the hardest part of building cross-border digital infrastructure isn’t the technology. it’s the fact that every country has a different answer to the question “what counts as verified.”
and that problem sits right in the middle of the $SIGN thesis.
@SignOfficial built a schema registry that lets governments define their own credential structures. what a resident credential looks like. what fields a professional license requires. what threshold counts as KYC verified. the design is sovereign by default. each government publishes their own schema, accredits their own issuers, controls their own trust registry.
that’s exactly right for a single country deployment.
but the Middle East opportunity isn’t single country. it’s the GCC corridor. cross-border settlement. regional identity portability. a UAE credential being accepted in Saudi Arabia. a Qatari business license verifiable across member states. that’s the actual prize and that’s where the schema question gets complicated.
$SIGN #SignDigitalSovereignInfra 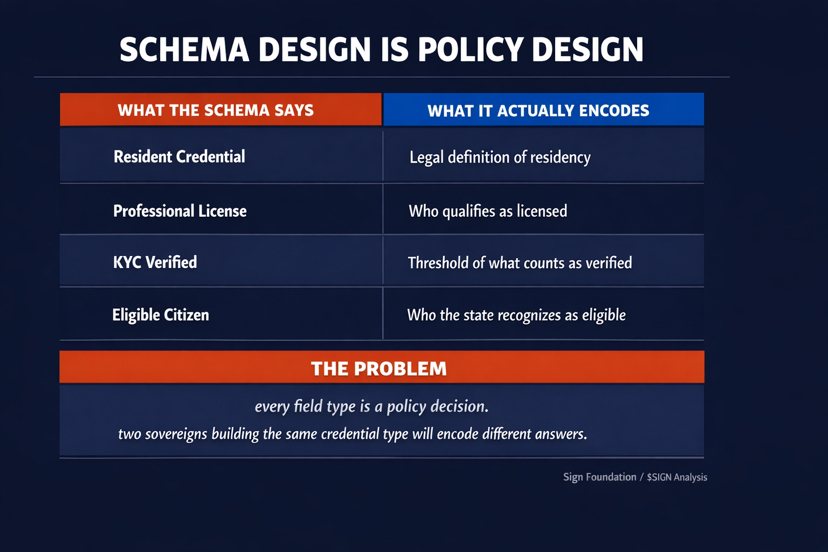
schemas are not neutral documents. they are policy decisions encoded in field types.
a UAE residency schema with twelve fields reflects UAE’s legal definition of residency. a Saudi trust registry expecting nine of those fields reflects Saudi Arabia’s definition. both are technically correct within their own sovereign deployment. both are built on W3C Verifiable Credentials. both use the same cryptographic primitives.
they still don’t interoperate. not because anything failed. because two governments made different policy decisions about what identity means.
the protocol layer cannot resolve that. it enforces schema compliance. it cannot determine which schema should govern when a UAE citizen presents a credential to a Saudi verifier.
that’s a treaty question dressed up as a technical one.
what @SignOfficial gets right is the foundation. W3C Verifiable Credentials, W3C DIDs, standard signature algorithms, selective disclosure, ZK proof support. building on open standards instead of proprietary formats means the technical substrate can support cross-border verification without requiring a single controlling authority. that’s the correct architectural choice for a region where no single government will accept another’s platform as the root of trust.
but open standards don’t resolve schema governance across sovereigns. two countries can implement W3C VC correctly and still produce credentials that don’t interoperate because they encoded different answers to the same policy questions.
the GCC has spent decades trying to harmonize regulatory frameworks across member states. some of it worked. most of it is still being negotiated. digital credential schema alignment is exactly the same problem with a cryptographic layer on top.
#SignDigitalSovereignInfra $SIGN

honestly the more i sit with this the more i think the schema registry is the right infrastructure for the first phase of sovereign deployment. single country. clean internal credential stack. auditable. privacy-preserving. sovereign.
the cross-border phase is a different conversation. and it doesn’t start with code. it starts with two finance ministers agreeing on what a verified identity actually means.
@SignOfficial built the rails. whether the Middle East uses them across borders depends on whether the politics catch up to the protocol.
a shared technical foundation that makes regional interoperability possible once political alignment exists, or a sovereignty-first design that defers the hardest questions to the diplomats?