been tracking the S.I.G.N. Reference Architecture docs for a few days now and the deployment-mode flexibility is the part that keeps pulling me back 😂
honestly? most people read the headline — three sovereign systems (Money, ID, Capital) unified under one evidence layer — and stop there. the headline is accurate and the ambition is genuinely national-scale. but the footnote underneath it is the thing worth sitting with.
S.I.G.N. was designed from the start to support public L1/L2, private permissioned rails, and hybrid configurations running in parallel. No phased “rip-and-replace.” The whitepaper frames this as pragmatic reality for sovereign deployments — balancing transparency needs, confidentiality mandates, and performance under concurrency as requirements evolve. That framing is fair as far as it goes. Public mode gives verifiable transparency, private mode protects sensitive flows, hybrid lets you prove compliance publicly while executing privately.
what the framing doesnt fully address is what changing deployment modes normally means at the infrastructure layer. this isnt swapping a payments processor or upgrading a database. these are the cryptographic anchors that every agency, bank, and verifier trusts for eligibility proofs, settlement records, and ownership provenance. the trust registry, schema IDs, and attestation anchors have to survive the switch.
every integration that any government department, regulator, or third-party service built against the original rail has to keep working when you add or shift modes.
the design gets the underlying principle right
the whitepaper explicitly commits to omni-chain Sign Protocol primitives and W3C standards — which means schemas and attestations are portable by construction. an attestation anchored on a public L2 can be referenced from a private rail (or vice-versa) without re-issuing credentials or rebuilding trust registries, provided the hybrid bridging and anchor commitments are maintained.
what i kept working through is the gap between theoretically portable and operationally bulletproof. standards compliance is necessary, not sufficient. every cross-mode query, every selective-disclosure proof, every audit manifest must resolve identically during the transition window. every verifier integration must handle dual anchors without downtime.
running three deployment modes from day one on a live national system is either exactly the kind of forward-looking architecture that prevents the migration pain other countries are still suffering, or a signal that the complexity of simultaneous public-private-hybrid orchestration hasn’t been stress-tested at full sovereign concurrency yet.
honestly dont know if the S.I.G.N. model shows a blueprint that finally lets governments evolve infrastructure without disrupting 750k+ citizens, or a system that traded simplicity for ultimate flexibility and is still proving the sync layers can hold.
pioneering sovereign infrastructure that earns the right to call itself migration-proof — or a live architecture still betting that hybrid reality will stay perfectly aligned?? 🤔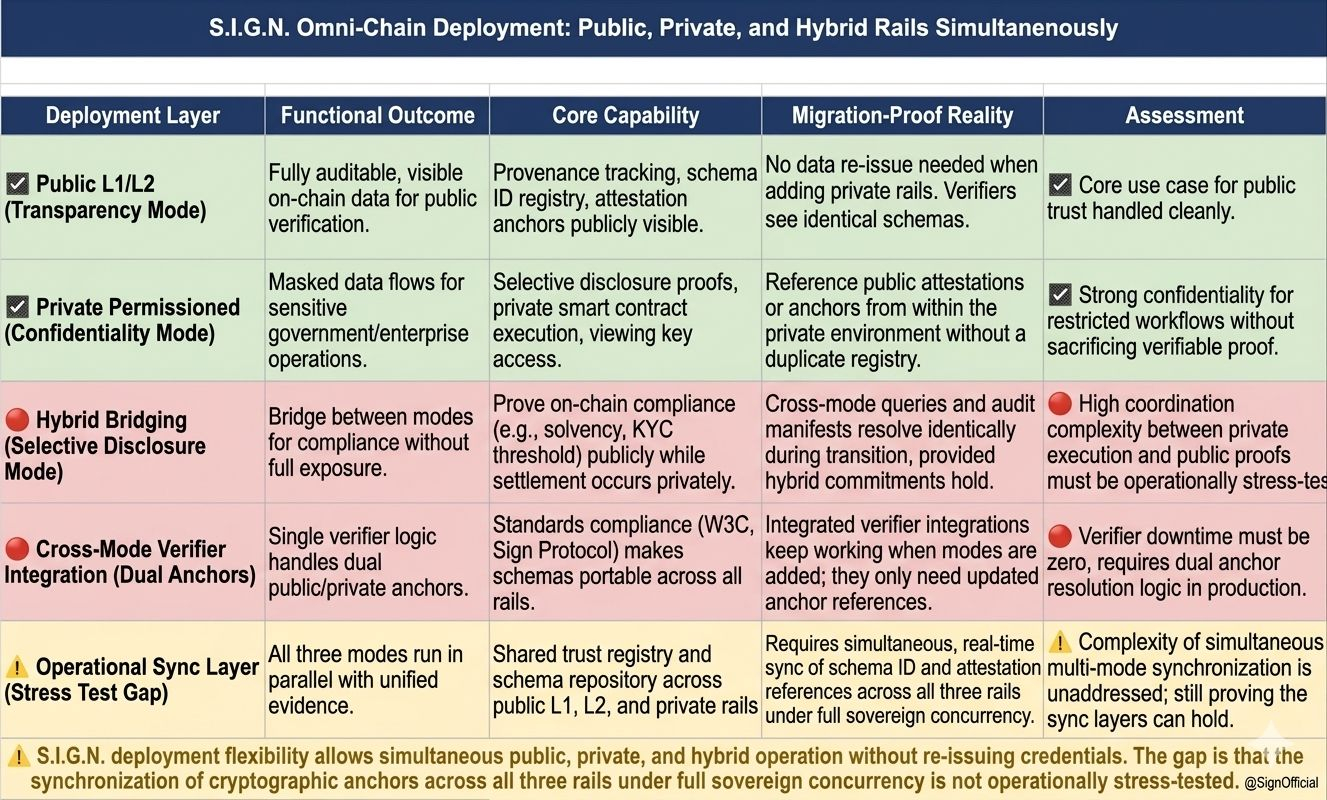
#SignDigitalSovereignInfra @SignOfficial $SIGN
$SIREN $BULLA #TrumpConsidersEndingIranConflict #OpenAIPlansDesktopSuperapp #AnimocaBrandsInvestsinAVAX