I have noticed something about how systems handle information.
Most of them are built on the assumption that more data leads to better outcomes.
More inputs improve decisions.
More visibility increases trust.
More information creates stronger systems.
That assumption has shaped both traditional systems and blockchain networks.
If you want to verify something, you collect more data. If you want to build trust, you expose more information. If you want to reduce uncertainty, you expand what is visible.
Over time, that approach creates a pattern.
Systems become dependent on information they may not actually need.
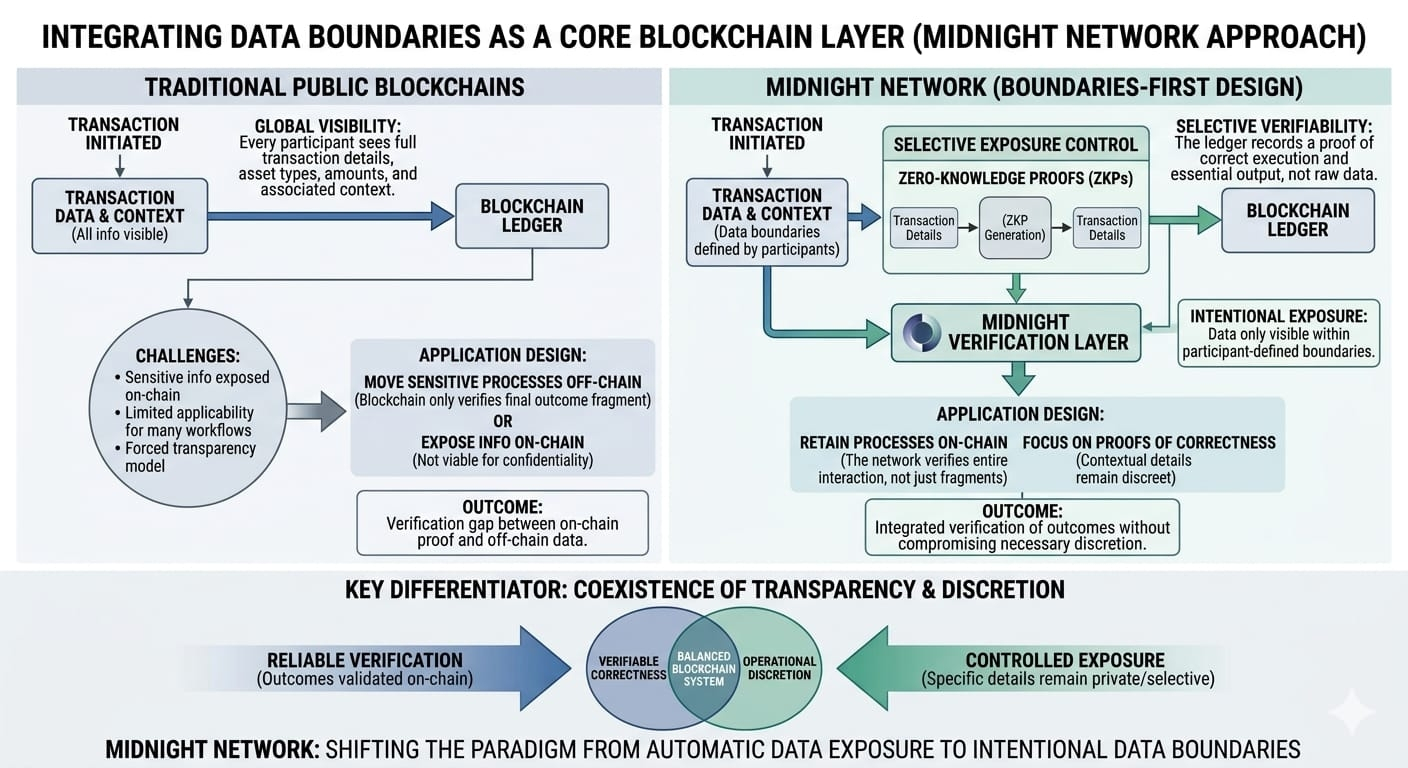
Midnight Network approaches this problem from a different direction.
Instead of asking how to protect more data, it asks a more fundamental question.
What if the system did not require that data in the first place?
This is where zero-knowledge systems introduce a different model.
Instead of exposing inputs to prove an outcome, the system can confirm that the outcome is valid without revealing how it was produced. The proof replaces the data.
This changes the structure of how systems can operate.
In a traditional model, verification depends on access. You need to see the information to confirm that it is correct.
In Midnight’s model, verification depends on proof. You do not need access to the underlying data as long as the system can demonstrate that the conditions have been satisfied.
This creates a more efficient way to handle information.
Systems no longer need to store, transmit, or expose unnecessary data. They can operate using only what is required to validate outcomes.
The implications of this approach become clearer in environments where data sensitivity is not optional.
A user may need to prove eligibility without revealing personal details.
A business may need to confirm compliance without exposing internal processes.
A system may need to validate a result without sharing the inputs behind it.
In these situations, reducing the amount of required data is more valuable than protecting it after exposure.
Midnight’s design allows systems to operate with less information while maintaining trust.
This introduces a different perspective on privacy.
Privacy is often framed as a defensive measure. Something that protects data from being accessed.
In this model, privacy becomes structural.
The system simply does not require the data to function.
That distinction matters because it changes how applications are built.
Developers no longer need to design around the assumption that information must be collected and then protected. They can design systems that minimize data requirements from the start.
Users no longer need to rely on trust that their information will remain secure. They interact with systems that do not demand that information in the first place.
But like all infrastructure shifts, the concept only becomes meaningful when it is applied.
Most existing systems are built around data-rich models because they are familiar and easy to implement. Transitioning to a model that reduces data requirements requires new ways of thinking about verification and system design.
This transition takes time.
It develops as more use cases appear where traditional approaches become inefficient or risky.
Midnight is positioned around that transition.
It assumes that future systems will prioritize efficiency in how data is used, not just security in how it is stored.
If that assumption proves correct, systems that rely on proof instead of exposure may become more relevant.
If adoption develops slowly, the model may take time to become widely understood.
This uncertainty is common for infrastructure.
The systems that redefine how information is handled often begin as alternatives before they become standards.
Midnight is exploring what happens when systems are built to require less data rather than protect more of it.
That shift may seem subtle.
But it changes the foundation of how trust and verification can work.
Not by hiding information.
But by making it unnecessary.
#night $NIGHT @MidnightNetwork 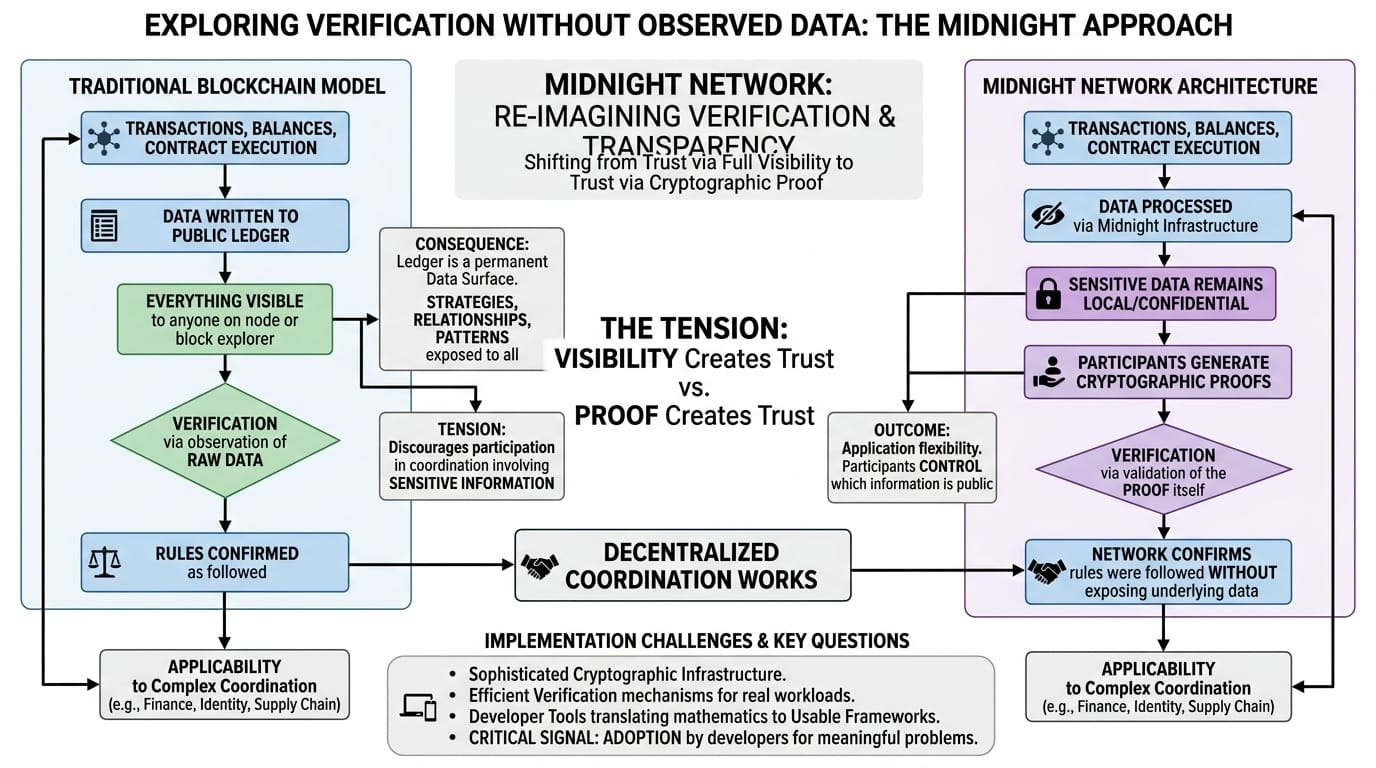
#Trump's48HourUltimatumNearsEnd #TrumpConsidersEndingIranConflict #BinanceKOLIntroductionProgram $JTO

