My dad called me last week. He had seen something about Midnight Network and wanted to know what I was looking at in crypto these days. I thought this would be easy. I explain crypto things to him all the time. Five minutes later I was the one learning. His first question caught me off guard. “Why two tokens? Isn't one enough for a blockchain?” When my dad asked that, I thought the answer would be simple. It turned out that question revealed a design problem most blockchains still haven't solved.
The Problem Midnight Is Trying to Solve Most blockchains use a single token for everything. For example, on Ethereum you use ETH both as an economic asset and as the fuel that powers transactions on the network. The same is largely true for Cardano. At first this sounds simple. One token. One system. But it creates a strange economic problem. The asset people hold for long-term value is also the asset they must constantly spend just to use the network. Fahmi Syed from the Midnight Foundation explained it with an analogy that finally clicked for me. Owning shares in a company is different from paying for the service that company provides. You might own stock in a phone manufacturer, but you don’t pay your phone bill using those shares. Your shares represent ownership. Your phone plan is simply the service you consume. On many blockchains those two things are combined into the same token. When network activity increases and the token price rises, transaction costs rise with it. You end up spending part of the asset you’re trying to hold.
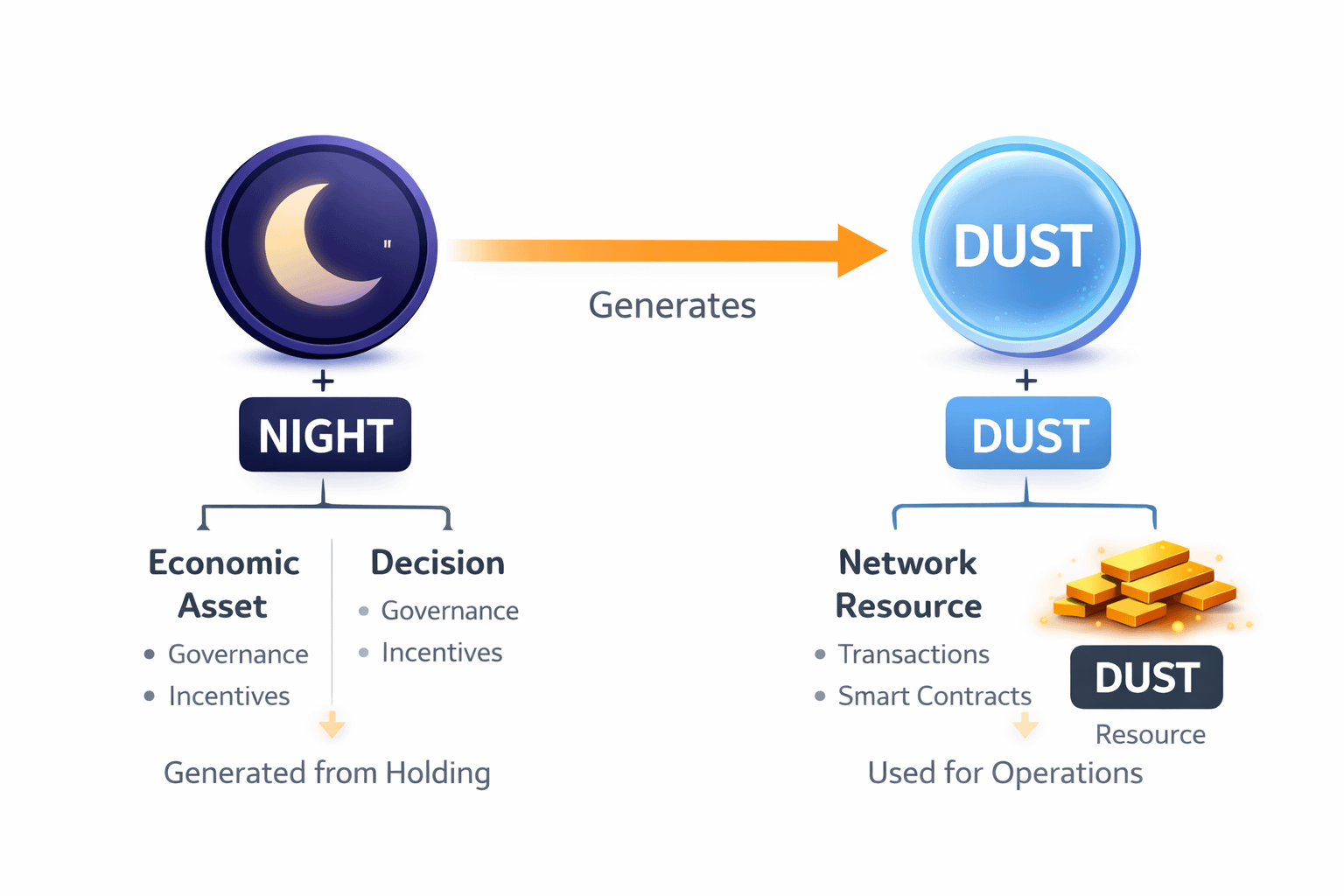 Why Midnight Uses Two Tokens | Midnight separates those two functions. The network has two distinct economic components. NIGHT is the primary economic and governance token of the ecosystem. It represents long-term participation in the network and plays a role in governance and incentives. DUST, on the other hand, functions differently. DUST behaves more like a network resource generated from holding NIGHT. In effect, the system converts capital into renewable execution capacity, reducing the volatility that fee markets often experience on single-token blockchains. It is used to execute transactions and smart-contract operations.
Why Midnight Uses Two Tokens | Midnight separates those two functions. The network has two distinct economic components. NIGHT is the primary economic and governance token of the ecosystem. It represents long-term participation in the network and plays a role in governance and incentives. DUST, on the other hand, functions differently. DUST behaves more like a network resource generated from holding NIGHT. In effect, the system converts capital into renewable execution capacity, reducing the volatility that fee markets often experience on single-token blockchains. It is used to execute transactions and smart-contract operations.
DUST is non-transferable and has a limited lifespan. If it is not used within a certain period, it decays. This design prevents speculation on transaction resources and discourages hoarding. The idea is to separate long-term economic participation from day-to-day network usage. When I explained it this way, my dad nodded. Then he asked something that sounded simple but turned out to be the hardest question of the conversation.
“If Everything Is Private… How Does Anyone Verify Anything?”
He asked something I think many people wonder but rarely say out loud. “If everything is private on this network… how does anyone verify anything?” That question forced me to look deeper.
How Midnight Handles Privacy | Midnight uses cryptographic techniques known as zero-knowledge proofs. The concept sounds complex, but the basic idea is surprisingly simple. You can prove that something is true without revealing the information behind it. Imagine buying a drink that requires proof that you are over twenty-one. Normally you might show your entire ID, which exposes your birth date, address, and identification number. With a zero-knowledge proof, you could instead show a simple confirmation that this person is over twenty-one. Nothing else needs to be revealed. 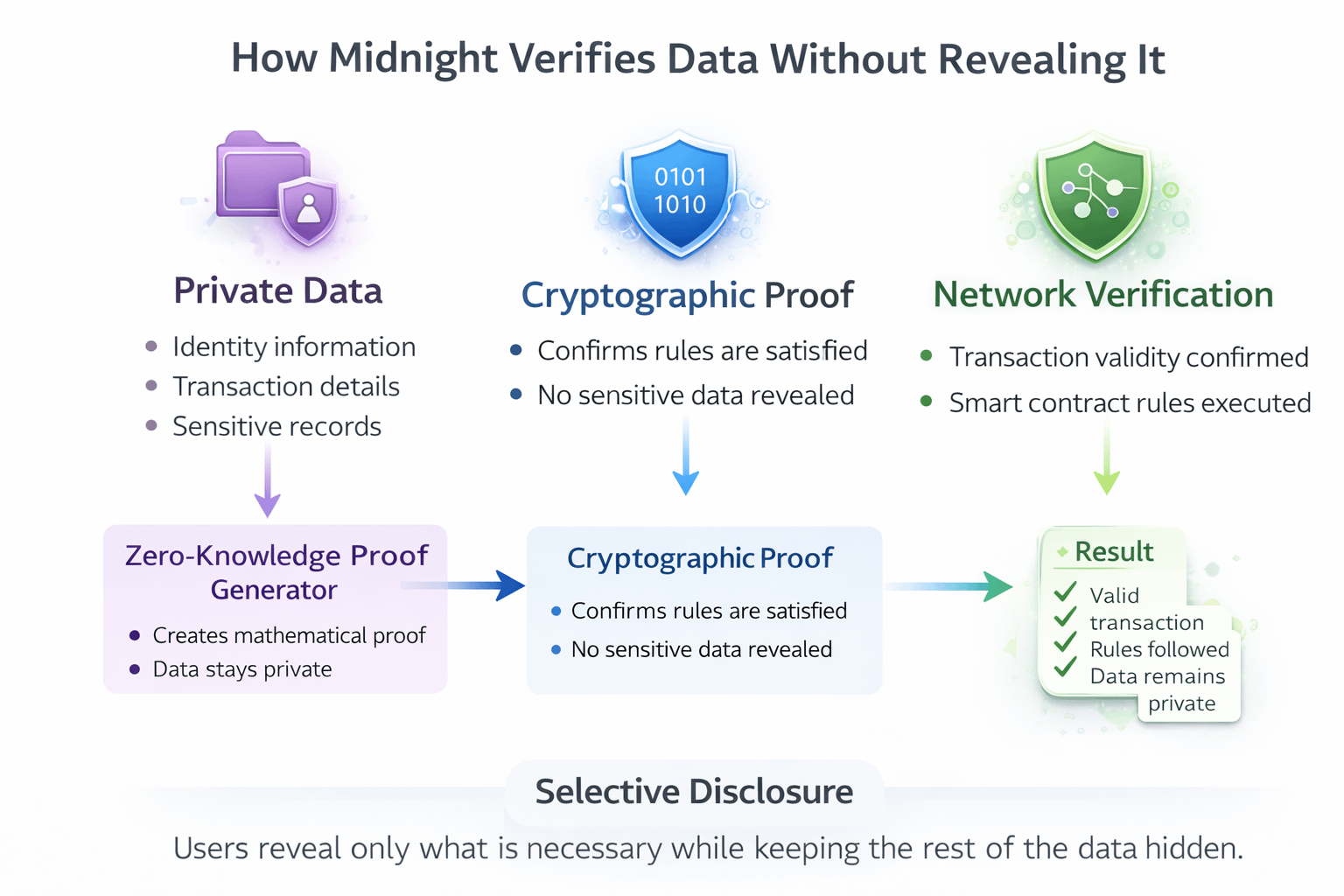 At a deeper level, the model changes how verification works. Verification moves from revealing data to verifying mathematical proofs. This allows something called selective disclosure. Users control what information they share, when they share it, and who receives the proof.
At a deeper level, the model changes how verification works. Verification moves from revealing data to verifying mathematical proofs. This allows something called selective disclosure. Users control what information they share, when they share it, and who receives the proof.
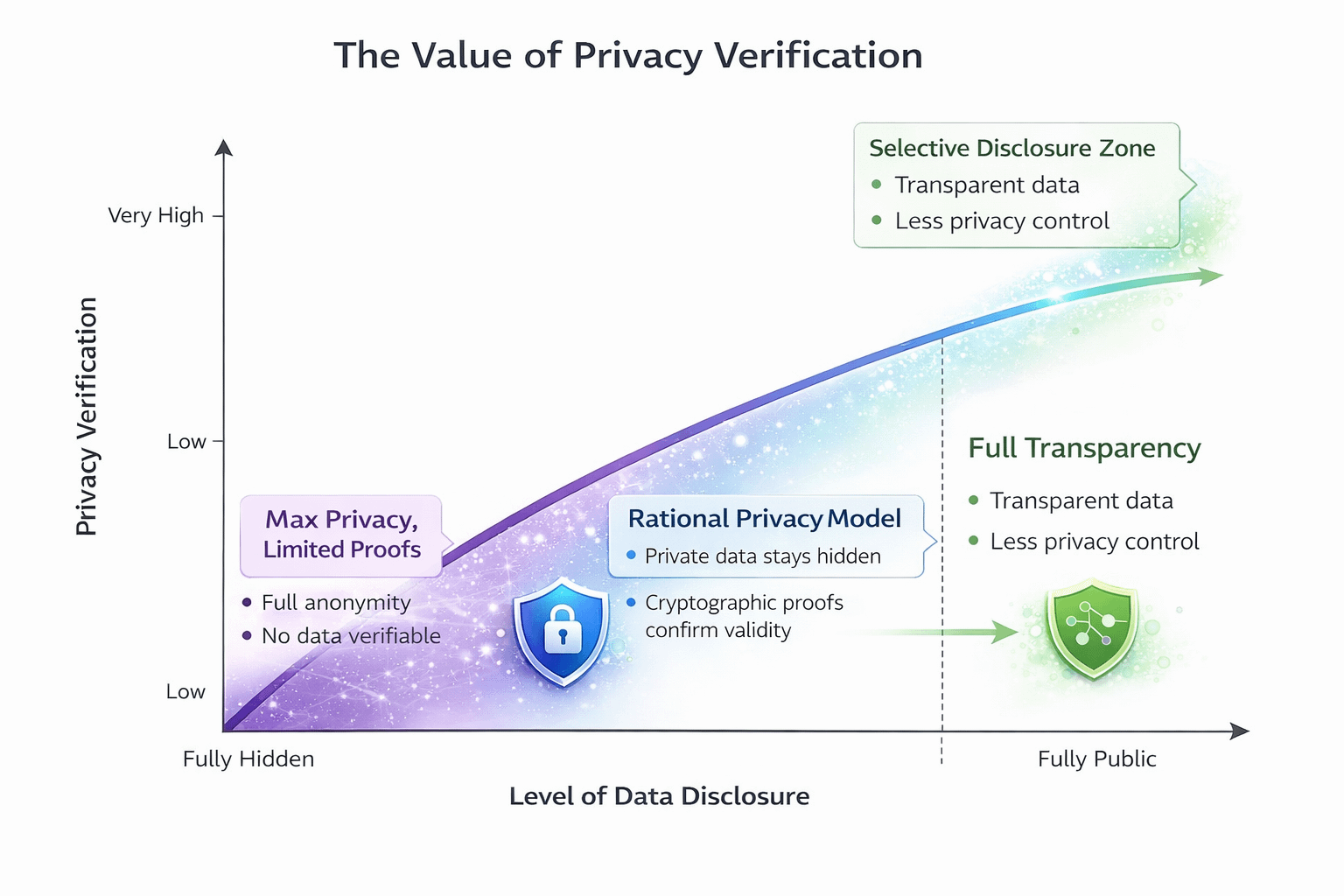
On public blockchains like Bitcoin or Ethereum, transactions are visible on public explorers. Midnight approaches this differently. Transaction data and smart-contract interactions can remain shielded by default while still allowing cryptographic proofs to verify that rules were followed. The project describes this idea as rational privacy. Unlike privacy-focused networks such as Monero, which aim for complete anonymity, Midnight focuses on enabling privacy while still allowing verifiable compliance when necessary. In other words, you can prove something is correct without revealing everything.
How Midnight Differs From Bitcoin | My dad’s next question was the classic one. “Is this like Bitcoin? Should I buy some?” That forced me to simplify the difference. Bitcoin functions primarily as a transparent ledger where every transaction is publicly visible. Midnight, by contrast, is designed as a smart-contract platform where applications can run while keeping user data private by default. Developers can build systems where sensitive information stays confidential while still allowing verifiable proofs when required.
 Early Use Case Exploration | Some early discussions around Midnight focus on industries where sensitive data must remain protected. Healthcare is one example. Systems often need to verify information across institutions while protecting patient records. According to discussions from the Midnight team, exploratory pilots have looked at ways cryptographic proofs could confirm medical information without exposing the underlying records. These examples are still developing, but they illustrate why privacy infrastructure might matter beyond traditional crypto use cases.
Early Use Case Exploration | Some early discussions around Midnight focus on industries where sensitive data must remain protected. Healthcare is one example. Systems often need to verify information across institutions while protecting patient records. According to discussions from the Midnight team, exploratory pilots have looked at ways cryptographic proofs could confirm medical information without exposing the underlying records. These examples are still developing, but they illustrate why privacy infrastructure might matter beyond traditional crypto use cases.
The Glacier Drop and Early Distribution Beyond its technology, Midnight also attracted attention through its distribution strategy. The project launched the Glacier Drop, a distribution event that reached tens of millions of wallets across multiple blockchain ecosystems. The distribution included participants from several networks and became one of the largest token distribution events in crypto. Millions of users also joined the Scavenger Mine phase, performing computational tasks to earn small allocations of the token. The goal was to distribute tokens broadly rather than concentrating them among early insiders.
 Potential Challenges | Despite the interesting design, Midnight still faces several challenges. The dual-token model may initially confuse new users compared to simpler single-token systems. The network also enters a competitive environment where many projects are experimenting with zero-knowledge technology and privacy infrastructure. Regulatory attitudes toward privacy technology in crypto may also influence adoption over time. Like any emerging blockchain platform, long-term success will likely depend on developer adoption and real-world applications.
Potential Challenges | Despite the interesting design, Midnight still faces several challenges. The dual-token model may initially confuse new users compared to simpler single-token systems. The network also enters a competitive environment where many projects are experimenting with zero-knowledge technology and privacy infrastructure. Regulatory attitudes toward privacy technology in crypto may also influence adoption over time. Like any emerging blockchain platform, long-term success will likely depend on developer adoption and real-world applications.
What I Learned From That Conversation Explaining something to someone outside crypto is one of the best ways to find gaps in your own understanding. My dad doesn’t care about cryptography or token economics. He just wants to know what something does and why it exists. His questions forced me to actually read the research instead of skimming headlines.
What I understand now is simpler than I expected. The two-token system separates long-term economic participation from everyday network usage. The privacy architecture allows people to prove information without exposing everything. But maybe the most interesting idea behind Midnight Network is something broader. For years the crypto world has treated transparency and privacy as opposites. The real innovation of Midnight may not be privacy alone, but proving that transparency and confidentiality can coexist in the same system.
@MidnightNetwork #night $COS $MBOX $NIGHT


