I’ll be honest—there was a time I thought “credentials” in Web3 were just decorative. Nice to have, easy to mint, but rarely essential. I treated them like badges you collect and forget. The kind of thing that looks meaningful on a dashboard but doesn’t really change how systems behave underneath.
That assumption started to break for me in small, almost unnoticeable ways. I’d move between apps and realize nothing carried over. A reputation built in one place meant nothing in another. A verification done once had to be repeated again somewhere else, often with more data exposed each time. It wasn’t a technical failure. It was something quieter—there was no shared structure behind what these credentials actually meant.
That’s when it clicked for me: the problem isn’t issuing credentials. It’s making them usable beyond the moment they’re created.
Most systems today treat credentials as isolated outputs. They exist, but they don’t travel well. And when they do, they often require full visibility to be trusted. You either reveal everything and get accepted, or you reveal nothing and get ignored. There’s no clean middle ground.
This is the gap where SIGN started to make sense to me—not as a solution I immediately believed in, but as a different way of framing the problem. Instead of focusing on identity as a whole, it narrows down to something more practical: how to structure and verify individual claims in a way that others can understand and trust without needing full access.
At its core, SIGN works with schemas and attestations. A schema defines the format of a claim—what’s being said and how it should be interpreted. An attestation is the actual statement issued under that structure. The interesting part is how verification happens. Through zero-knowledge proofs, the system allows someone to prove a claim is valid without exposing all the underlying data.
The simplest way I’ve been able to think about it is this: it’s like proving you’re over 18 without showing your entire ID card. The verifier gets what they need, nothing more. That small shift changes the nature of the interaction.
What I find more important, though, is not the cryptography itself but the discipline it introduces. It forces systems to think carefully about what actually needs to be proven. Not everything has to be visible to be trusted, and not every interaction needs to leak context.
Still, I don’t think this approach is free from friction. Standardization only works if multiple parties agree to follow it, and that’s never guaranteed. If different platforms define their own schemas without coordination, the portability advantage weakens quickly. It becomes another fragmented layer instead of a shared one.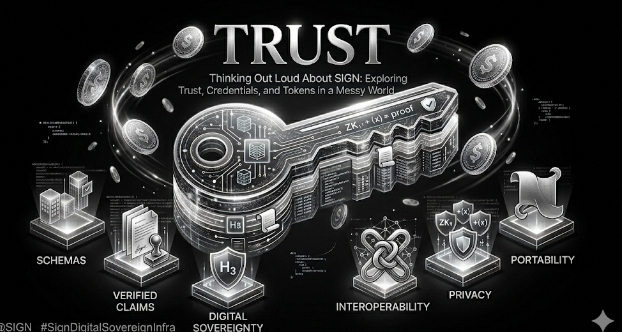
There’s also a real question around developer priorities. Building with structured attestations and zero-knowledge proofs requires more effort than simpler alternatives. Unless there’s clear user demand—or a strong reason to care about privacy at this level—many teams might choose convenience over precision.
And then there’s the user side, which is often overlooked. Most users don’t actively think about credentials. They think about access, outcomes, and speed. If verification becomes even slightly slower or more complex, the benefits need to be very clear, otherwise they’ll default to whatever feels easiest.
So when I look at SIGN now, I don’t see it as something to judge by attention or short-term traction. I look for quieter signals. Are developers actually reusing schemas across different applications? Are attestations being recognized outside their original context? Do users interact with these proofs without needing to understand how they work?
Because in the end, the real test isn’t whether the system can issue credentials. It’s whether those credentials start to matter in places they weren’t originally created for.
I’m still figuring out where this goes. But I’ve stopped thinking of credentials as decorative. If anything, they’re becoming a kind of infrastructure—one that only becomes visible when it fails.
And right now, most of it still does.
@SignOfficial #SignDigitalSovereignInfra $SIGN
