There has been a change in how people talk about identity in crypto. A years ago the conversation was mostly about ownership.
Wallets
Keys
Self-Sovereignty
The idea was simple: if users control their identity everything else will follow. That assumption has not really played out.
Owning identity and actually using it in real-world transactions are two very different things.
The gap between owning identity and using it is where Midnight Network is trying to position itself.
Not as another identity layer. As a bridge between digital identity and application.
The problem is subtle but important.
Most digital identity systems today can prove who you are. They struggle to prove what matters in context.
For example proving compliance without revealing data or verifying eligibility without exposing credentials.
In systems this is handled by intermediaries.
In crypto that model breaks the moment privacy and decentralization are taken seriously.
Midnights approach to data protection is built around this tension.
It treats identity as something that can be selectively revealed, verified and executed against, rather than a static asset.
This is not about zero-knowledge proofs as a concept. About making them usable inside applications in a way that developers can actually integrate without breaking the user experience.
That is where the programmable part starts to matter.
If digital identity data can be embedded into contracts with grained control over visibility then digital identity stops being passive.
It becomes functional.
It becomes something that can actively participate in transactions, governance and compliance workflows.
From a market perspective this distinction is starting to show up in signals.
Liquidity for instance is no longer about trading volume.
It reflects confidence in whether a networks utility will translate into usage.
Projects that focus purely on narrative often see liquidity spikes followed by sharp drops.
In contrast ecosystems that build around application layers tend to develop more stable liquidity profiles.
Holder distribution tells a story.
A concentrated token base usually signals accumulation, not long-term belief.
If Midnights ecosystem evolves toward distribution that would indicate something organic: users interacting with the Midnight Network because they need its functionality, not just its token.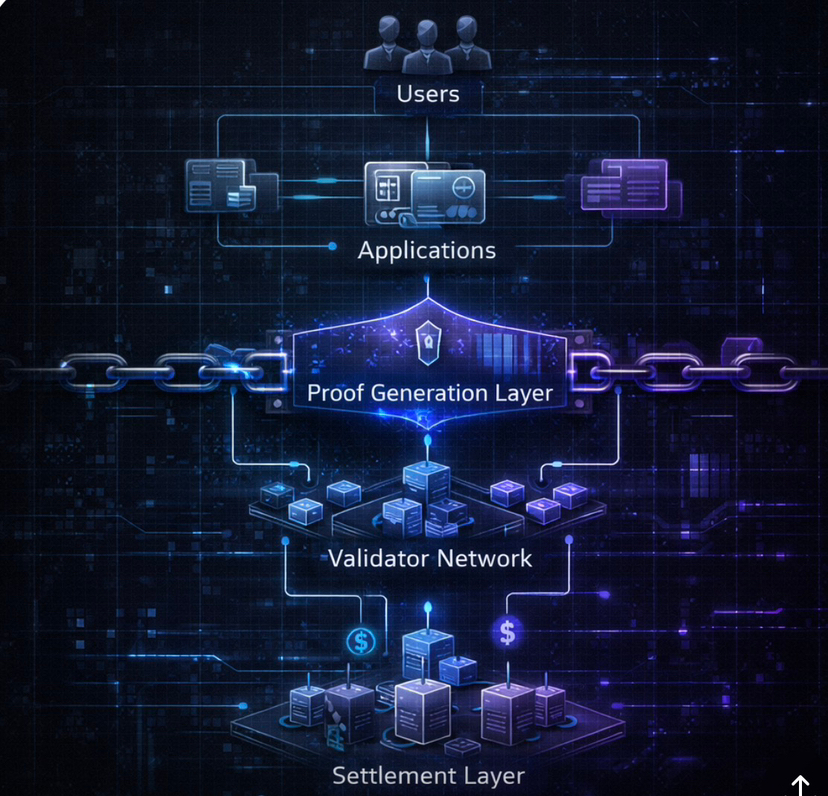
Organic demand is the differentiator here.
It is easy to generate attention in crypto. It is much harder to create systems people rely on.
Midnights bet is that privacy, when tied directly to usability and compliance can become one of those needs.
That is where its relevance to trust and regulation becomes clearer.
Privacy in isolation often raises concerns from regulators.
Programmable privacy, where data can be verified without being exposed aligns closely with compliance requirements.
It allows institutions to meet standards without compromising user confidentiality.
In that sense Midnight is not positioning itself against regulation.
It is positioning itself as a tool that could make compliance more efficient and less intrusive.
That is a difference especially as global frameworks around digital identity and data protection continue to evolve.
Course execution is everything.
The concept is strong. Adoption depends on whether developers actually build on it and whether users find value in those applications.
Without that even the elegant architecture remains theoretical.
Still the direction is notable.
Bridging the gap between owning identity and using it in transactions is one of the harder problems in Web3.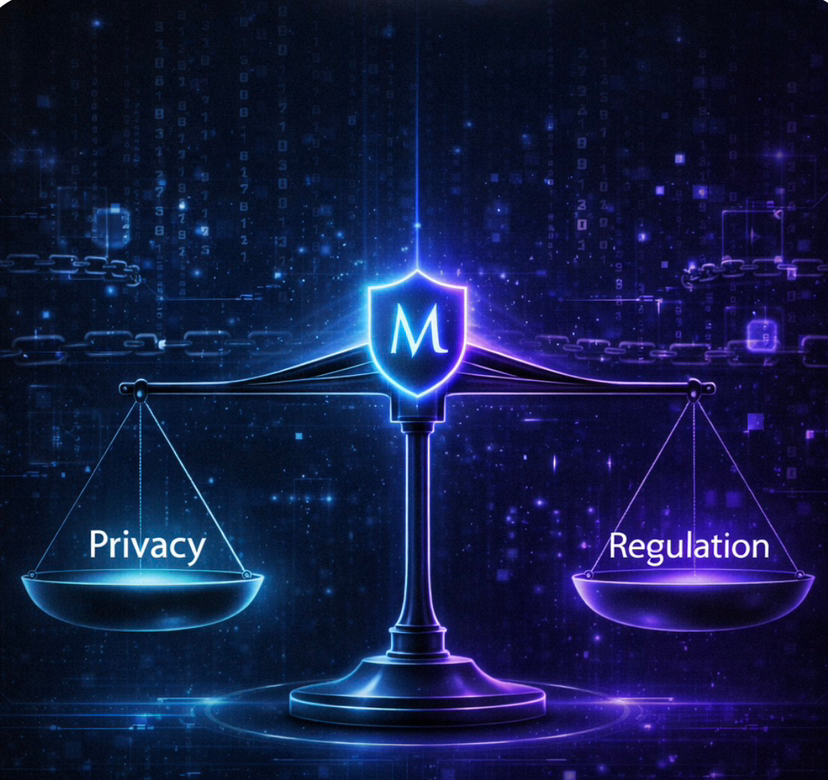
If Midnight can make that bridge practical not just possible it could shift how digital identity is understood across the space.
Not, as something you hold. As something you use digital identity could become more functional.
Midnight Network is trying to make digital identity more usable.