did it, and why it was allowed to do it isn’t just technically sound. It’s socially accountable, and that’s the real test of any national identity infrastructure.
