Most conversations around privacy in crypto still orbit the same surface-level narrative: hide transactions, protect identities, reduce exposure. It’s a framing that made sense early on, but it no longer matches where real demand is emerging.
Because today, the problem isn’t just visibility.
It’s usability under confidentiality.
$NIGHT, through Midnight, approaches this from a fundamentally different angle. It doesn’t treat privacy as a feature bolted onto a chain. It treats it as an execution condition — something that needs to exist natively within how applications run, not as an afterthought layered on top.
That shift is more structural than it sounds.
The core issue is simple but largely unresolved: most blockchain systems force a tradeoff between transparency and practicality. Everything is visible by default, which is great for verification but unusable for any scenario involving sensitive data — financial agreements, identity-linked interactions, enterprise workflows.
So developers are left improvising.
They either avoid blockchain altogether for these use cases or build complex workarounds that compromise either privacy or composability.
NIGHT targets this exact gap.
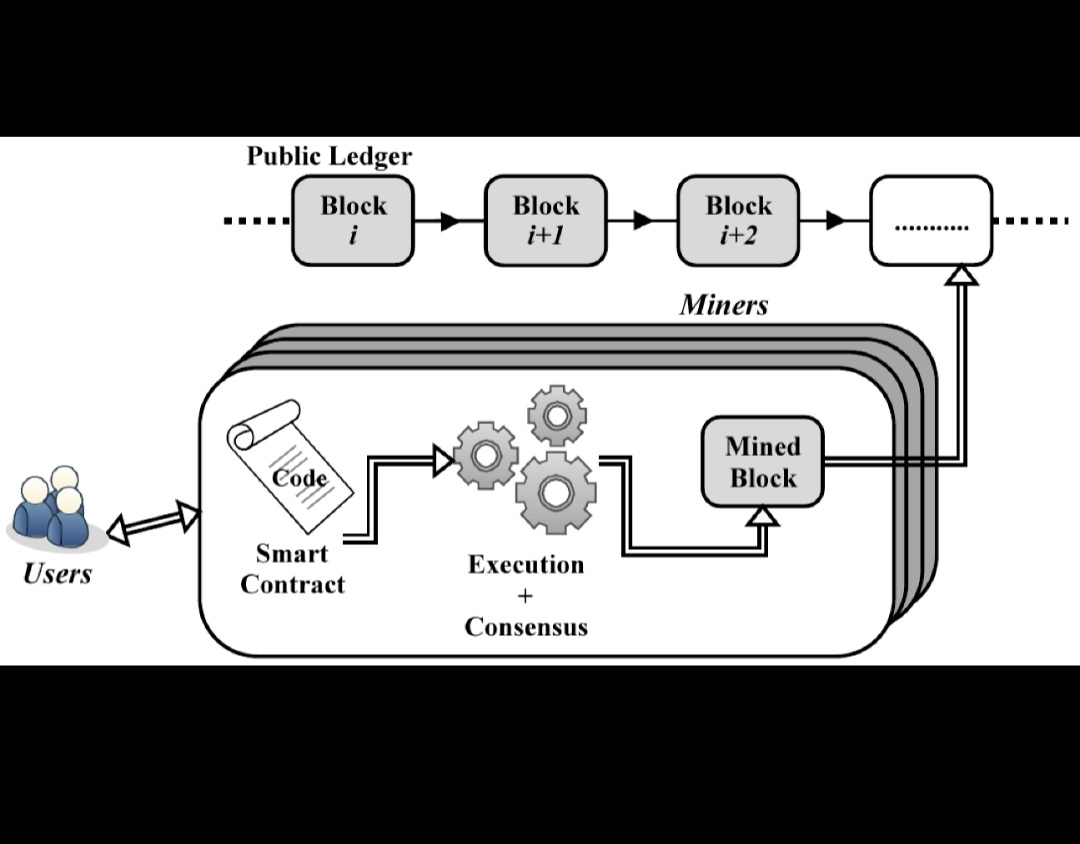
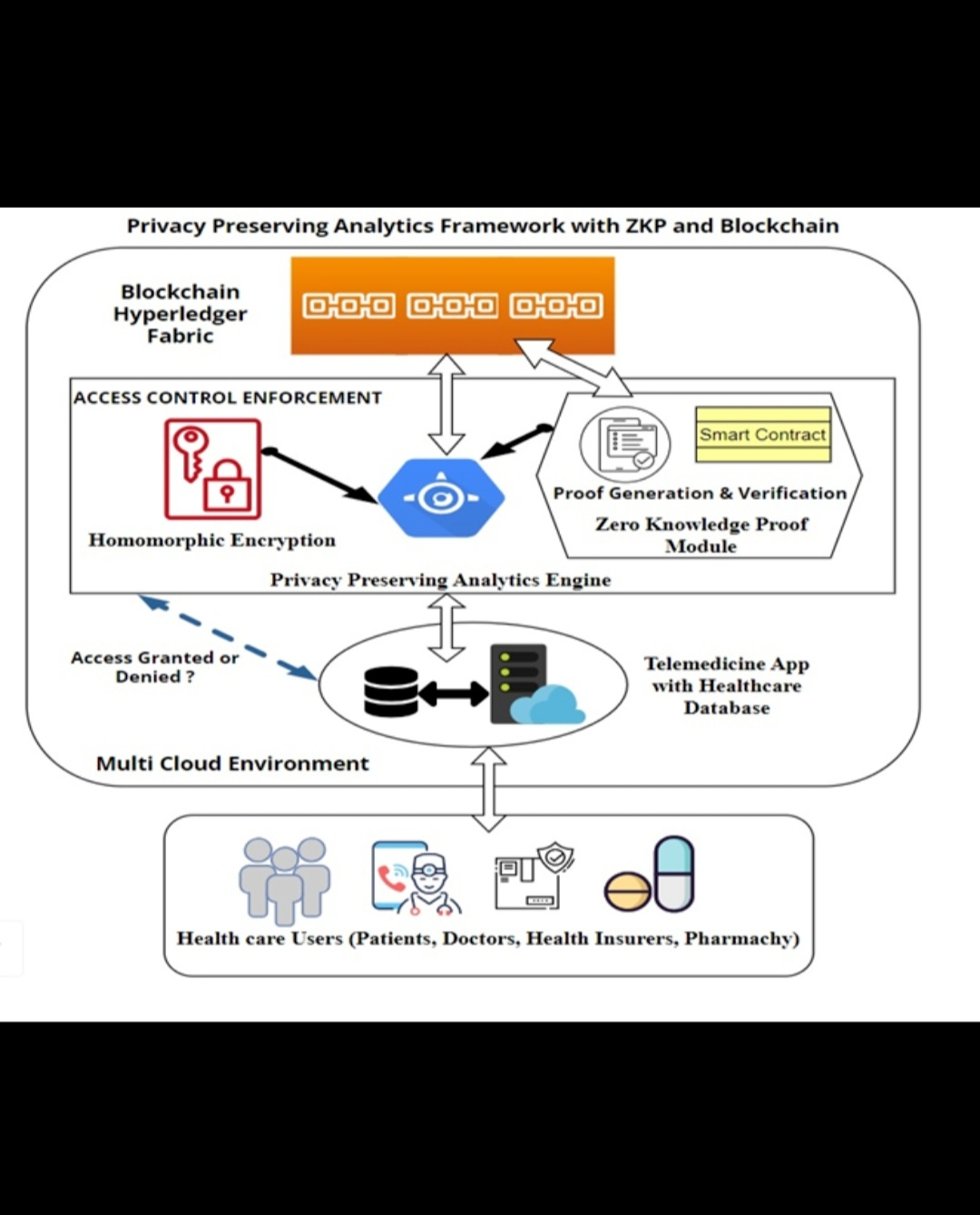
Instead of asking developers to choose between privacy and utility, it introduces a model where confidential smart contracts can execute while still being verifiable. Data remains shielded, but the correctness of execution doesn’t.
That’s the key.
Not hidden systems — but provable systems with selective disclosure.
What makes this design compelling is how it aligns with real-world constraints.
In traditional finance and enterprise environments, confidentiality isn’t optional. It’s a requirement. But so is auditability. Systems need to prove that rules were followed without exposing the underlying data.
This is where Midnight’s approach starts to feel less like a crypto experiment and more like infrastructure design.
By enabling programmable privacy at the contract level, NIGHT effectively opens the door for applications that were previously incompatible with public chains. Think regulated financial products, identity-bound services, or data-sensitive coordination between institutions.
These aren’t niche use cases.
They’re the majority of real economic activity.
There’s also a subtle but important shift in how developers interact with the system.
Instead of building around limitations, they build with primitives designed for confidentiality from the start. That changes development patterns entirely. Privacy stops being a constraint and becomes part of the logic itself.
And that has downstream effects.
Better developer experience leads to more experimentation. More experimentation leads to more applications. And more applications create organic demand — not speculative, but functional.
From a token perspective, this is NIGHT become more than just an asset.
It sits within a system where privacy-preserving execution has a cost, a demand curve, and a usage cycle. If confidential computation becomes a standard requirement for certain classes of applications, then the token is directly tied to enabling that environment.
Not indirectly.
Operationally.
What stands out to me is how this avoids the usual hype traps.
There’s no attempt to position privacy as a buzzword or a narrative spike. Instead, it’s framed as infrastructure — something that either works under real constraints or doesn’t matter at all.
That’s a harder path.
It requires actual adoption, not just attention.
The broader implication is where this becomes interesting.
As regulation tightens and institutions move closer to onchain systems, the need for controlled transparency becomes unavoidable. Fully public systems won’t suffice. Fully private systems won’t either.
The future likely sits in between.
Verifiable, but not exposed.
NIGHT is building directly into that middle ground.
My view is that this positions it ahead of where the market currently is, but aligned with where it’s heading.
Right now, most users don’t feel the urgency of programmable privacy because the applications demanding it haven’t fully materialized onchain yet. But infrastructure tends to be built before the demand becomes obvious.
And when that demand arrives, the systems already capable of handling it don’t need to pivot.
They just scale.
Execution risk still applies, as it always does with infrastructure plays.
Confidential systems are complex. Developer tooling needs to be intuitive. Performance needs to hold under load. And most importantly, real applications need to choose this stack over existing alternatives.
But if those pieces come together, the role of NIGHT becomes clear.
It’s not competing in the attention economy.
It’s anchoring itself in the trust economy.
And in a space where verification is everything, that’s not a small distinction.