to be honest there was a moment recently when I had to help someone verify a simple document for a cross-border deal. Nothing complicated, just proof of identity and a signed agreement. But what surprised me wasn’t the difficulty, it was the repetition. The same data had to be submitted again and again across different platforms, each one asking for slightly different formats, slightly different checks. It felt less like verification and more like friction disguised as process
That was the moment I started paying closer attention to what projects like @SignOfficial are trying to solve 🤩🤩
$SIGN is not just another blockchain application chasing narratives. At its core, it feels more like an attempt to rebuild how trust is created and reused in a digital environment. Instead of forcing users to prove the same thing multiple times, Sign introduces a system where data can be attested once and then carried across contexts without losing its validity. That idea alone sounds simple, but in practice it touches identity, contracts, credentials, and even how value moves between systems
What stands out to me is how Sign approaches this through a combination of technologies rather than a single solution. The schema-based attestation model creates a shared structure for data, which means different systems can interpret the same information consistently. Once an attestation is created and signed, it becomes something verifiable without relying on trust in the original issuer. Over time, this starts to feel like a reusable layer of truth rather than isolated proofs scattered across platforms.

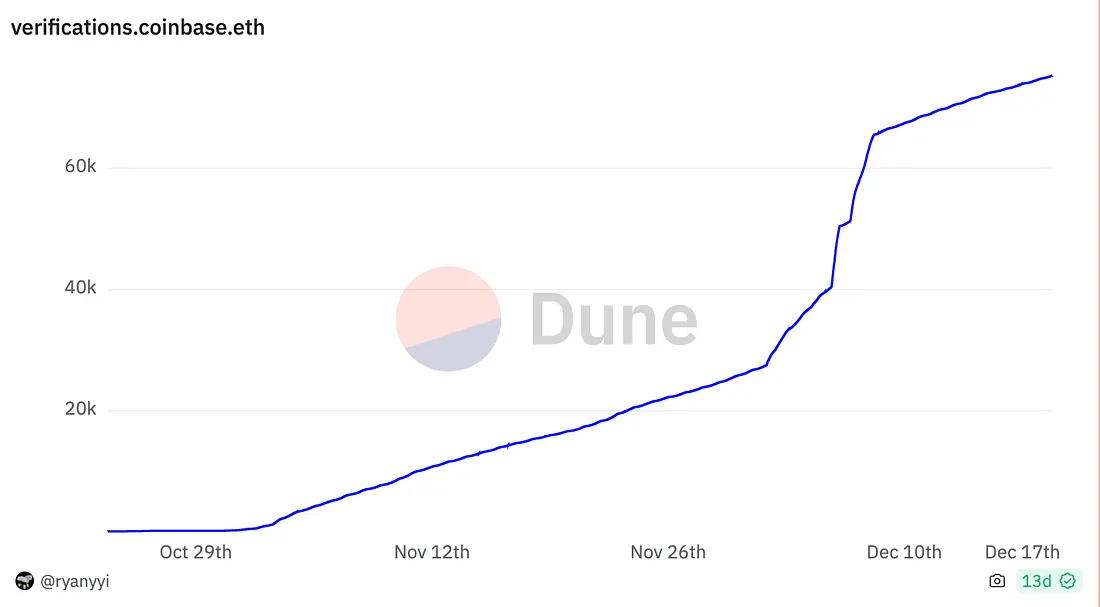
Then there is the multi-chain aspect. Instead of locking everything into one ecosystem, Sign spreads across public chains, private infrastructure, and decentralized storage like Arweave. It is a design choice that suggests they are thinking beyond typical Web3 silos. The addition of zero-knowledge proofs adds another layer, allowing verification without exposing the underlying data. That balance between privacy and transparency feels particularly important if the goal is to work with institutions, not just retail users.
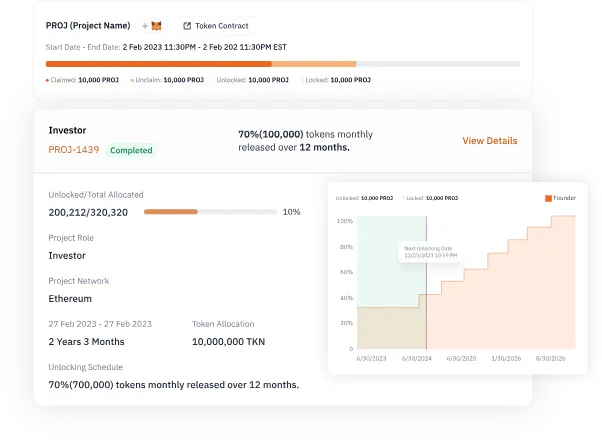
Products like TokenTable and EthSign also show a more practical side of the vision. Token distribution, contract signing, and credential verification are not abstract use cases. They are things people already do every day, just in inefficient and fragmented ways. Sign seems to be positioning itself right in the middle of that gap.
But the more I look into it, the more I feel the challenges are just as important as the vision 🤨🤨
Scalability is probably the first real test. As attestations grow from thousands to millions, the reliance on multiple chains and off-chain storage could introduce latency or complexity that is not obvious at smaller scale. The system works in theory, but real-world usage at scale often exposes bottlenecks that architecture diagrams do not show.
Then there is the developer experience. Even though Sign provides SDKs and tools, bridging Web2 developers into a system that involves schemas, attestations, and cryptographic proofs is not trivial. If the learning curve remains high, adoption could slow down regardless of how strong the underlying technology is.
Security and privacy also remain ongoing concerns. Zero-knowledge proofs are powerful, but they do not eliminate risks from smart contract vulnerabilities or poor key management. In a system built around trust, even small weaknesses can have outsized consequences.
Personally I think $SIGN is moving in the right direction, especially in how it treats trust as something portable rather than disposable. But the real challenge is not building the infrastructure, it is making that infrastructure invisible enough for people to actually use it without thinking. If they can solve that, Sign has a chance to become more than just another protocol. It could quietly become a standard layer that everything else depends on.