Credentials are just promises with better paperwork. A diploma says you finished something. A badge says you’re allowed past a door. A token—whether it’s tucked into an API request header or sitting in a wallet app—says a system should treat you differently for a moment. The tricky part isn’t making those promises. It’s keeping them legible and honest after the first burst of certainty, when people change jobs, keys get rotated, phones get replaced, and yesterday’s “valid” quietly becomes today’s “maybe.”
SIGN’s latest upgrade is mostly about that unglamorous stretch of time.
If you watch how credentials fail in real settings, it’s rarely dramatic. It’s small. A QR code that won’t scan because it’s too dense for the cheap camera on a guard’s aging Android. A verification link that loads slowly on venue Wi‑Fi and gets waved through anyway. A token that grants access long after it should because revocation is technically possible but operationally messy. The gap is usually not cryptography; it’s the backbone: identifiers that don’t line up across systems, status checks that aren’t reliable, and logs that tell you what happened only after you already needed to know.
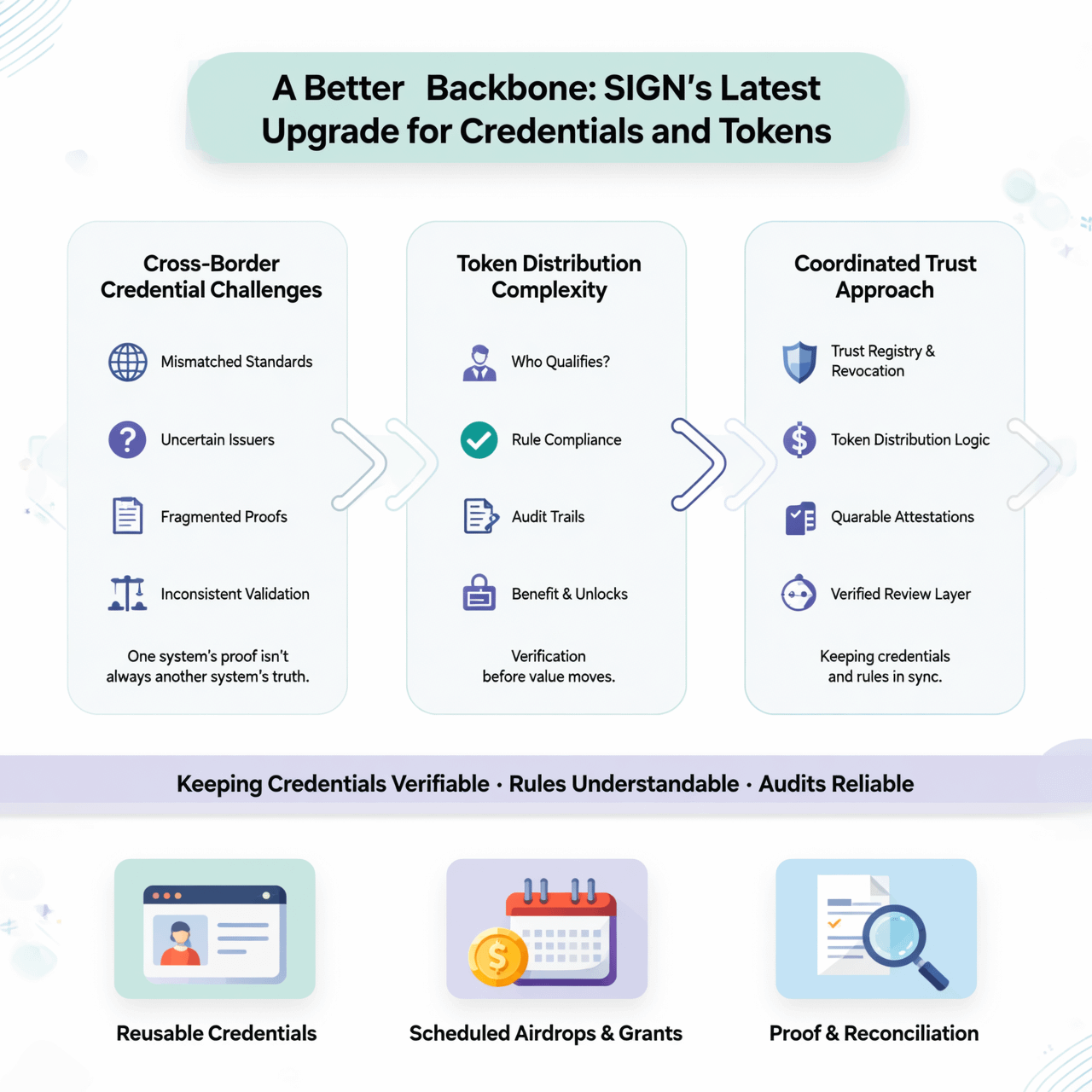
SIGN has been living in that gap, sitting between issuers—schools, employers, event organizers, software platforms—and verifiers who need an answer in seconds, not a lecture. The upgrade doesn’t change what a credential is in the abstract. It changes how the pieces are stored, referenced, refreshed, and proven so that the credential behaves like something you can maintain, not just mint.
One of the most noticeable shifts is an insistence on stable structure. That’s fine until it isn’t. Add one field and an old parser breaks. Move a claim from public to private and downstream systems panic. The new SIGN backbone treats credentials more like versioned documents than one-off artifacts. Schemas are pinned. Fields are typed. The system keeps track of what “version” of a credential format you’re looking at, not as trivia, but as a way to prevent silent misreads.
People verify them months later for internships and visas. Over time, the registrar updates naming conventions, adds a new honors field, changes how course codes are represented. Without strict structure, you either freeze your format forever or accept that verifiers will interpret the same credential differently depending on when they integrated. With structure, the issuer can evolve without breaking the past, and the verifier can choose: support older versions explicitly, or refuse them clearly and explain why.
Tokens complicate things because they live on shorter clocks. A credential might be meant to last for years; a token might be meant to last for minutes. Yet in real systems they blur. A long-lived credential is often used to fetch a short-lived token. A token sometimes gets treated like a credential because it’s convenient: it already exists, it’s already signed, it already travels easily. The result is a mess of implied meaning. People wind up using a bearer token as proof of identity when it was only meant to prove a session. They forward it in a screenshot. They paste it into the wrong place. And when it leaks, it behaves exactly like cash.
SIGN’s upgrade tightens the relationship between credentials and tokens without pretending they’re the same thing. It becomes easier to bind a token to a particular proof event—this device, this key, this request—so it can’t be replayed somewhere else as easily. It becomes easier, too, to limit what a token reveals, so a verifier gets the answer they need (“over 18,” “employee,” “ticket valid for Friday”) without swallowing an entire identity record. The work here isn’t philosophical. It’s payload sizes, signature formats, how many round trips a verifier needs before it can decide, and what happens when the network drops mid-check.
Revocation is where a backbone earns its keep, and it’s where most credential talk gets painfully real. In a demo, everything is valid. In life, people leave organizations, licenses expire, and mistakes get issued. Revocation is also political: someone has to be allowed to revoke, and someone has to be accountable when it happens. SIGN’s newer design makes revocation less like yanking a file from a shared folder and more like maintaining a status record that can be checked quickly and cached safely. A verifier at a door or an API gateway doesn’t have time to do archaeology. It needs a fast yes or no, plus enough context to log the decision without logging sensitive data.
That last part—what you log—ends up shaping behavior. When logs are too thin, fraud investigations become guesswork. When logs are too rich, you create a shadow surveillance system by accident. A better backbone threads that needle with intention: record the fact that a verification occurred, what was asked, what was answered, which issuer signed it, which version of the schema was used. Avoid recording the whole credential when you don’t need it. Store fingerprints and references that can be audited later without turning every routine check into a permanent dossier.
There are tradeoffs in every choice. Make verification fully offline and you risk accepting a credential that should have been revoked an hour ago. Force online status checks for everything and you hand attackers a denial-of-service lever and make honest verifiers dependent on connectivity they don’t control. SIGN’s upgrade doesn’t erase those tensions; it makes them explicit, so an issuer can decide what kind of failure they can live with. A concert venue might accept a small window of revocation lag if it means the line keeps moving. A financial platform probably won’t.
What’s easy to miss, if you only look at features, is how much of this is about reducing improvisation. In older setups, when something went wrong, a human would step in. They’d compare screenshots, read timestamps, ask someone to refresh an app, call a manager. Those interventions keep the world running, but they also create soft spots where policy becomes mood and trust becomes familiarity. A stronger backbone doesn’t replace human judgment; it saves it for the cases that actually require it.
The clearest sign of a mature credential system is not that it can issue impressive proofs. It’s that it behaves predictably under boring pressure: Monday mornings, crowded entrances, expired memberships, rotated keys, half-updated clients, and someone on the other side of the counter who just needs an answer they can stand behind. SIGN’s latest upgrade reads like it was built with those scenes in mind. Not as a pitch, but as a concession to reality: trust isn’t a single signature. It’s the maintenance schedule behind it.
