$SIGN #SignDigitalSovereignInfra
The record looked finished on @SignOfficial .
That was the problem.
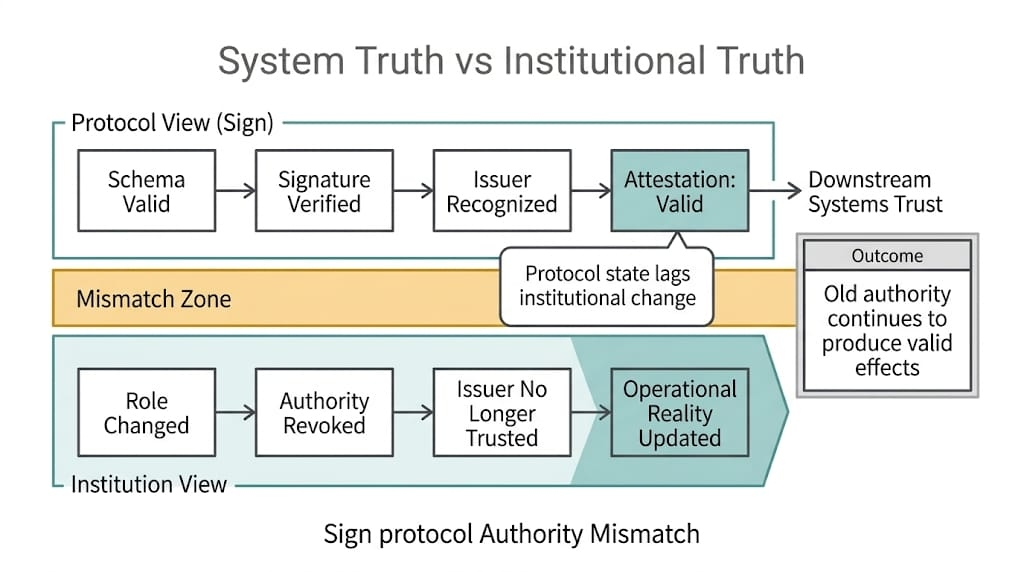
Sign's Schema matched. Issuer signed. Status clean. SignScan shows something nice and legible. Query layer can pull it later without drama. Great. Very civilized. Meanwhile half the approval was still sitting offchain in a case system, a CRM note, a manual hold, some side comment a reviewer understood perfectly at the time and nobody else was ever going to see again.
And then the attestation gets treated like it settled all of it.
That is the leak.
Not forged data. Not broken signatures. Not some clean exploit story people can point at and feel clever about. Worse. The record is real. The reviewer really did sign. The subject really did clear something. The problem is that what got signed was only the durable slice of a workflow that still had soft parts hanging off it.
Still pending refresh.
Still provisional in someone’s notes. Anyways.
Still “good for this round” and not much more than that.
Nice clean record. Missing half the case.
I keep coming back to the same Sign's miserable sequence. Case comes in. Ops or compliance or some review team works it in an offchain system first, because obviously they do. Documents checked there. Manual flags there. Exceptions there. Maybe a sanctions refresh pending. Maybe a residency note that still needed confirmation. Maybe another team said proceed for route one but do not treat this as final for route two until the file closes properly.
Then the attestation gets issued.
Fine.
Maybe not fine. Maybe just early.
Because once it is in Sign sovereign infrastructure, it starts looking finished in a way the case behind it never was. That is what Sign is good at. It takes some prior judgment and gives it shape. Schema. issuer. signature. evidence surface. Reusable later. Good. Useful. Nobody wants the next system calling back into case notes every time it needs a yes or no.
But what exactly did the attestation settle.
That the subject was fully clear.
Or that the subject was clear enough at that moment, under whatever offchain assumptions still happened to be true.
Those are not the same thing. They only start sounding the same once the record gets portable and the messy dependencies stay trapped outside it.
TokenTable is an obvious place this goes bad. Claims filter sees valid attestation under the right schema and keeps moving. Why would it not. Nobody gave it the reviewer’s side note. Nobody gave it the pending refresh. Nobody gave it the manual hold that lived in the CRM for forty-eight hours before somebody remembered to update it. Same with access systems. Same with partner integrations. Same with reporting, which is worse in its own dead spreadsheet way because reporting will flatten anything if it means the row count looks calm.
Calm row. Unfinished case.
And that part never really made it onchain.
Maybe the reviewer knew the approval was narrow. Maybe they understood it as “safe enough for this route, not the next one.” Maybe they were relying on another team to close the remaining check later. Maybe the offchain file changed the next day. Maybe the CRM flag got corrected. Maybe the hold was removed. Maybe it was added. The point is the attestation comes out looking harder than the admin process behind it actually was.
That should make people nervous.
Usually it makes them relaxed.
Because a clean Sign $SIGN record invites trust fast. Signature. issuer trail. schema reference. queryability. Looks settled. Looks reusable. Looks like the next system does not need to know about all the grime that fed into it. That is the convenience. Also the trap.
Portable record. Unresolved file.
I do not think people are honest enough about that split. Not because they are malicious. Because the whole workflow gets simpler if they pretend the attestation swallowed the whole case. Simpler for engineering. Simpler for ops. Simpler for distribution. Simpler for whoever is trying to ship without reopening the ugly offchain process every time.
Simple. Right.
Then the next system reads claim presence. Maybe status. Maybe issuer. Maybe schema family. It does not read the case note saying pending sanctions refresh. It does not read the comment saying route one only. It does not read the temporary exception somebody approved under deadline pressure and never meant to become reusable permission later.
So the wallet stays in scope.
Or the gate stays open.
Or the subject keeps showing up as clean in reporting.
And the answers afterward are always the same wrong ones. Treasury asks why the wallet was still eligible. Ops says the attestation was valid. Engineering says it still verifies. Compliance says the offchain file changed later.
Useful detail to surface after the relying layer already treated the compact signed record like the whole truth.
That is the ugly Sign pressure here. Not that the attestation is false. That it can be perfectly real and still incomplete in exactly the way the next system is least equipped to respect. The protocol keeps the durable part. Good. Necessary. But whatever never made it into the durable part does not magically stop mattering just because Sign made the visible part look clean.
Clean surface. Wet paint underneath.
And once that record starts moving through claims logic or access control like the side conditions were gone, the missing parts do what missing parts always do.
They come back later.
Usually after the money moved.
