By Maheen | Inflectiv
There's a problem nobody is talking about loudly enough.
Every AI agent running right now - on your machine, inside your company's stack, inside ours - has full access to your credentials. Your API keys. Your environment variables. Your AWS keys, your database URLs, the secrets that connect your systems to the world.
This isn't a theoretical vulnerability. In December 2025, researchers found over 30 vulnerabilities across AI coding tools. Agents being hijacked to silently exfiltrate credentials. And the underlying issue in almost every case was the same: there is no standard governing how agent access to secrets actually works. No scoping. No audit trail. No kill switch. The agent inherits your entire shell environment and does whatever it wants with it.
We ran into this problem ourselves.
What 4,600 agents taught us
Inflectiv crossed 4,600 active agents on our platform. Agents that write to datasets, call external APIs, generate intelligence, and feed that intelligence back into the system. At that scale, the credential problem stops being theoretical.
We had agents with access to credentials they didn't need. No way to verify what had been accessed. No consistent way to scope permissions across agents doing different jobs. No mechanism to cut access when a session ended. The audit trail was us, manually checking.
That's when we built what became AVP - the Agent Vault Protocol.
The first version solved our problem. But the more we worked on it, the clearer it became that this wasn't an Inflectiv-specific problem. Every team running agents at any meaningful scale hits this wall, whether they've named it yet or not. Claude Code, Cursor, Codex - they all inherit your full environment by default. Every credential, visible and accessible, with zero visibility into what gets touched and when.
So we published the spec.
What AVP actually defines
AVP is an open standard for how AI agents store, access, and are governed around credentials and environment variables. Four components, working together:
An encrypted vault. Credentials live locally, encrypted at rest using AES-256-GCM with keys derived via scrypt. They never leave the machine. No cloud dependency, no central point of failure.
Profile-based permissions. You define what each agent is allowed to see. Restrictive, moderate, permissive - or fully custom with per-credential rules. An agent running a market data pipeline has no business touching your database credentials. AVP makes that enforceable rather than aspirational. Rules evaluate in order, last match wins, which means you can set broad defaults and layer specific overrides cleanly.
A three-state access model. Every credential is either allowed, denied, or redacted. Redaction is the important one - the agent receives a cryptographic token in place of the real value. It can run without breaking. It cannot exfiltrate what it was never meant to see.
An immutable audit trail. Every access decision is logged before it's enforced. Every credential, every agent, every timestamp. You can query it. You can't delete individual entries. When something goes wrong - and eventually something will - you have a full record.
And one more thing worth naming: a kill switch. One command revokes all active sessions instantly. Every agent, all credential access, cut immediately.
The design principles were non-negotiable: local-first, deny by default, audit everything, simple enough to implement in any language in under 50 lines.
Three commands. Full control.
The reference implementation installs in seconds:
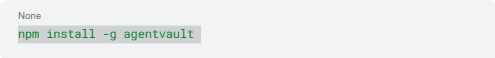
From there:
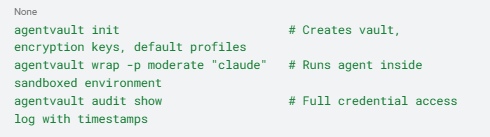
That's the entire surface area for most use cases. The spec goes deeper - trust levels scored 1–100, TTL-based session expiry, runtime metadata injection so agents know their own trust context, and a standard directory structure so any implementation stores data consistently.
Why publish it as an open standard
We could have kept this proprietary. We didn't, for the same reason TCP/IP wasn't owned by one company.
Open protocols create trust. Trust creates adoption. Adoption creates the kind of gravity that no amount of marketing can manufacture. If AVP becomes the way agents handle credentials - across frameworks, across platforms, across companies - then Inflectiv isn't just a marketplace. We're infrastructure. And infrastructure doesn't win by locking people in. It wins by being the thing everyone builds on.
There's also something more immediate: the ecosystem needs this now. HashiCorp Vault is powerful but it wasn't built for AI agents. Manual .env files offer nothing. There is no purpose-built, agent-native, local-first standard for credential governance - until now.
We're not the only team that could have written this spec. But we wrote it because we had to, and we're publishing it because the gap is too dangerous to leave open.
Inflectiv as the first use case
AVP needed a real implementation to prove it works at scale. Ours is it.
4,600+ agents. Production datasets. Credentials that matter. Inflectiv runs on AVP because we needed exactly what it specifies - and running it in production is how we know the spec is honest.
What that unlocks for us is the intelligence layer. Agents with governed, auditable credential access can do something more interesting than just run safely - they can publish what they learn. Structured knowledge packs, bought and sold through our Agentic Data marketplace, transacted autonomously through our MCP server with X402 micropayments.
The vault protects credentials. It also protects intelligence. And intelligence compounds in a way raw credentials never will.
The spec is live
AVP v1.0 is published. The reference implementation is on GitHub. MIT licensed. An enterprise tier - SSO, team management, compliance reporting - is on the roadmap.
If you're building agents and you have a credential problem - or you're about to - we'd like to hear from you. If you want to implement AVP in your own framework, the spec is everything you need. If you find gaps, open an issue.
The agent economy is coming whether the tooling is ready or not. We'd rather it arrived with a security standard in place.
Maheen writes about infrastructure, data, and the practical side of building for the agentic economy at Inflectiv.
Find the AVP spec and reference implementation at agentvault.up.railway.app