What kept bothering me in Midnight was not the private state. It was the maintenance job that starts after a contract is already deployed and everyone thinks the hard part is over.
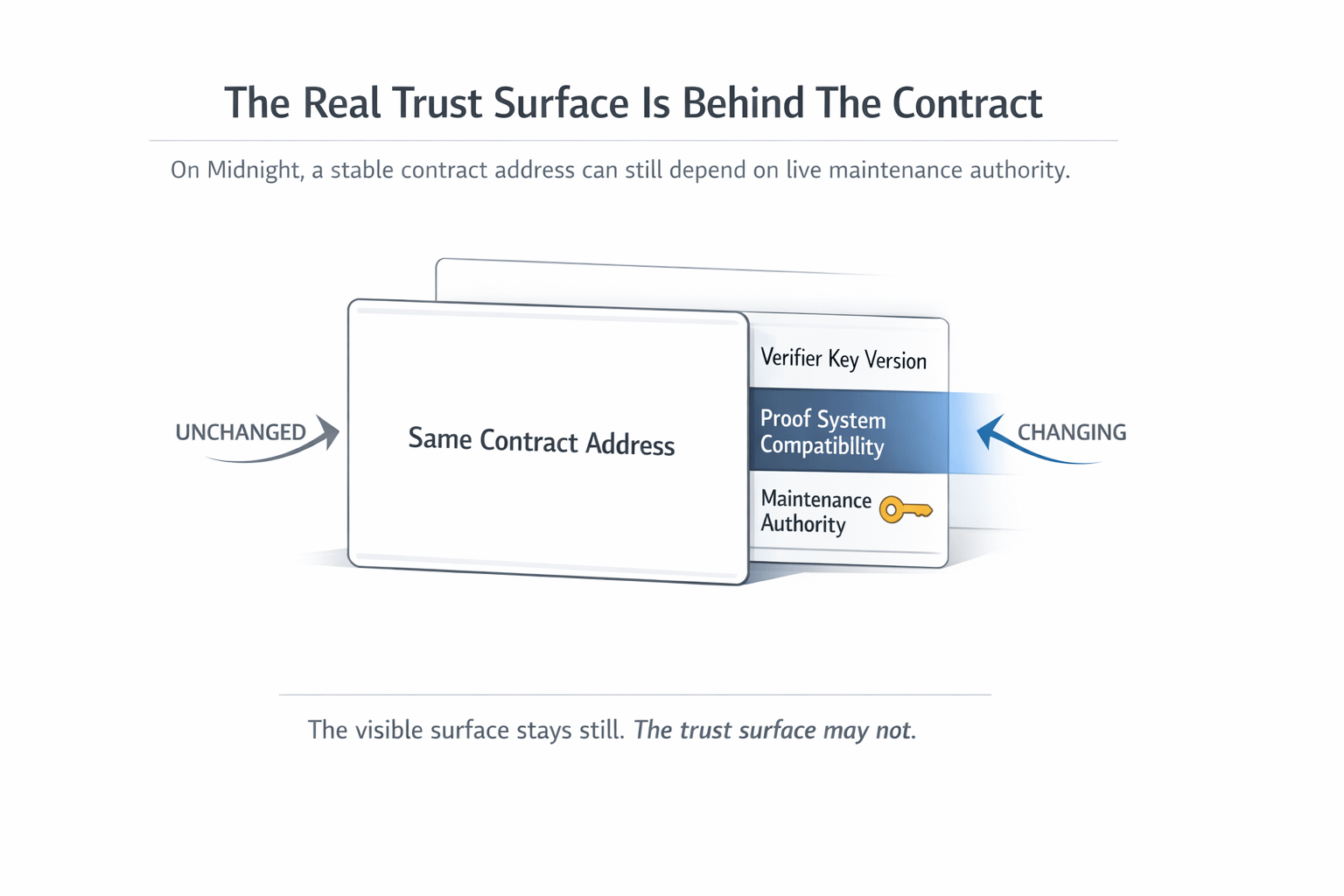
A Midnight app can look settled from the outside. Same contract address. Same user flow. Same interface. But under that surface, the proving system, verifier keys, and runtime compatibility can still move. That means the contract people think they are trusting is not just code frozen in place. It is also whatever authority still has the right to keep that contract valid when the underlying proof environment changes.
That is a very different kind of trust burden.
Midnight's own updatability guide does not treat upgrades like a nice extra. It says breaking proof-system updates can force contracts to update, and that old deployments may lose support after notice. It goes even further than that. Non-upgradable contracts are expected to give users a way to withdraw funds within a week. Upgradable ones are expected to commit to upgrade timelines or at least provide a way out if the upgrade does not happen. That is not the language of optional polish. That is the language of live operational responsibility.
The proof point that really sharpened this for me was the Contract Maintenance Authority.
Midnight lets a deployed contract carry a maintenance authority that can change the authority itself, add a verifier key for a specific verifier key version, or remove one. And the docs are blunt about the most powerful part. If you remove a verifier key and re-add one for that version, you can change the implementation of a circuit. Maintenance updates also take effect immediately right now. So the thing keeping a contract usable across proof-system shifts is also the thing that can materially change how that contract behaves.
That is the hidden mess.
On a lot of chains, users can treat a deployed contract address like the center of trust. On Midnight, that shortcut gets weaker the moment proof compatibility becomes part of the life cycle. The live trust surface is not only the address. It is also the keyholder, the upgrade policy, the response time, and the discipline around verifier-key transitions. Midnight even defines a verifier key version as a combination of proving-system version and onchain runtime version, which tells you how deep this maintenance layer runs.
The visible consequence is simple.
A builder can ship a private app that looks stable to the user while the real continuity risk sits with whoever controls maintenance. If that operator is slow, careless, or opaque, the user does not experience an abstract governance issue. They experience an app that suddenly needs migration, a withdrawal rush, or a contract they can no longer rely on the same way. Midnight's privacy model is interesting, but this is the part that feels harder and more honest to me. Private execution is not the whole trust story when update authority can keep the surface calm while the assumptions underneath it change.

I think this is where Midnight becomes much more real than generic privacy marketing. The network is telling builders, very directly, that private smart contracts live inside an evolving proving environment. So the serious design question is not only how to hide user data. It is how to carry upgrade power without asking users to trust a black box that can quietly redefine the contract they thought they already understood.
That is also why I do not think the important Midnight question is "can this app stay private?" The sharper question is whether builders can make maintenance authority legible enough that users know when a stable contract address still means stable trust, and when it does not. #night $NIGHT @MidnightNetwork
