i’ll be honest — i didn’t take Sign seriously at first. not because the idea is bad, but because “digital identity + government rails” has been pitched a thousand different ways in crypto. most of them end up as dashboards, partnerships, and a token that people trade… while the real world keeps running on paper forms and PDF stamps.
what changed for me is the angle.
Sign isn’t trying to win attention by being loud. it’s trying to make trust behave like infrastructure — the kind that sits underneath everything and quietly keeps systems moving.
and i think the most underrated part isn’t “credentials” by itself.
it’s cross-chain identity that doesn’t break.
the real problem isn’t moving proofs — it’s keeping them meaningful
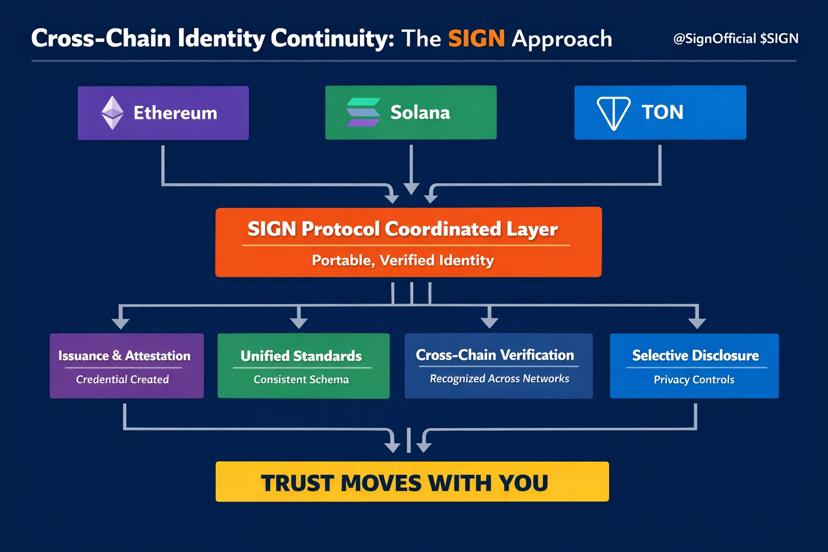
at first i thought interoperability was just plumbing. bridge this. sync that. move a credential from Ethereum to Solana to TON and done.
but the more i think about it, the less i believe transport is the hard part.
recognition is.
if i earn a credential on one chain — event attendance, KYC status, contributor role, business approval — the point isn’t the chain. the point is the claim. and that claim should still mean something when the rails change.
otherwise we’re just recreating the same broken internet pattern:
new app → start from zero → re-verify → re-earn trust → repeat forever.
that’s not “Web3.” that’s a fragmented identity nightmare.
i keep coming back to this: trust needs continuity
imagine i prove i attended a conference on Ethereum. later a Solana app wants to gate access. or a TON community wants to verify i’m legit. in today’s world, i end up doing the same dumb loop: screenshots, links, manual checks, “trust me bro.”
SIGN’s direction (at least from how i’m reading it) is trying to make this smoother:
• a claim gets structured
• it gets attested by an issuer people recognize
• it becomes verifiable evidence, not a vibe
• and other systems can check it without rebuilding the whole verification stack
that’s not just convenience. it’s identity staying intact while everything else evolves.
and if you zoom out, that’s exactly what governments and big institutions care about. not hype. not tokens. continuity.
why “sovereign” isn’t just a buzzword here
when people say “sovereign digital infrastructure,” i think most retail reads it like marketing. but the practical meaning is simple:
governments don’t want identity and money rails that depend on one foreign platform, one company’s database, or one chain’s survival.
they want systems where:
• credentials can be verified
• data exposure can be controlled
• rules can be audited
• and the stack doesn’t collapse when networks rotate or politics shift
that’s why selective disclosure matters too. because “everything public” is not how real states operate. they need proof, but they don’t want to leak everything.
so when @SignOfficial talks about verifiable credentials + programmable distribution + privacy-aware verification, that’s the first time i feel like the pitch is aimed at real-world constraints instead of crypto fantasy.
the hard truth: standards decide everything
here’s where i’m still cautious.
cross-chain trust only works if enough people agree on what a credential means. not just how it’s stored.
because the biggest risk isn’t that chains can’t connect. the risk is that identity gets flattened into meaningless badges that every app interprets differently.
that’s the “lowest common denominator” trap.
so for me, the real milestone isn’t more chains supported.
it’s seeing shared interpretation become normal:
• the same schema
• the same issuer assumptions
• the same verification logic
• the same revocation rules
• the same proof durability across ecosystems
when that happens, you don’t just move credentials.
you move trust.
my take
i’m watching Sign because it’s chasing a very specific thing most projects ignore:
making trust portable without making people re-prove themselves every time the rails change.
if they pull that off, $SIGN stops being “another token.” it becomes the coordination glue for identity + access + distribution across systems that don’t naturally trust each other.
and that’s the kind of infrastructure that gets adopted quietly… then suddenly becomes hard to replace.