There’s a quiet inefficiency baked into crypto that most people ignore.
We’ve built systems that can move billions in seconds, settle globally, and execute complex logic without intermediaries. But the moment something needs to be verified beyond a wallet balance, everything falls apart.
Identity moves offchain.
Credentials sit in closed systems.
Reputation resets every time you switch platforms.
So despite all the progress, one thing hasn’t changed:
Trust is still fragmented.
That’s the gap SIGN stepping into — not as a feature, but as infrastructure.
The Hidden Friction No One Talks About
Every application that needs verification today ends up rebuilding the same logic.
Who is this user
Can this entity be trusted
Is this claim valid
And each time, the answer lives somewhere else — an API, a database, a centralized provider.
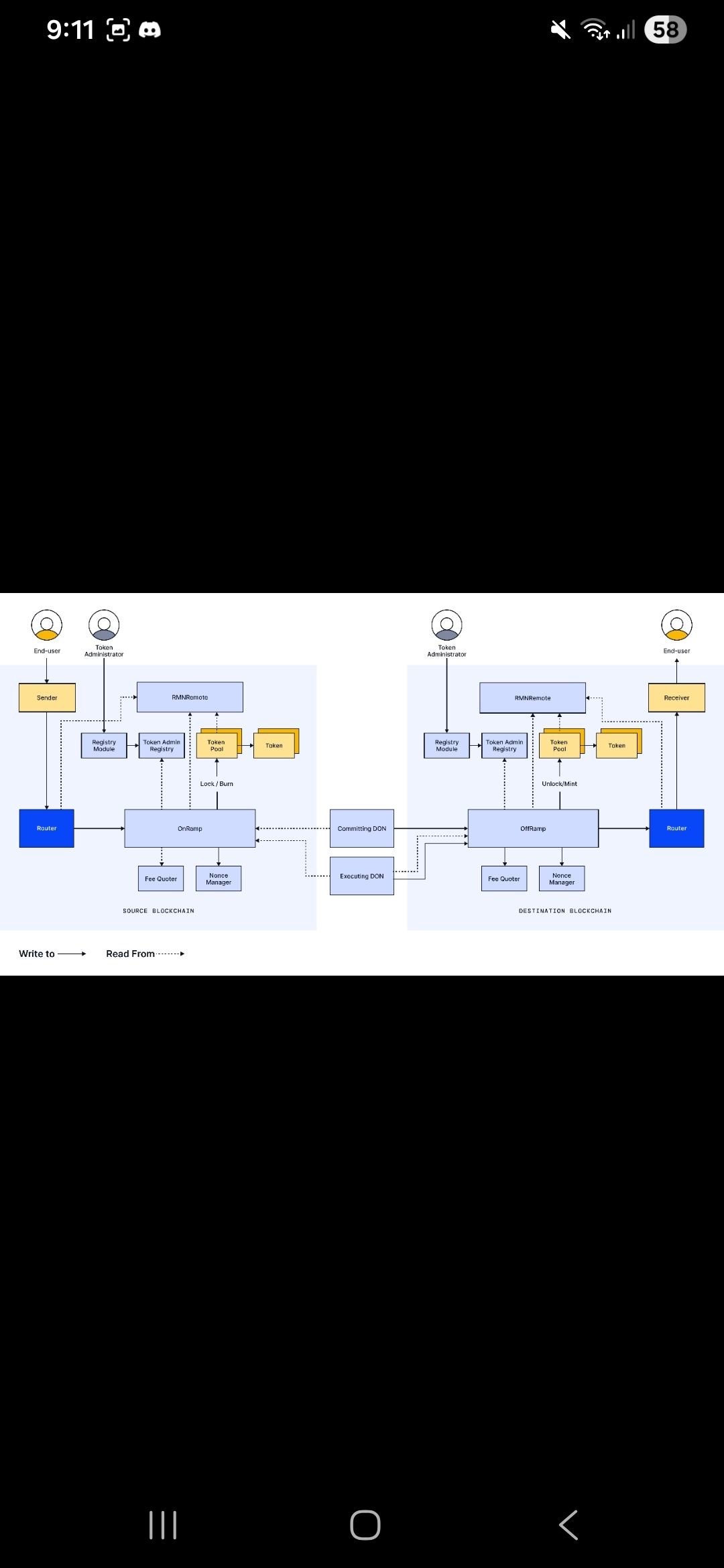
Which means verification isn’t composable.
It doesn’t travel.
It doesn’t integrate natively with smart contracts.
So instead of trust compounding across systems, it resets.
Again. And again.
SIGN Changes the Unit of Trust
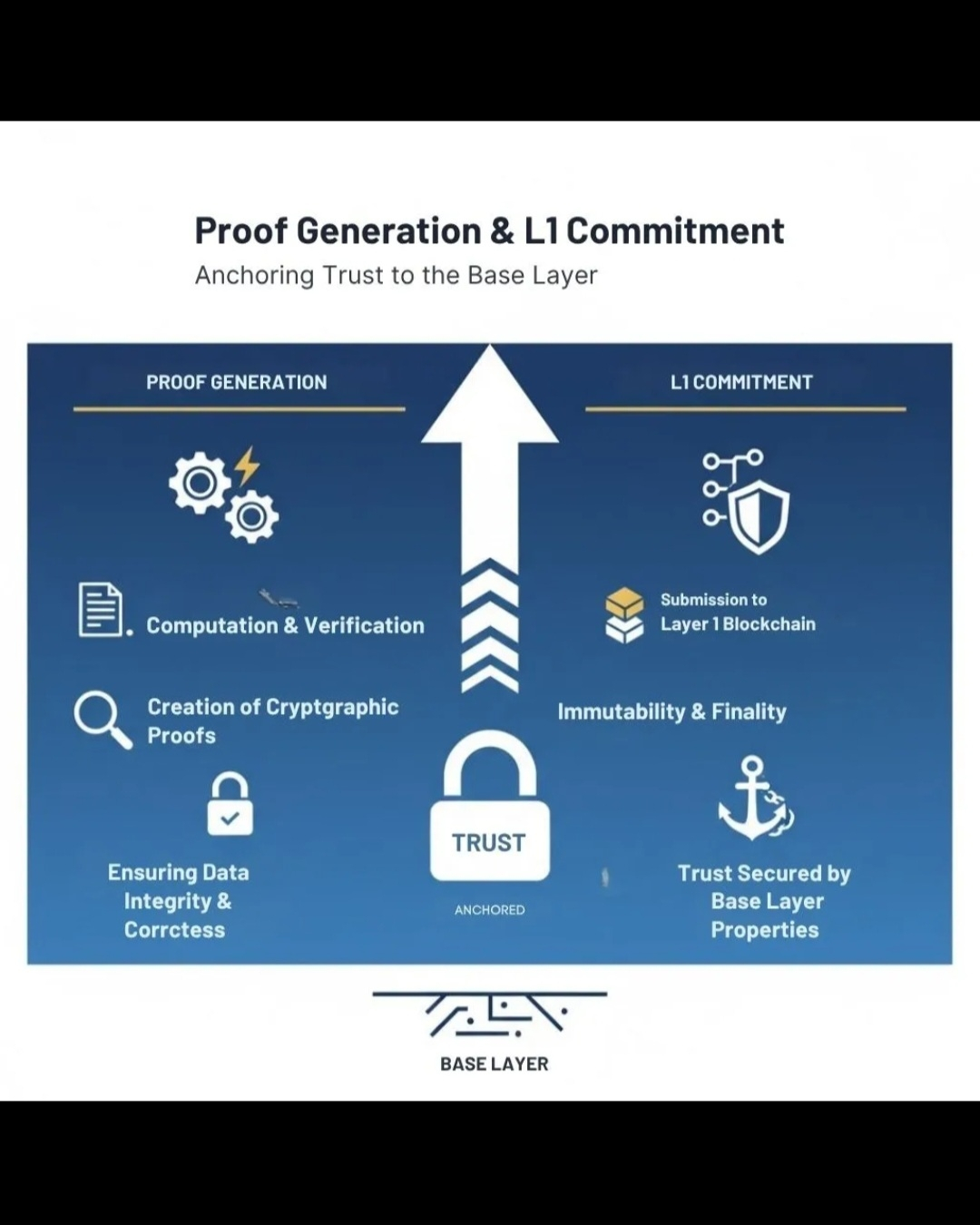
What SIGN introduces is simple in concept, but structural in impact:
Attestations as a primitive.
Not documents.
Not approvals.
Not platform-bound credentials.
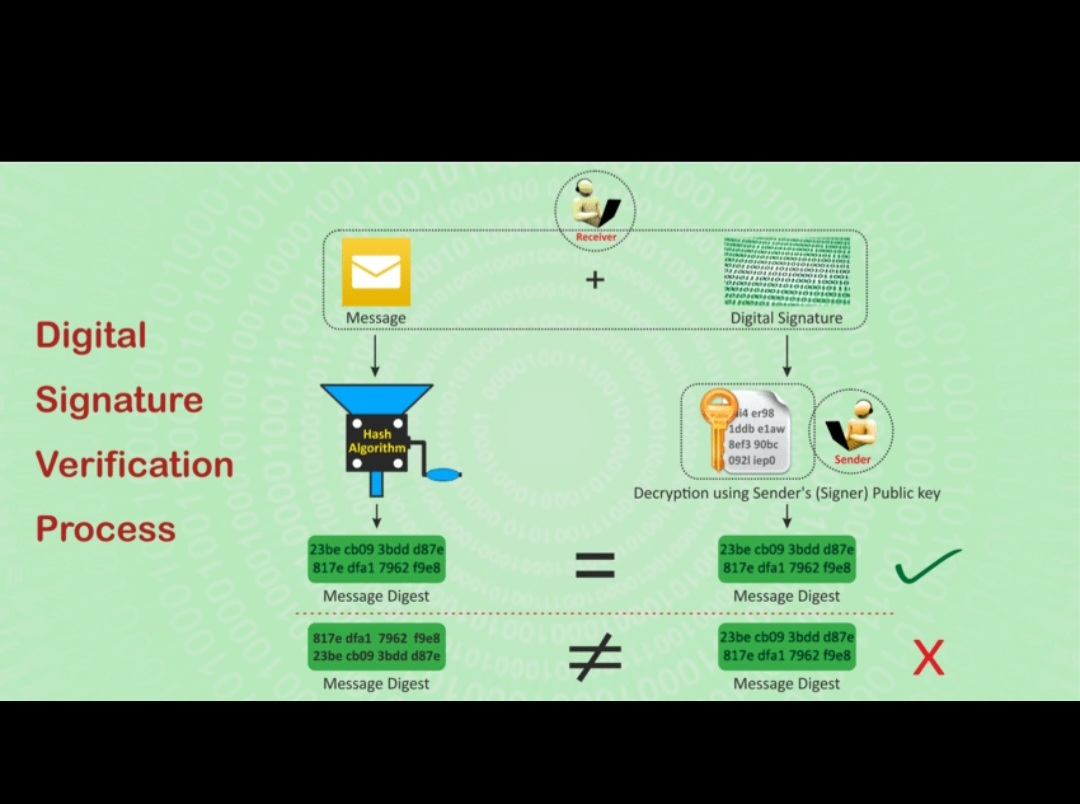
But cryptographic proofs that can exist onchain, be verified anywhere, and reused across contexts without re-issuance.
This flips the model entirely.
From:
> Verify → store → isolate
To:
> Verify → attest → reuse
And once verification becomes reusable, it stops being a bottleneck.
It becomes infrastructure.
Why This Unlocks a Different Class of Applications
When trust becomes portable, systems stop depending on isolated checks.
They start composing.
DeFi can integrate identity without holding user data.
DAOs can gate access using verifiable credentials instead of manual curation.
Marketplaces can rely on reputation that isn’t trapped inside their own platform.
This isn’t just efficiency.
It’s a shift from closed trust systems → open verification networks.
And that changes how applications are designed at a fundamental level.
The Architecture Signal Most People Miss
SIGN isn’t trying to own identity.
That’s where most projects fail.
Instead, it focuses on making verification interoperable, which is a much stronger position.
Because identity will always be fragmented.
Different providers, different standards, different jurisdictions.
But if verification becomes a shared layer,
those fragments can finally connect.
That’s the real unlock.
Not control over identity —
but usability of it.
Where This Is Heading
The next phase of onchain systems isn’t about faster execution.
It’s about integrating real-world signals into programmable environments.
And that requires a shift:
From storing data
→ to proving it
From trusting entities
→ to verifying claims
SIGN sits exactly in that transition.
Not at the surface level,
but at the layer where systems decide what to trust.
The Part That Actually Matters
Most narratives come and go.
But infrastructure tends to follow a different path.
It starts invisible.
It looks optional.
And then suddenly, it becomes required.
SIGN feels early in that curve.
Because once applications start depending on portable verification,
you don’t go back to isolated trust systems.
You can’t.
Final Thought
$SIGN isn’t making verification more convenient.
It’s making it native to how systems interact.
And once trust becomes something that can move,
compose,
and scale alongside code,
you’re no longer just building applications.
You’re building systems that can actually understand what’s real.