I keep noticing the same pattern in digital infrastructure: people likes to talk about applications, but the real bottlenecks usually sit one layer deeper. A government can launch a CBDC pilot. A fintech can issue a regulated stablecoin. A platform can tokenize real-world assets. An agency can modernize identity systems. On the surface, these look like different initiatives. In practice, they run into the same hard questions almost immediately. Who is allowed to do what? How are rules enforced without making systems rigid? How do records stay inspectable over time? And how do you do all of that without turning privacy into collateral damage?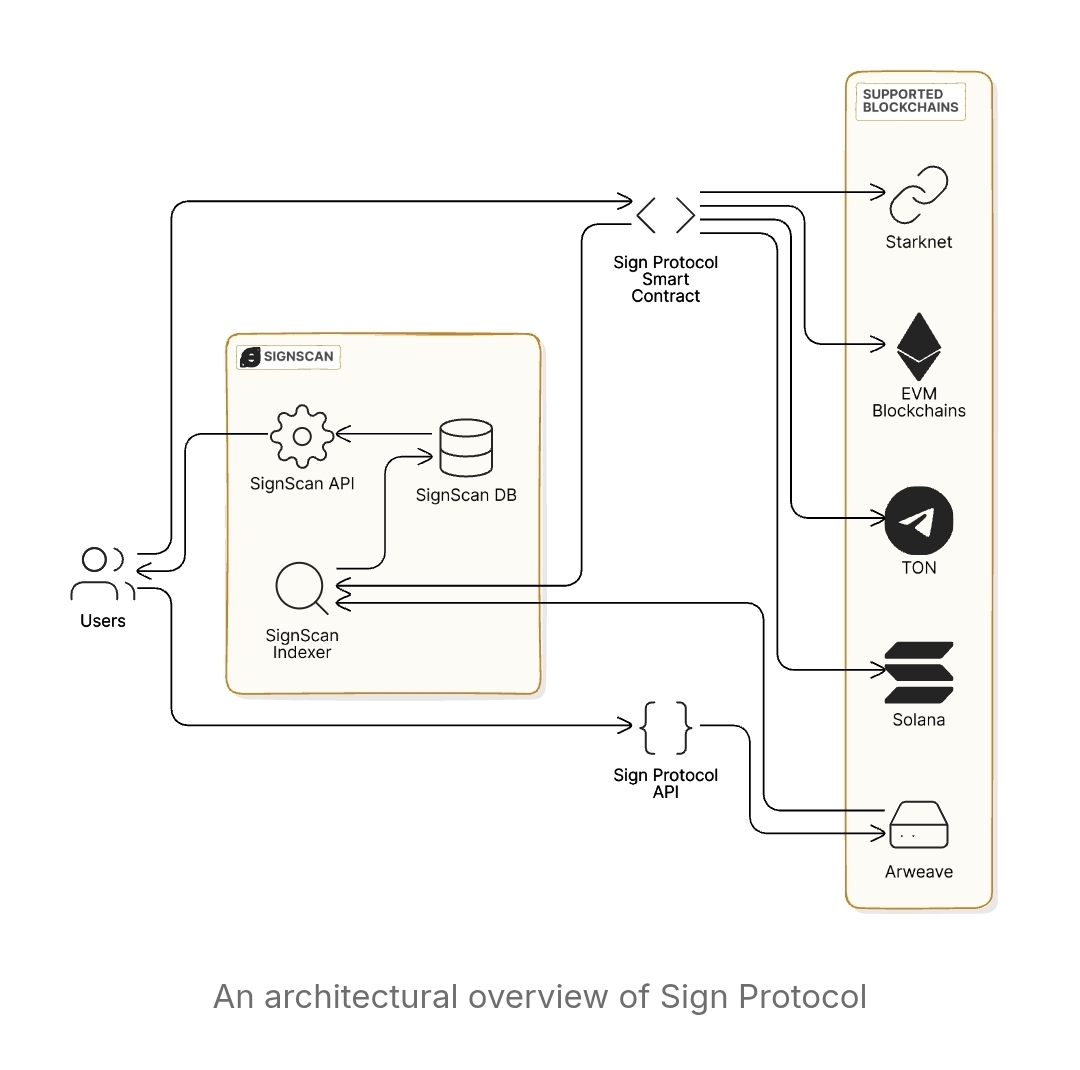
That is why S.I.G.N. stands out to me.
What catches my attention is not just the idea of another protocol, but the way S.I.G.N. is positioned as sovereign-grade digital infrastructure for money, identity, and capital at national scale. That framing matters. It tells me this is not being built for isolated demos or short-lived experiments. It is being aimed at environments where compliance, interoperability, continuity, and auditability are not optional. They are the baseline.
From a builder’s perspective, that changes how the whole stack should be judged.
The clearest way to understand S.I.G.N., in my view, is not as a single product, but as three interoperable systems working together. The New Money System is designed for CBDCs and regulated stablecoins, and it allows them to operate across both public and private chains. That feels realistic. Serious deployments are unlikely to live forever in only one environment. Some will want the transparency and composability of public L1s or L2s. Others will need the confidentiality and controlled access of private rails. A serious infrastructure layer has to support both, and more importantly, the movement between them.
Then there is the New ID System, which to me sits at the center of everything else. Digital systems start to fail quickly when identity is weak, fragmented, or too invasive. S.I.G.N.’s use of verifiable credentials, DIDs, selective disclosure, and trust registries points toward a model where identity does not automatically mean overexposure. That matters more than people sometimes admit. Too many systems still treat eligibility checks as an excuse to collect more information than the task actually requires. Builders thinking beyond the next release cycle should pay close attention to that, because privacy-preserving verification will only become more important as these systems grow.
The New Capital System completes the picture.
This is where tokenized real-world assets, grants, subsidies, incentives, vesting, and identity-gated participation start to feel like part of the same operational family. Capital distribution sounds straightforward until real-world constraints enter the room. Eligibility, compliance, reporting, monitoring, audit trails suddenly it stops being a simple transfer problem. It becomes a coordination problem built around rules, records, and trust.
And that leads to the layer I think builders should study most carefully: Sign Protocol.
All three systems depend on a shared trust and evidence layer, and that is where Sign Protocol fits. To me, this is one of the strongest parts of the architecture because it addresses a problem many teams underestimate until scale forces them to confront it. Blockchain data fragments fast. Some of it lives in contracts, some in off-chain storage, some across multiple chains, and some inside custom indexing pipelines that few outsiders can read without effort. Once that happens, auditing gets messy, historical changes become harder to trace, and integrations turn into ongoing infrastructure work.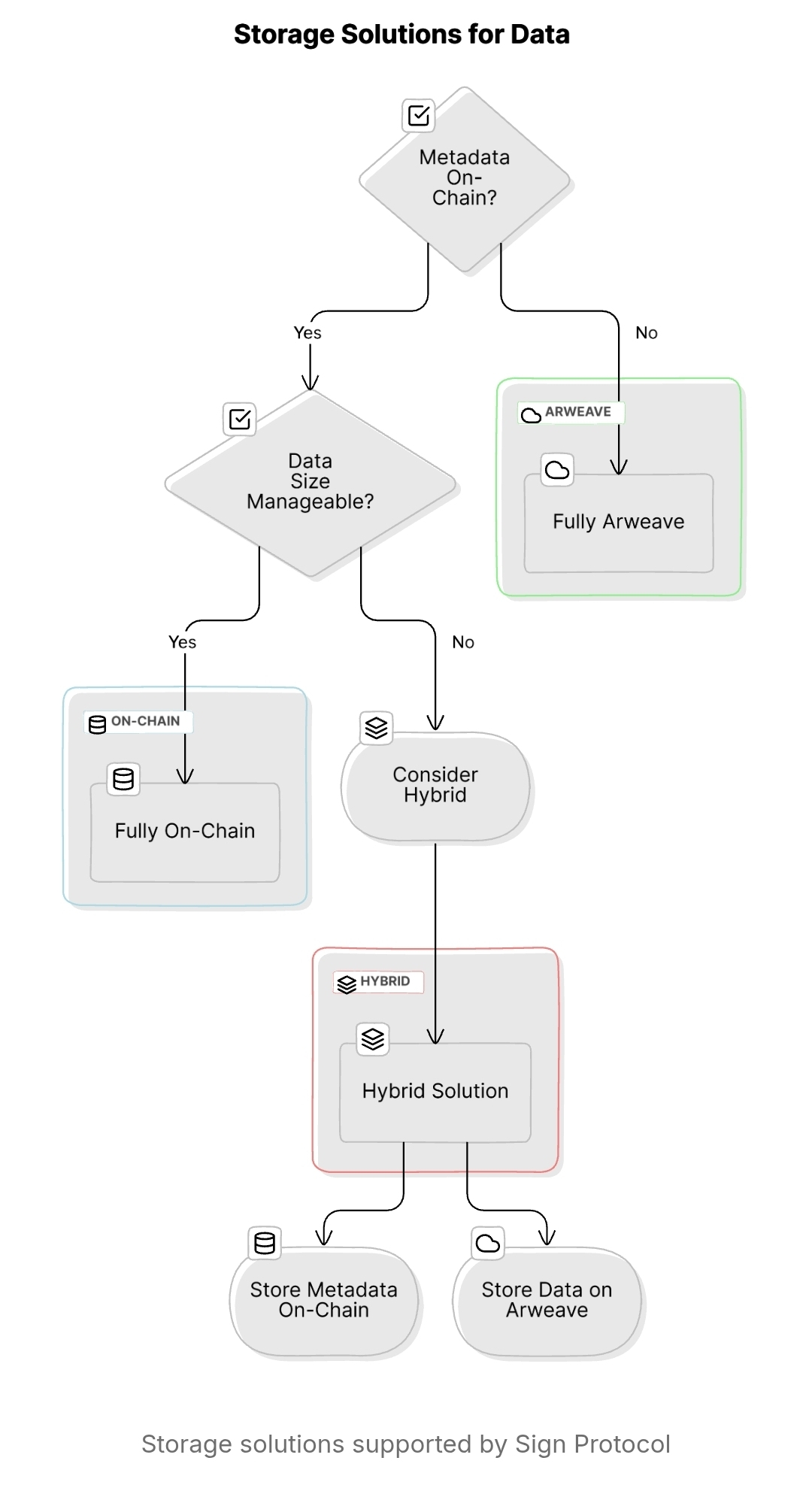
That is expensive, and it is rarely elegant.
Sign Protocol looks like an attempt to standardize how structured claims are defined, written, linked, discovered, and queried over time. The core primitives are clear: schemas define structure, and attestations are signed instances of data that follow that structure. For builders, that is valuable because it creates consistency without forcing every application to invent its own evidence framework from scratch.
I also think the storage flexibility is practical rather than decorative. Teams can choose fully on-chain storage, fully Arweave-based storage, or hybrid models that combine on-chain references with off-chain payloads. That gives builders room to balance cost, permanence, accessibility, and privacy according to the use case. Not every record belongs fully on-chain, and systems that pretend otherwise usually end up with awkward tradeoffs later.
Reading matters just as much as writing.
A system is only as useful as its ability to surface meaningful information when someone actually needs it. Direct contract reads or Arweave reads are possible, but those approaches can become clumsy when filtering, aggregating, or comparing records across environments. SignScan looks important here because it acts as the indexing and aggregation layer, with REST and GraphQL APIs that unify supported chain data. That means builders can spend less time dealing with raw data layouts and more time focusing on workflows, policy logic, and actual user outcomes.
That is the kind of detail I respect in infrastructure design.
What makes S.I.G.N. compelling is that it seems to recognize a truth many systems still ignore: sovereign and regulated infrastructure is not won by elegant theory alone. It is won by whether identity, policy, evidence, execution, and reporting can work together without collapsing into duplication, opacity, or surveillance-heavy design. Money, ID, and capital are usually treated as separate verticals. S.I.G.N. treats them more like connected state functions built on shared trust rails.
For builders, that should be the real signal.
My conclusion is simple: S.I.G.N. is worth attention not because it sounds ambitious, but because it is aimed at the layer where modern digital systems usually become fragile. Builders who understand that early may have an advantage much sooner than they expect.
@SignOfficial #SignDigitalSovereignInfra

