@MidnightNetwork #Night $NIGHT
The private core was fine.
Audit still spent the whole meeting at the trigger log.
Thats the version of Midnight I keep ending up back at.
Not the nice version where private smart contracts keep business logic sealed, selective disclosure keeps the room calm, and everybody acts like privacy solved the hard problem because the ugly part is no longer sitting in public. Good. Thats useful. Midnight $NIGHT should be doing that. Public chains are still absurd once the thing on-chain is a real internal process and not just speculative chaos pretending to be infrastructure.
Fine.
Hide the core.
See what happens next.
Because the more the interior gets sealed properly, the more scrutiny starts collecting at the interfaces. Inputs. Outputs. Triggers. Exception paths. External handoffs. Who can inject something into the private flow. What comes out of it. What wakes it up. What pauses it. What gets exported. What gets logged somewhere else because the system still has to touch reality eventually.
Of course they go there.
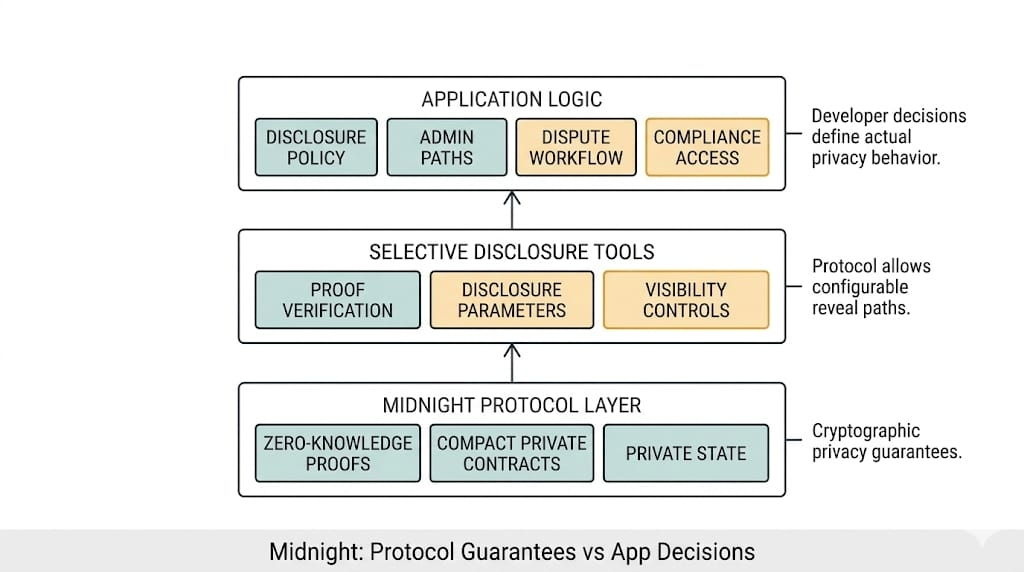
Take a private approval or treasury workflow on Midnight. Some hidden rule evaluates internal conditions and decides whether a release, threshold, or access path clears. The proof verifies. The business logic stays private. Good use case. Very Midnight. The whole point is that the most sensitive part of the process does not have to become public theater just because somebody somewhere decided “auditability” meant radical oversharing forever.
Good.
Now bring in a real control team.
They look at the hidden core once, realize they are not getting the cheap transparent-chain version of comfort, and then they start living at the boundaries like everybody in controls eventually does when the center of the system gets harder to inspect.
What fed the rule?
Who authorized the input on @MidnightNetwork ?
What external trigger woke the flow up?
What exactly got emitted on the way out?
What happens on exception?
Who can override?
What gets handed to another system?
What gets retained?
What gets silently dropped because the private logic says it was never relevant?
That is the surface everybody ends up stuck on.
And the annoying part is they’re not wrong.
One stale trigger timestamp and suddenly nobody cares how elegant the private core was.
Because once Midnight network makes the core harder to inspect directly, the edges stop being support structure. They become the only parts everyone else can still lean on. The interface stops being plumbing. It’s where trust gets priced, documented, challenged, maybe quietly broken.
I've watched teams call the core verified while half the real risk was sitting in the handoff nobody wanted to own.
I’ve seen this in enough boring enterprise systems to know how it goes. Nobody gets the elegant central explanation they wanted, so they compensate by becoming obsessive about the seams. Input validation. Trigger ownership. Timestamp consistency. Export logic. Review states. Retry behavior. Exception routing. All the ugly little places where the private core has to touch some less-private neighbor.
One trigger came in from an external service with a stale timestamp. The private yes still propagated. Downstream reconciliation did not enjoy that.
That’s the inversion, really.
Seal the middle well enough and everyone starts clawing at the seams instead.
Not because the core stopped mattering.
Because the core got harder to inspect cheaply.
So the auditors move outward. The counterparties move outward. The risk team moves outward. And pretty soon the whole argument is happening at the edges.
Say a private treasury rule on Midnight approves a release if internal conditions clear. Fine. The proof says yes. The sensitive reasoning stays sealed. Then audit comes in and does not start with “show us the hidden rule.” They start with the trigger source, the approval handoff, the exception queue, the outbound record, the settlement timestamp, the external system reconciliation. Because that’s where they can still grab the system with both hands.
That is what happens.
Not privacy makes auditing impossible.
That’s lazy.
It makes auditing relocate.

And relocated scrutiny gets weird because boundaries are usually where systems are messiest. The core logic may be beautifully private, formally verified, very adult, all of that. Meanwhile the trigger came from an external service with fuzzy guarantees, the export format got interpreted differently downstream, the exception path has one admin role too many, and the retry logic leaves weird little scars no one remembered to explain in the controls memo.
Great. The center is elegant. The edges are where the body is bleeding.
Very enterprise. Very adult. Still bleeding.
So no, I don’t think Midnight’s hard institutional problem is only proving the private logic correctly.
It’s whether the edges can survive that much distrust once everyone starts leaning on them at once.
A counterparty may accept the private logic in theory and still refuse to rely on the system if the handoff semantics feel weak. Weak handoff, weak export, weak trigger ownership. Doesn’t take much. The core can still be fine.
An auditor may be perfectly satisfied that the hidden rule exists and still hammer the exports, triggers, and exception paths until the product team starts wishing the core had been the problem instead.
I keep ending up back there.
Midnight can seal the core. Good. It should.
The uglier question is what happens when the whole room stops trusting the middle and starts living at the seams instead. #night