I remember a time when I avoided interacting with certain wallets publicly. Not because I didn’t trust the blockchain, but because I knew everything I did could be tracked. Transfers, balances, even patterns all visible.
At the time, I believed transparency was necessary. That’s how blockchains build trust, right?
But after spending more time analyzing on-chain data, I realized something uncomfortable. Transparency doesn’t just build trust it also exposes behavior. And for real-world use cases, that can become a serious limitation.
That experience changed how I evaluate blockchain systems.
Now I ask a different question:
Can privacy exist without breaking trust?
That’s why Midnight Network caught my attention.
Not because of hype or narratives.
But because it raises a deeper question:
Can a blockchain protect sensitive data while still remaining verifiable and compliant?
Most privacy-focused systems either hide everything or expose everything.
Midnight tries something different.
It introduces the idea of rational privacy where data is protected, but still usable and verifiable when needed.
So the real question becomes:
Does this balance actually work in practice?
According to the project documentation, Midnight uses zero-knowledge proofs to enable verification without exposure.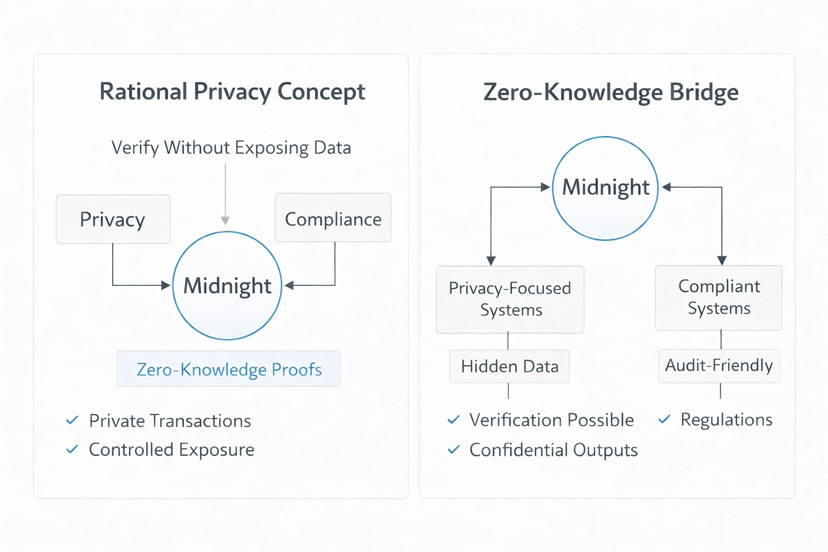
This means the network can confirm that a transaction is valid without revealing the details behind it.
A simple analogy might help.
Think of it like showing a ticket at an event. You prove you have access, but you don’t reveal all your personal information.
That’s what zero-knowledge does for blockchain.
Midnight combines this with its NIGHT and DUST model, where users hold NIGHT to generate DUST, the resource used for transactions.
DUST is also shielded, meaning it doesn’t leave the same metadata trails as traditional systems.
This matters because it allows:
• private transactions
• verifiable outcomes
• controlled data exposure
Instead of choosing between transparency and privacy, Midnight tries to create a system where both can coexist.
The market is starting to notice this approach.
The NIGHT token has a total supply of 24 billion, initially issued on Cardano and mirrored on Midnight. Each token is divisible into one million STARs.
The project also introduced a Glacier Drop distribution model, aiming to spread ownership more broadly rather than concentrating it.
At the same time, there is growing demand for blockchain systems that can handle sensitive data.
Industries like finance, healthcare, and enterprise systems cannot operate on fully transparent ledgers.
This creates a gap.
And Midnight positions itself inside that gap.
But this is where the real test appears.
The biggest challenge isn’t privacy technology.
It’s real-world adoption.
Because privacy only matters if people actually need it and use it.
If developers build applications that require confidential data handling, the system becomes valuable.
But if those applications don’t appear, the technology remains underused.
So the key metric isn’t how private the system is.
It’s whether people use it consistently.
Because if usage stays low, the value of privacy becomes theoretical.
So what would make me more confident?
I’d want to see:
• applications using zero-knowledge for real use cases
• enterprises or developers building privacy-focused tools
• consistent activity that depends on confidential transactions
On the other hand, I’d become cautious if:
• adoption remains limited
• most attention stays around speculation
Because privacy infrastructure only works when it solves real problems.
So if you’re watching Midnight Network, don’t just focus on the technology.
Watch how it’s used.
Because the difference between a privacy concept and a working system is simple:
Do people rely on it when it matters?
@MidnightNetwork #night $NIGHT





