The more I reflect on Midnight Network's design, the more I see it confronting one of crypto's most persistently avoided realities: privacy isn't just a feature you toggle on—it's a structural requirement for anything serious, yet most chains treat it as an afterthought or a marketing checkbox.
Projects love to chase spectacle—flashy DeFi yields, viral memes, layer-2 speed wars—while quietly ignoring how exposed ledgers make real-world adoption impossible for regulated entities, AI systems handling proprietary data, or even basic confidential coordination. Midnight doesn't chase that noise. It starts from the opposite premise: if verifiable computation is going to matter beyond speculation, it has to be rational about privacy from the ground up. Not total anonymity that invites abuse and regulatory shutdowns. Not forced transparency that scares off enterprises. Rational privacy: prove what's necessary, shield the rest, make it programmable and developer-accessible.
That's why the architecture feels weightier than the usual hype cycle.
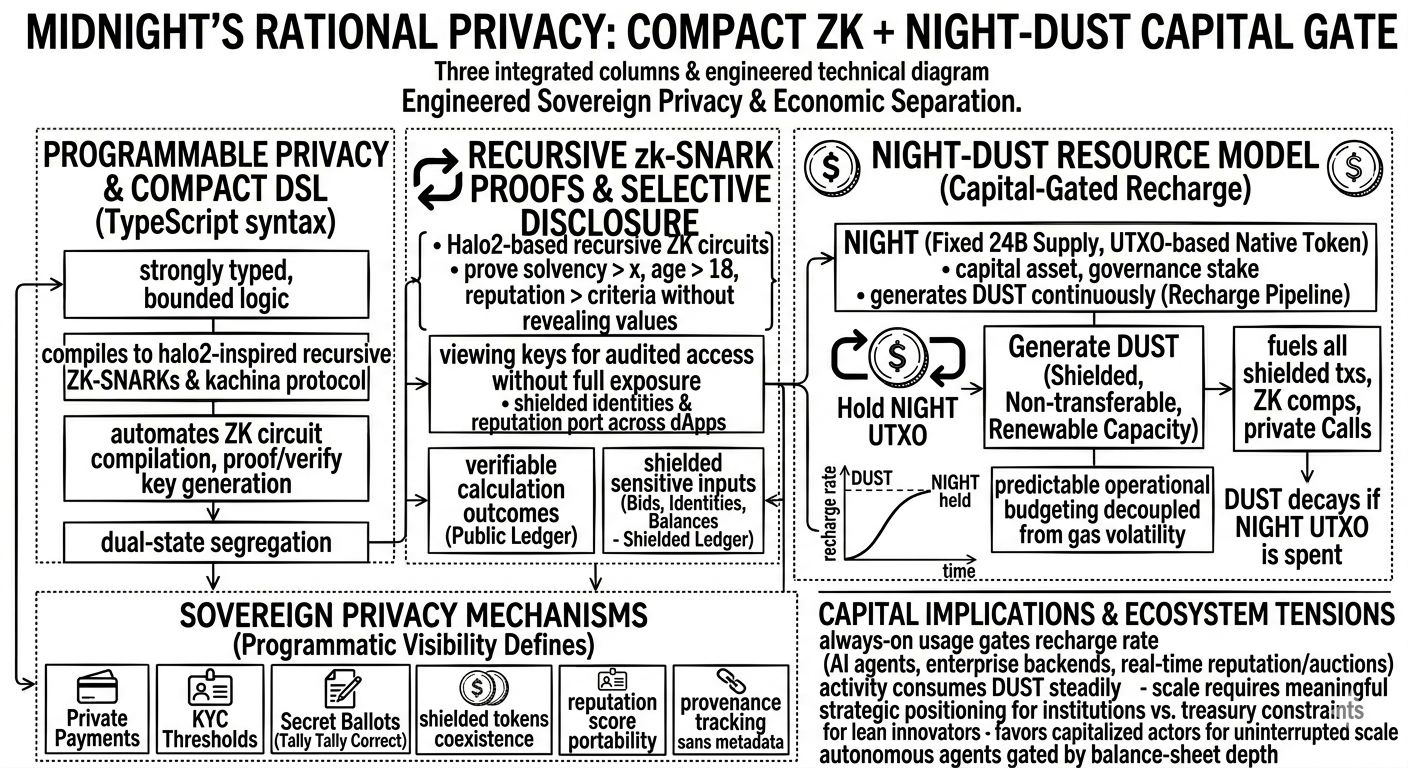
Compact stands out as the quiet engineering win. A TypeScript-derived, strongly typed DSL that compiles to zk-SNARK circuits via recursive proofs (built on Halo2-inspired tech and Kachina protocol foundations). Developers write familiar syntax—no need to master Rust macros, Circom constraints, or low-level ZK plumbing. Compact handles the dual-state segregation: public ledger for verifiable outcomes (e.g., auction cleared, compliance attested), shielded ledger for sensitive inputs (bids, identities, balances, ML model params). The compiler generates the cryptographic materials automatically—proof keys, verification keys, circuit descriptions—letting engineers focus on logic instead of wrestling with ZK hardness. This isn't incremental tooling; it's a deliberate bridge to bring millions of mainstream devs into programmable privacy without retraining them as cryptographers.
Layer on selective disclosure: viewing keys for audited access, zero-knowledge attestations for thresholds (prove solvency > X, age > 18, reputation score meets criteria) without leaking values. Shielded tokens coexist with public ones. Provenance verifies origin integrity sans metadata trails. Secret ballots tally correctly while votes stay hidden. Private payments move value without wallet surveillance. Reputation ports across dApps without trailing histories. These aren't exotic add-ons; they're native expressions of the dual-ledger + recursive ZK design.
Then the resource layer—NIGHT and DUST—introduces cooperative economics that sidesteps classic pitfalls. NIGHT (fixed 24B supply, UTXO-based native token) serves as capital asset, governance stake, and recharge generator. Hold NIGHT, and it continuously mints DUST—a shielded, non-transferable, renewable capacity resource. DUST fuels all shielded txs, private contract execution, ZK computations; regenerates over time toward a cap proportional to holdings; decays if underlying NIGHT UTXO spends. No spot-market gas volatility. No direct token burns. Predictable operational budgeting decoupled from price swings. For steady workloads, it's elegant: treasury reserves translate to sustainable throughput.
I respect this refusal to skip the boring-but-essential parts. Midnight tackles fragmentation head-on—privacy that travels across dApps, compliance without compromise, dev onboarding without PhDs, costs without chaos. It aligns with real friction: enterprises need confidentiality + auditability; AI agents need shielded coordination; regulated flows need selective proofs. The vision connects directly to how systems actually scale when sensitive data is involved.
But the capital dimension remains the unavoidable tension.
Always-on, high-frequency use cases—persistent AI agents proving/adjusting in shielded loops, enterprise backends running continuous private workflows, real-time reputation or auction systems—don't throttle to polite recharge rates. They consume DUST steadily. DUST scales with NIGHT held. Meaningful scale therefore demands meaningful NIGHT reserves to maintain smooth generation. Institutions can treat this as infrastructure capex—lock it up, plan around it, call it strategic. Smaller builders, startups, indie protocols? They encounter a different reality: prove product viability first by securing enough capital to keep the shielded pipeline flowing. It's not user-facing fee spikes anymore. It's upstream treasury constraint before traction.
That quietly reshapes accessibility. Technical sophistication (Compact abstraction, recursive zk-SNARKs, dual-state contracts, selective disclosure) enables powerful private apps. Economic model (NIGHT → DUST recharge) ensures predictability and spam resistance. Together they favor actors who can afford sustained exposure to the base asset. Well-capitalized players dominate uninterrupted scale; lean innovators face a "capitalize first" hurdle. AI-heavy or enterprise narratives amplify this: autonomous agents sound decentralized until their shielded activity is gated by balance-sheet depth.
This isn't a flaw in isolation—it's the trade-off of disciplined design. Midnight could thrive in regulated finance, confidential AI, provenance chains—potentially owning the niche where privacy is mandatory. But if broad, grassroots participation requires upfront capital heft for persistent operation, the network serves deep-pocket actors most fluidly.
That's the edge I keep circling. Rational privacy is only as open as the resource model allows in practice. If the answer lands as "elegant for institutions that warehouse NIGHT, constraining for everyone else at meaningful scale," Midnight succeeds—but in a narrower band than the freedom-of-association/commerce/expression rhetoric implies.
Not universal Web3 restoration.
More like production-grade private infrastructure for those positioned to keep it charged.
$SIREN $RIVER #TrumpConsidersEndingIranConflict #iOSSecurityUpdate #BinanceKOLIntroductionProgram